We’ve made the assertion in our Totem Top 10 that, after you have gathered a complete inventory of all your IT system assets and identified the lifecycle of the sensitive information facilitated by those assets, the first thing you should do is begin training your users on what they can do to protect your business against cyber threats. The truth is that user training is your most effective weapon in this fight – even more powerful than a shiny new firewall or antivirus. NIST 800-171 – the DoD’s standard for cybersecurity compliance among small to medium-sized businesses (SMBs) within the Defense Industrial Base (DIB) that handle Controlled Unclassified Information (CUI) – has plenty to say about user training, and we will highlight our top takeaways on the matter in this blog.
Side note: we mention three free resources in this blog that you can download for free at the end or on our Free Tools page. Check ’em out!
User training: the magic bullet?
It doesn’t take long to find an advertisement from someone claiming that their cybersecurity product is the “magic bullet” for solving all your organization’s cybersecurity deficiencies. Unfortunately, these “solutions” tend to ignore the element of cybersecurity that should be at the forefront of our minds: user training. Human nature drives us towards “turnkey” solutions, while cybersecurity requires a significant defense-in-depth approach. Consequently, we pay exorbitant amounts for “quick and easy” yet only semi-helpful products.
What if we instead addressed cybersecurity deficiencies using a tiered approach, with a trained and informed workforce actively detecting and preventing threats, and technology being used as additional layers of defense? When user training becomes our “magic bullet”, we believe that we would see both the number of incidents as well as the amount of money spent on preventative technology greatly reduced.
For those of us required to comply with NIST 800-171, mandatory employee cybersecurity training requirements can be found across nearly every control family. User training is not the only element in a mature cybersecurity program, as NIST 800-171 also requires implementation of a wide array of different technologies, including whitelisting, multifactor authentication, data backups, event log analysis, and others. However, when we view these technologies through the lens of user training, we can protect ourselves from falling into the trap that they can be employed in “fire-and-forget” fashion.
NIST 800-171 requirements for user training
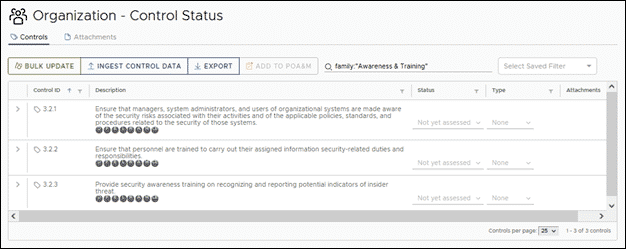
Now that we have cleared up the fog and ascertained user training’s place in your organization, we can turn our attention to NIST 800-171’s training requirements. The framework has quite a bit to say about user training, as it has been given its own family (Awareness & Training), with three controls and nine affiliated organizational actions total. The control identifiers as well as their descriptions are seen below:
Control 3.2.1 requires you to train your users on the security risks associated with their various organizational activities. Although the emphasis here is on protecting CUI, the security risks for all business processes ought to be trained on just as activities involving CUI. Furthermore, just because a security risk may not seem directly connected to CUI does not mean it is completely unassociated. For example, phishing is the . Although CUI does not typically come to mind when you think of phishing, an adversary may use a phishing attack to gain a foothold on your network and proceed to seek out and compromise sensitive information including CUI. So, we have a responsibility to train our users on identifying and preventing phishing attacks. This means that we must take a comprehensive approach when putting together our user training and risk management plans, and develop policies and procedures that encompass more than just surface-level CUI protection.
Control 3.2.2 requires you to identify the specific information security-related roles within your organization, to define the responsibilities of these individuals, and to train them to carry out their assigned duties. One of the most significant failures we’ve seen when it comes to this control is when an organization places the entirety of the information security responsibilities upon the shoulders of their IT team. These individuals certainly have a significant role to play in cybersecurity, but they cannot always be there to prevent an executive from clicking on a phishing link or a warehouse worker from allowing a fake UPS associate into the building. Responding to cyber threats is a responsibility of everyone top to bottom, so be conscientious when implementing this control. By training your users, your organization can help turn one of your most vulnerable assets (human users) into a proactive detection device!
