Derived from recommendations by leading security organizations, the Totem Top 10™ is our take on the 10 most important cybersecurity safeguards you should put in place right away. Whether you are pursuing NIST 800-171/CMMC compliance or are just looking to establish a cybersecurity program to reduce overall risk, the Totem Top 10™ provides you with the most relevant and cost-effective information to get started.
Our list contains safeguard descriptions, as well as helpful resources to assist you along the way. We have also included all corresponding NIST 800-171 controls that you can assess against as you implement each Totem Top 10™ safeguard.
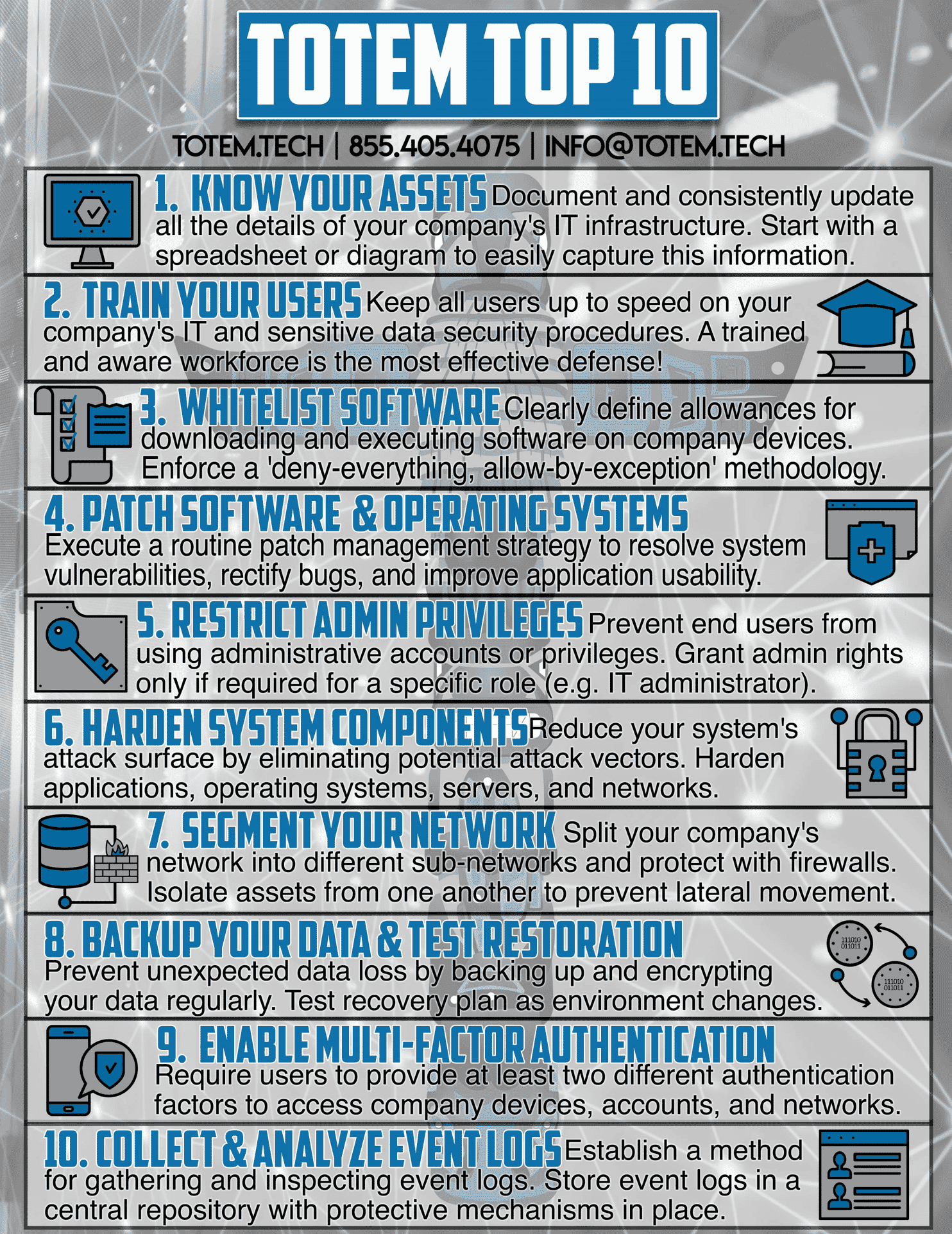
1. Know Your Assets
This is the first step to building a cybersecurity program. Perform an inventory of all your IT system assets, including your hardware, software, and system users, and understand their role in facilitating the flow of sensitive information throughout your environment. Be sure to update your inventory when assets are changed, added, or removed. You can’t protect what you don’t know exists!
Free Tools – CUI & System Inventory
Totem Blog – Know Your Assets: The first step in building a cybersecurity program
3.4.1, 3.4.3, 3.4.7, 3.4.9
2. Train Your Users
Simply put, a trained and aware workforce is your greatest defense against cyberattacks; even more than any technology in this list. Train your users to identify and prevent dangerous and common threats such as phishing, and look for ways that you can establish a cybersecurity culture within your organization.
