How to Know Your CMMC Scope
How much does CMMC cost, and how long is it going to take my company to comply? These are the two most frequently asked questions
How much does CMMC cost, and how long is it going to take my company to comply? These are the two most frequently asked questions
Government contractors handling technical or mission-related information during the performance of their contracts need to be cognizant of the National Institute of Standards and Technology

You’re a small business providing precision parts, advanced technologies, or other services to the Department of War (DoW — formerly Department of Defense). Maybe you’ve

If you’ve spent any amount of time digging through the NIST 800-171 cybersecurity requirements, you’ve likely thought to yourself, “what the heck does ______ mean?”

In this post, we highlight important considerations for achieving CMMC compliance in a Google Workspace environment.

US Department of Defense (DoD) contractors that handle Controlled Unclassified Information (CUI) are subject to the DoD’s Cybersecurity Maturity Model Certification (CMMC) Level 2 assessments.

Most Department of Defense (DoD) contractors, especially small businesses, rely on the help of External Service Providers (ESP) for their operational needs. Whether for day-to-day IT

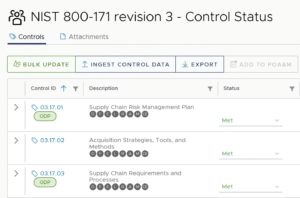
While Department of Defense (DoD) contractors implementing NIST 800-171 and pursuing a CMMC Level 2 certification will encounter many security controls that require careful interpretation,

For Department of Defense (DoD) contractors that are pursuing Cybersecurity Maturity Model Certification (CMMC) compliance, you may have heard recent buzz of “organization-defined parameters” (ODP)