Control 3.2.3 is more focused than the previous controls, as it requires users to be trained on recognizing and reporting potential indicators of an insider threat. An insider threat is an individual within an organization that uses their authorized access to cause harm to the organization, either intentionally or unintentionally. Without the proper training in place, these attacks can become nearly impossible to detect until the damage has been done. Oh, and the damages can be astronomical. In 2020, the Ponemon Institute reported that the average cost of an insider threat event was around $11.5 million. For attacks that took longer than 90 days to contain, the average cost rose to around $13.7 million. How many small businesses within the DoD supply chain would be able to overcome the repercussions of such an attack? Not very many.
Additionally, an insider threat would be a particularly interesting attack vector for DIB adversaries, because they typically will have easy access to CUI and may remain undetected for a significant period of time. Given this, we strongly recommend training ALL of your users on the DoD’s list of indicators of an insider threat:
- inordinate, long-term job dissatisfaction;
- attempts to gain access to information that is not required for job performance;
- unusual work hours;
- unexpected significant transfers of data;
- suspicious contacts;
- concerning behaviors outside the workplace;
- unexplained access to financial resources;
- bullying or sexual harassment of fellow employees;
- workplace violence;
- repeated and other serious violations of organizational policies, procedures, directives, rules, or practices.
Tools to build a compliant cybersecurity program
It’s tough to know where to even begin with cybersecurity user training. We have put together a handful of free resources to assist you in this endeavor:
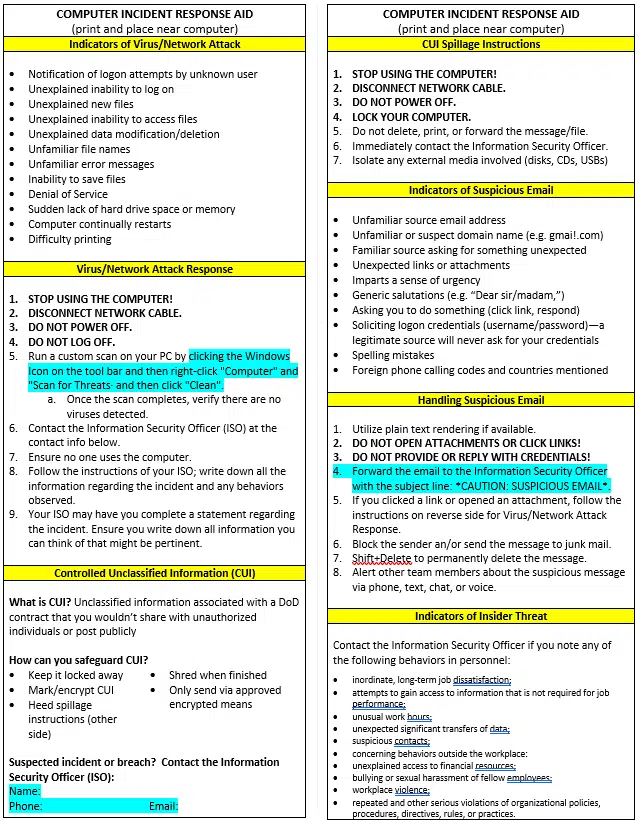
Computer Incident Response Aid
Our Computer Incident Response Aid (CIRA) is a convenient guide that your employees can keep on their desks and refer to in the event of a computer-related incident. The guide details clear instructions for what your users should do to help with the initial “fire-fighting” when an incident occurs. Included in this guide are recommendations covering several different potential incidents, including:
- indicators of virus/network attacks
- virus/network attack response
- Controlled Unclassified Information (CUI)
- CUI spillage instructions
- indicators of suspicious email
- handling suspicious email
- indicators of insider threat
You can customize the CIRA to include contact information for your organization’s Information Security Officer (ISO).
