Introduction
Since Totem offers cybersecurity empowerment services to small businesses, our goal is to show that they can supplement their existing cybersecurity tool suite with low-cost or free network monitoring solutions. We were excited when we heard that LogRhythm provides a free version of its NetMon product: LogRhythm NetMon Freemium. How could this tool could help small business’s network security analysts, “Hunters” as we call them, quickly baseline network traffic, identify anomalies, and pursue further investigation?
During July 2017, we received permission from a small business client to prototype NetMon Freemium on their internal network, and investigate the features of the tool. We’ve captured the results of our investigation in a whitepaper, available for download at the bottom of the blog. The rest of this blog is a synopsis of that whitepaper.
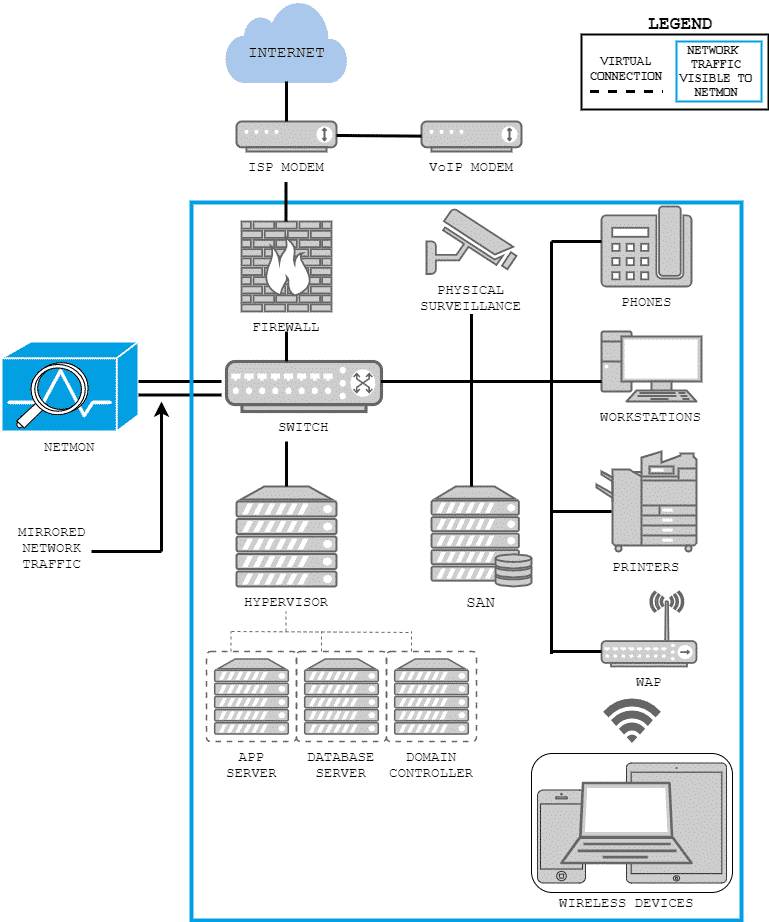
Target Network
The target network originates from a micro-small business, with fewer than 20 employees and workstations, and less than 25 Mbps traffic. The network hosts typical office devices, including phone, workstations, printers, internal application and database servers, and a local physical security system. We established NetMon Freemium’s scope of visibility as seen in Figure 1:
Integration and Test
NetMon Freemium provides out-of-the-box, browser-based interfaces containing an immense amount of network traffic data for a Hunter. It also allows the Hunter to adjust the front-end interface to suit his/her needs. For example, The “Analyze” user interface allows the following configurations:
- Ability to configure displayed data period over minutes, hours, days, weeks, and months
- Lucene queries on available detected Elasticsearch fields to filter captured traffic
- Metadata summaries of network flow sessions which include application path, IP addresses, MAC addresses
- Option to turn on packet capture for analyzed traffic flows
- Ability to download captured file and packet streams in PCAP format
- Replay functionality with PCAP formatted network
Alone, the ability to format and download PCAPs of traffic of interest makes NetMon Freemium a valuable tool for the Hunter; other free (and not-so-free) tools do not have this ability out of the box. Reducing a Hunter’s analysis time on a forensic task, such as file carving from a TCP stream is imperative for a small business with limited time resources.
