Totem™ CMMC Compliance Software
Built for CMMC.
Designed for you.
Totem™ is the trusted CMMC and NIST 800-171 compliance GRC software solution for defense contractors and their external service providers.

CMMC compliance is challenging.
We get that.
Totem is purposefully designed to help you:
Assess your CMMC implementation and track and report current scores
Quickly build an SSP, POA&M, SRM, and other required documentation
Prove your CMMC compliance to a C3PAO or other external auditor
Continuously monitor your CMMC compliance program long-term
View our interactive demo:
Built to ensure CMMC success. No fluff.
System Security Plan (SSP)
The core document of your CMMC compliance. Totem helps you build your SSP to satisfy the NIST SP 800-171A Assessment Objectives.
Plan of Action & Milestones (POA&M)
Your CMMC "get well plan". Totem helps you identify deficiencies and easily build Corrective Action Plans (CAP) for remediation.
SPRS Score Tracking
Totem dynamically calculates your compliance score, so you can track your progress as you go -- no manual calculations required.
Evidence Gathering
Totem serves as a single repository for all your CMMC evidence. Upload your artifacts or link to external evidence sources for streamlined assessment readiness.
Customizable Templates
Totem includes dozens of customizable CMMC compliance artifact templates, saving you hours of effort building your documentation from scratch.
Support You Can Trust
Gain access to our exclusive monthly Subscribers Q&A Forum, where we'll address your CMMC questions live. Totem also includes email compliance support.
Totem™ is ideal for:
Defense contractors and subcontractors facing CMMC compliance
External service providers assisting defense contractors with CMMC compliance
Government Industrial Base members assisting with CMMC (APEX, MEP, NCMA, SBDC)
Tired of paying for expensive consultants? Try CMMC Engaged.
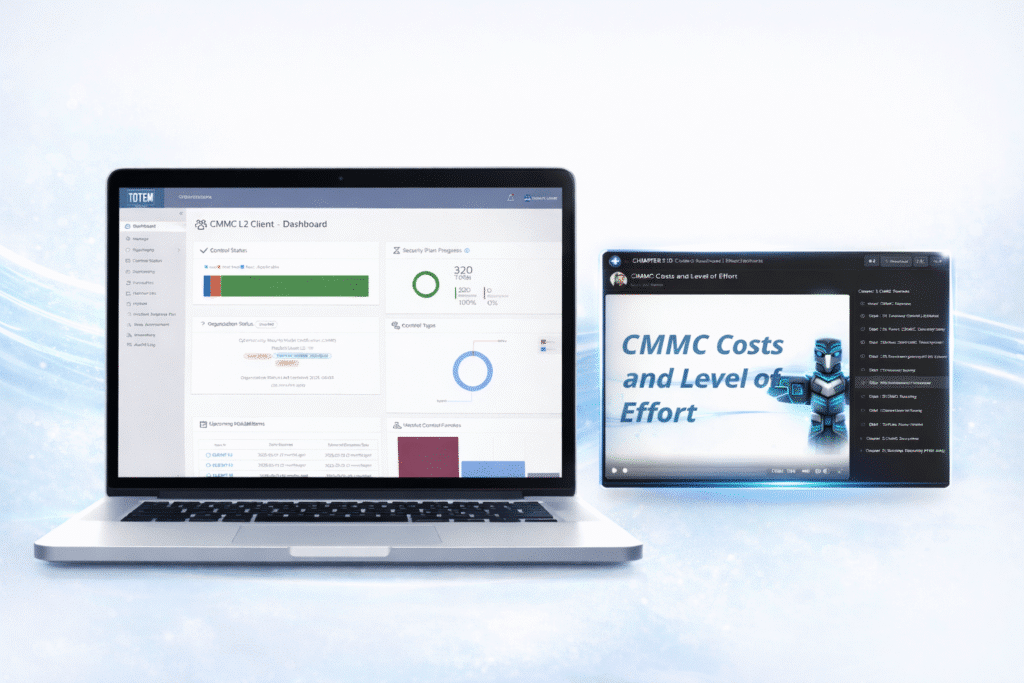
We’ve been training defense contractors and their service providers on CMMC compliance since 2020. With CMMC Engaged, you get Totem™, plus our proven CMMC training content, plus access to weekly consultations to discuss your unique challenges.
For unlimited users, all under a single subscription.
Transparent pricing. Unlimited users.
View monthly and annual pricing options.
Frequently Asked Questions
Aside from the CMMC compliance management tool and slew of templates, we host a monthly virtual CMMC Q&A Forum, exclusive to subscribers. These take place the first Thursday of the month, and you’ll receive an invite the week of. Here you can pre-submit your CMMC questions or get them answered live.
If you subscribe to the CMMC Engaged tier, your entire team will receive access to our full CMMC readiness training library, in addition to access to weekly consultation sessions to discuss whatever unique challenges you are facing.
Yes. Via the CMMC Expert tier, MSPs can procure their own “instance” of Totem, where they can manage all their clients in one place entirely under their control. Consider also applying to our Trusted Partner Program!
No. You may choose to purchase an annual subscription and save 10%, but we do not require any long-term contracts or commitments.
Yes. Totem supports the following:
- CMMC L1 (FAR 52.204-21)
- CMMC L2 (NIST SP 800-171 rev. 2)
- CMMC L3 (NIST SP 800-171 + NIST SP 800-172)
- NIST SP 800-171 rev. 3
- ISO/IEC 27001:2022
- HIPAA 405d
Yes! The Engaged subscription tier includes access to our full CMMC training portal. Check it out!
Yes! This is the basis of our SSP and POA&M generation workflows within Totem. Contact us if you need help.
Yes, Totem Technologies staff are available to answer any questions about use of the tool at no extra charge. In addition to a live support feature, our Support Center contains answers to many frequently asked questions: https://support.totem.tech/
Please see our Security Features page for a description of Totem’s security features.
Yes we do. Contact us to request this.
CMMC compliance starts with a plan.
See why Totem™ is the trusted CMMC planning GRC software solution.


