We’ve been there. We can help.
We are a small business DoD contractor that must adhere to the same cybersecurity requirements and guidelines that you do.
We know that with the right approach, compliance is achievable even on the small business budget. Let us help your organization become compliant with the DFARS, NIST, CMMC, or HIPAA cybersecurity regulations.

Totem™ CMMC Compliance Software
Totem™ is the trusted CMMC and NIST 800-171 compliance documentation and planning solution for defense contractors and their external service providers.
HRDN-IT™ Single PC CMMC Enclave
HRDN-IT™ is the simple and affordable on-premise CUI enclave solution for small business defense contractors pursuing NIST 800-171 and CMMC Level 2 compliance.
Manage HRDN-IT™ yourself or let us manage it for you.
Perfect for small- and micro-businesses with minimal CUI-handling needs but still required to meet CMMC Level 2 and NIST 800-171.

CMMC Training
We provide affordable CMMC training geared towards DoD Contractors and their service providers.
Totem’s CMMC Level 1 or Level 2 training options will teach you what you need to know about the NIST SP 800-171 / CMMC cybersecurity requirements, including how you build your System Security Plan (SSP), Plan of Actions and Milestones (POA&M), and other compliance artifacts. We’ll give you the tools and support you need to sustain ongoing compliance.
Assessments
Let Totem do more of the heavy lifting.
Our cybersecurity experts will guide your organization through a full security gap assessment against cybersecurity control sets such as the NIST SP 800-171 and CMMC Level 2 standards.

Partner with Totem Technologies
If you’re an MSP, MSSP, vCISO, or Consultant helping your clients implement the NIST 800-171/CMMC security requirements, partnering with Totem Technologies can unlock discounts on our CMMC tooling and training solutions. Interested in learning more? Explore partnership below.
Latest News
How to Know Your CMMC Scope
How much does CMMC cost, and how long is it going to take my company to comply? These are the two most frequently asked questions
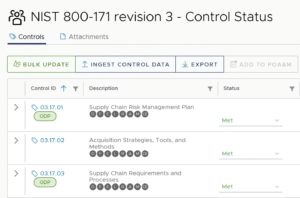
What the heck is NIST 800-171 revision 3?
Government contractors handling technical or mission-related information during the performance of their contracts need to be cognizant of the National Institute of Standards and Technology

A Small Business Guide to CMMC Compliance (2026)
You’re a small business providing precision parts, advanced technologies, or other services to the Department of War (DoW — formerly Department of Defense). Maybe you’ve