Free Tools – IT Acceptable Use Policy Template, Computer Incident Response Aid Guide, Employee CUI Handling Guide Template
Totem Blog – The importance of cybersecurity user training in NIST 800-171
Totem Tech – Cybersecurity Training Capabilities (user and administrator training, phishing simulations, etc.)
3.2.1, 3.2.2, 3.2.3
3. Protect Your Endpoints
An endpoint is any device that is connected to and exchanges information with a network. Protect your endpoints from malware by using an Endpoint Detection & Response (EDR) or eXtended Detection & Response (XDR) solution. Consider a solution which offers a software whitelisting capability, where you can lock down your environment to only the software you approve to run.
Free Tools – CUI & System Inventory (Software Baseline)
Other – NIST SP 800-167, Windows AppLocker, Windows Software Restriction Policies, third-party whitelisting tool
3.4.8
4. Patch Software & Operating Systems
Old and outdated software and operating systems are a significant cybersecurity risk, because any associated vulnerabilities have already been identified and likely exploited. Establish a routine patching strategy to remediate these vulnerabilities. Apply automatic updates wherever possible, and run recurring vulnerability scans to ensure that patches are being adequately applied.
Free Tools – CUI & System Inventory (Software Baseline)
Other – NIST 800-40, Windows Group Policy, Tenable Nessus
3.11.3, 3.14.1, 3.14.4
5. Restrict Admin Privileges
Administrative privileges (also known as root or superuser privileges) grant a user practically unlimited control over a given system. These accounts are highly sought after by adversaries, as they make possible crippling attacks such as ransomware. Create a non-admin user account for all employees to operate full-time, and limit administrative privileges to only the IT staff who require them.
Free Tools – CUI & System Inventory (Duties & Responsibilities, Contact List), Separation of Duties Matrix
Totem Blog – Why is separation of duties required by NIST 800-171 and CMMC?
Other – Windows Active Directory, Windows User Account Control, third-party centralized account management tool
3.1.5, 3.1.6, 3.1.7, 3.1.15
6. Harden System Components
Each component within your IT system asset scope needs to be “hardened”. To harden a system component means to take it from its default (or current) vulnerable state and make it secure. For example, you can harden a router by disabling WEP and WPS or by resetting the administrator username and password. There are many different ways that a system could be hardened, which is why it is crucial to refer to an official security baseline when doing so.
Free Tools – CUI & System Inventory (Hardware Inventory)
Totem Blog – Password Policy Requirements for CMMC
Other – Microsoft Security Baselines, CIS Benchmarks
3.4.2
7. Segment Your Network
Operating on a “flat” network is akin to fighting on a flat battlefield. There are no obstacles, so an adversary can see everything and move in whichever direction they choose. You can prevent an adversary from moving around your network with impunity through segmentation. Divide your network into multiple pieces based on device type or function, and actively monitor your network for suspicious activity.
Free Tools – CUI & System Inventory (Hardware Inventory), SSP Introduction & SEPG
Totem Blog – What the Heck is a “Key Internal Boundary”?
3.1.16, 3.1.3, 3.13.1, 3.13.5
8. Backup Your Data & Test Restoration
Data backups are one of the simplest methods for protecting your business when something goes wrong. Once you have determined your recovery metrics and begun backing up your data, test your restoration plan to ensure that it will work when needed.
Free Tools – Incident Response Plan Template
Totem Blog – Six Steps to Include in Your Incident Response Plan
Totem Tech – NIST 800-171/CMMC Workshop (developing IRP, SSP, and POA&M)
3.8.9
9. Enable Multi-Factor Authentication
Multi-factor authentication (MFA) adds another layer of security to your networks, applications, or wherever else sensitive information may be stored. Require your users to provide at least two authentication factors (e.g., a password and an authenticator push notification) when accessing company networks, devices, and accounts.
Free Tools – CUI & System Inventory (Contact List, Interconnections Matrix)
Totem Blog – Understanding Multi-Factor Authentication
Totem Blog – Free Windows Multi-Factor Authentication for NIST/CMMC Compliance
3.5.3, 3.7.5
10. Collect & Analyze Event Logs
A “log” is simply a digital record of some computer event, whether that event be human or computer-initiated. Analyzing event logs and looking for anomalies can help you spot an adversary in your system before major damage is done. The most effective way to achieve this is to partner with a Managed Security Service Provider (MSSP), who would utilize a Security Incident and Event Management (SIEM) tool to actively monitor your collective network and alert you when suspicious activity is taking place.
Totem Blog – Empowering Cybersecurity Hunters for Small Businesses
Other – Windows Event Viewer, third-party MSSP and SIEM tech
3.3.1, 3.3.3, 3.3.4, 3.3.5, 3.3.6, 3.3.8, 3.3.9