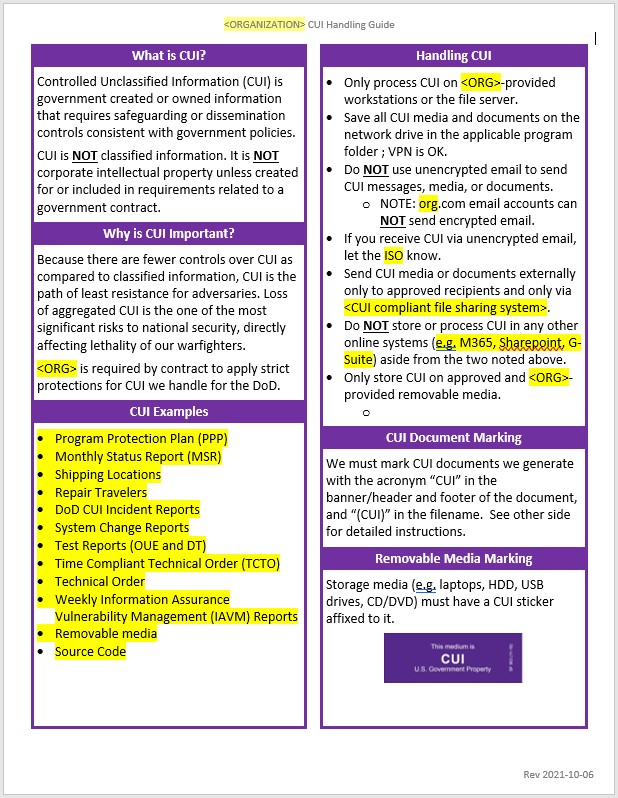
CUI Handling Guide
The DoD Instruction 5200.48 lays out specific requirements for “authorized holders” of CUI. We are, as members of the DIB, authorized holders of CUI. If your organization handles CUI, you will want to be certain that your users are trained to properly process, store, and transmit this sensitive information. We created our CUI Handling Guide Template to assist you with this. We have the guide printed back and front on card stock and every employee in the company has received a copy of the guide. Additionally, we dedicate a portion of our cybersecurity awareness training program to instructing employees on the contents and use of the guide.
The first page provides a quick definition of CUI and why it’s important to protect it. This helps establish a rationale for the guide, and motivation for employees to abide it. We then list the CUI documents and media (what we call “CUI Elements”) in our environment so employees know exactly what they might handle that contains CUI. It then goes on to list several high-level procedures employees are expected to execute when handling CUI.
The second page consists of instructions for appropriately marking CUI. This includes marking removable media with CUI stickers, and documents with “CUI” in the header and footer in accordance with DoD requirements. We also direct our users’ attention to the other side of the document for specifics on the “Designation Indicator” that must be included on the first page of any document containing CUI. For a more detailed walkthrough of this template, please see our CUI Handling Guide blog.
Acceptable Use Policy Template
Developing an IT Acceptable Use Policy is one of the first steps to take when building your cybersecurity program, and it is required by NIST 800-171 (3.2.1[d]). We developed our AUP Template to assist you with creating this document and provide a framework that your users must agree to abide by. The document includes several different security and privacy responsibilities, including:
- secure identification, authentication, and accountability
- secure communications
- secure devices
- secure remote work
- secure general use
When cybersecurity awareness training rolls around again, we strongly recommend you spend some time reviewing this document with your users and ensure their continual commitment to abide by the policies described.
Finishing up
We certainly don’t want to overwhelm you with information, but the grim reality is that businesses that ignore or underestimate cybersecurity user training are more likely to find themselves at the mercy of an adversary. To comply with NIST 800-171, cybersecurity user training must be baked into your everyday business processes. We have gotten you started with some tools to help you accomplish this as you weave your way towards compliance.
Keep in mind that none of this is particularly difficult to achieve – it just takes time. Give yourselves some time to enjoy the journey and do things the right way.
If you have any questions on anything we have discussed in this blog, please get in touch with us, or jump into one of our Workshops. We love talking about all of this!
Keep fighting the good fight!
— Nathan Cross, Cybersecurity Engineer