Next we investigated the usefulness of the Kibana visualizations and dashboards within NetMon Freemium for baselining network traffic to facilitate identification of anomalies. We utilized the SANS Institute’s SANS DFIR Network Forensics and Analysis Poster (DFIR-Network_v1_4-17, available here for download with SANS account)
as a practical guide and ad hoc checklist for baselining network traffic. The explanations of analytical methods outlined in the “Network Traffic Anomalies” (NTA) section of the poster clarified what data and information we needed to display in visualizations and dashboards (Figure 2).
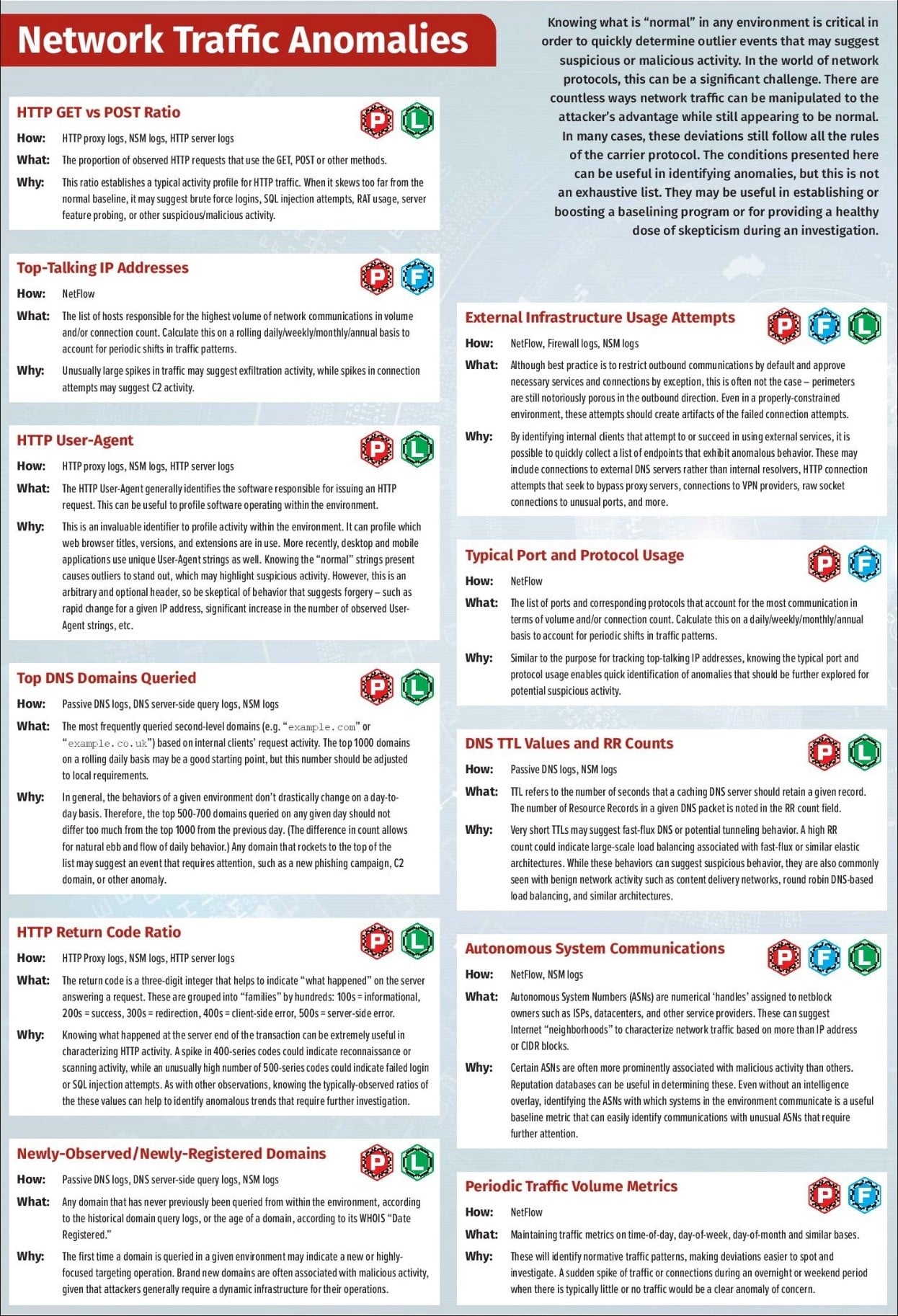
Figure 3 shows an example of a created Kibana dashboard based on an NTA. This dashboard contains visualizations to meet the “HTTP GET vs POST Ratio” and “HTTP Return Code Ratio” NTAs:
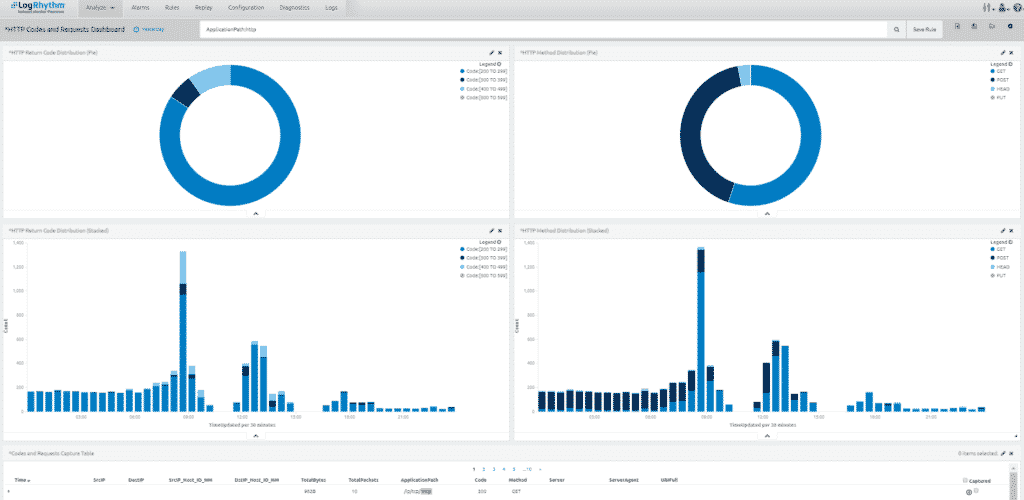
The table below outlines our ideas of how a Hunter would use the dashboard. The left-hand column describes baselining activities, and the right-hand column describes anomalies that would trigger a Hunter to investigate suspicious network activities.
| Over time, establish a baseline of: | Investigate further when: |
|---|---|
| Typical proportion(s) between HTTP methods | Observed ratio deviates from normal baseline |
| Typical proportion(s) among X00-series return codes | Observed frequency distribution displays one or multiple spikes in X00-series return codes |
Results of Evaluation
In the matrix below we evaluated how NetMon Freemium could help a small business Hunter analyze network traffic against each NTA. We used three criteria for the evaluation:
1) Ease of Implementation
How difficult was the implementation process for the visualizations?
- Easy: visualization exists out-of-the-box, only required simple re-configuration
- Moderate: required some novel development and re-configuration
- Challenging: could not create from the Visualize development environment, or may require significant development within the tool
2) Ease of Anomaly Detection
How quickly can the Hunter discover anomalies after establishing a baseline?
- At-a-glance: deviations are immediately apparent within the visualizations, at-a-glance
- Deeper look: deviations require cross-referencing with other organized information or more in-depth examination of visualizations and associated capture table to recognize oddities; for instance, a scroll through the chart legend may be required to spot deviations
3) Additional Tools Required?
- Yes: at least one other tool (Nmap, Wireshark, SIEM, firewall logs, etc.) is required
- No: out-of-the-box interfaces and drill down tools are sufficient
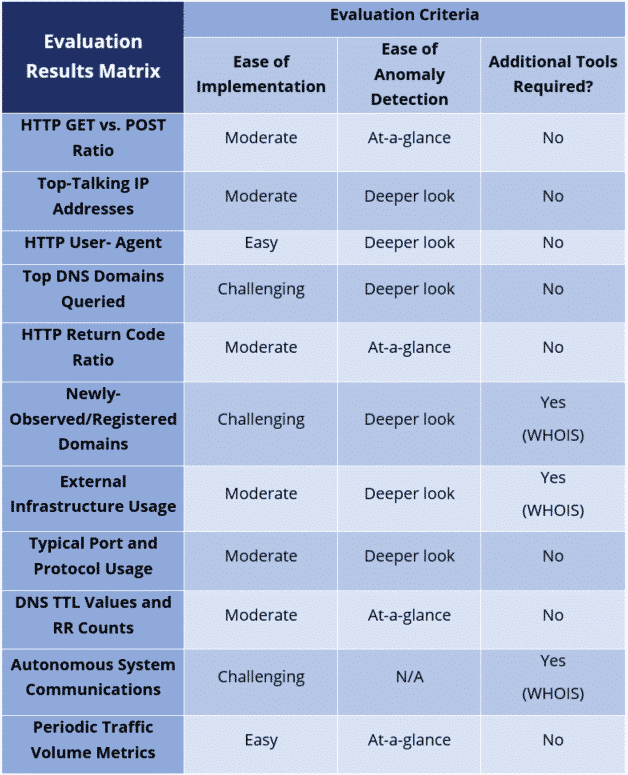
As the matrix shows, we are satisfied with NetMon Freemium as a low-cost addition to the cybersecurity toolkit for a small business Hunter. Free software can be a boon (with obvious exceptions: laden with spyware, not supported, etc.), and the cost of the necessary hardware was reasonable for a typical small business. The process to install and integrate the product into a small business’s network environment was painless.
The user interface and experience in NetMon Freemium are intuitive, and easily configurable for most of the NTAs we judged the tool against. We successfully created dashboards for 10 of the 11 Network Traffic Anomalies presented in the SANS poster. A couple of the NTAs were met by NetMon Freemium right out-of-the-box, and in short-order we were able to create novel dashboards that could help the small business Hunter identify other NTAs. The ability to drill down into a packet, flow, or PCAP within seconds of identifying an anomaly is of much value to a Hunter, and automatic packet capture of (all, if desired) traffic flows distinguishes NetMon Freemium from other tools. For several of the NTAs, NetMon Freemium would be the only tool the Hunter would need to identify an anomaly and determine the root cause.
However, it would be a mistake for a Hunter to rely solely on NetMon Freemium for network traffic monitoring, as the tool has limitations in meeting several of the NTAs, such as identifying external infrastructure attributes and usage attempts. The user interface needs improvements in some areas as well. For example, the main query interface has limitations, and users that are familiar with regular expression (RegEx) searches in scripting engines may become frustrated as they familiarize themselves with the Lucene syntax. Totem.Tech explored the Deep Packet Analysis Rules engine in the tool, which opened avenues for more in-depth analysis by a small business Hunter; however, manipulating these Lua scripts required a level of software programming or scripting expertise an average small business Hunter may not possess.
Once the tool has been installed and configured for the small business environment, we predict a small business Hunter would spend ½ hour to an hour or so a day using the dashboards to establish baselines of normal network traffic. Once the Hunter is comfortable with the baselines, he or she should be able to quickly spot anomalies during that same ½ hour period, and then use the tool to plan and execute further investigations.
Conclusion
LogRhythm’s NetMon Freemium is a valuable tool for someone hunting network traffic anomalies in a small business network, especially since the software is free. Although it has some front/backend limitations, it meets many industry best practices for network traffic analysis. It can certainly help the Hunter baseline network traffic, identify anomalies, and pursue further investigation.
Again, you can download the full whitepaper describing our investigation below. For more information on NetMon Freemium and to download it, visit LogRhythm’s landing page. We found the LogRhythm Community extremely helpful with deployment and configuration.
Good hunting!
–Adam Austin
Cybersecurity Lead
–Jim Lee
Cybersecurity Technician

