Cybersecurity Risk Assessment Within the Defense Industrial Base
Risk management is a part of business. Although the level of risk companies face depends upon a multitude of different factors, the truth is that small businesses must be especially careful when handling risk. If your company operates within the Defense Industrial Base (DIB), you likely understand this firsthand. Not only must you perform with fewer resources which leave you with little room for error, but the target placed on your back by cyberthreats is larger than those outside the DIB, given that you likely process sensitive information such as Controlled Unclassified Information (CUI). As a result, your need for an effective cybersecurity risk management strategy is a top priority. This blog will help differentiate between a handful of cybersecurity risk assessment methodologies and highlight several relevant tools that you can use to conduct a cybersecurity risk assessment for your own small business. If you are interested in reading more about Totem’s approach to cybersecurity risk assessment, you can grab a free copy of our eBook at the end of this blog.
Totem's Assumed Risk™ Assessment Methodology
We’ll kick off our list with an analysis of how small businesses tend to conduct their cybersecurity risk assessments. We’ve found that most occur in the following manner:
- An asset inventory list of all things of value to the organization is created. This will typically include users, intellectual property, customer information, IT components, facilities, and others. (Side note: Knowing your assets should always be the first safeguard implemented, as we encourage in our Totem Top 10.)
- A list of vulnerabilities associated with each of those assets is created. For example, untrained users are susceptible to social engineering attacks.
- A list of threats the organization faces is created. This could be a natural threat such as an earthquake, an environmental threat such as a fire, or a human threat such as social engineering or fraud.
- The threats are inserted into a matrix and the likelihood that an identified threat exploits a defined vulnerability is determined.
- In a separate matrix, risk is computed according to a pre-defined risk equation. For example, low probability x high impact = moderate risk.
We certainly are not discouraging this approach to cybersecurity risk management, but we do want to point out that this approach can be more challenging for small businesses to implement for two primary reasons:
- First, small businesses lack a process to identify vulnerabilities (Step 2).
- Second, small businesses do not have the expertise or tools to determine specific threats (Step 3).
This is where Totem’s “Assumed Risk”™ assessment method comes into play. Contrary to the risk assessment methodology we previously outlined, this approach focuses primarily on assumed risk, threat event outcome, and layers of currently employed mitigations. Applying this method would look something like this:
- Categories of assets – asset classes – of things of value to the organization are developed. This includes users, customer information, workstations, servers, facilities, and others. (Again, we maintain that knowing your assets must always be first.)
- A standard list of possible threat event outcomes should any threat source exploit any vulnerability is established. This list includes the following:
- Social Engineering
- Unauthorized access to data or system
- Unauthorized use of data or system
- Unauthorized disclosure of data
- Disruption of data or system availability
- Unauthorized modification of data or system
- Unauthorized destruction/loss of data or system
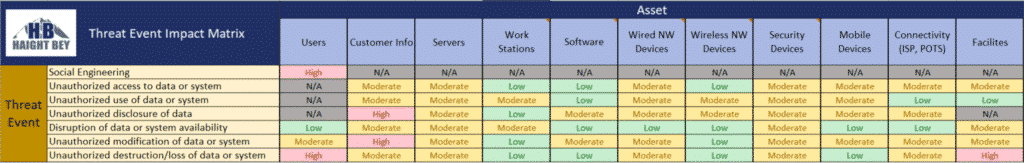
- Each asset class is placed into a matrix. The impact to each asset class is determined – whether high, moderate, or low (or however your organization chooses to define this) should each threat event outcome affect that asset class. Keep in mind that the impact of the event types on the asset is “assumed” to be the risk – meaning that if we identify a high impact event, it automatically becomes high risk, until we can execute Step 4 and identify mitigations we already have in place.
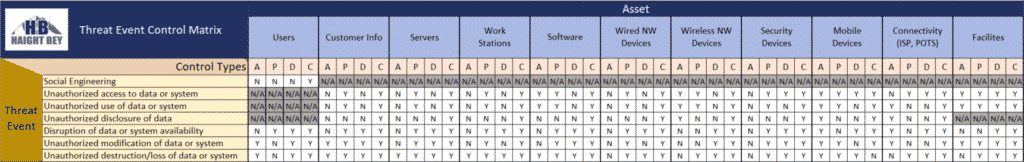
- Now that we know our assumed risk, we can begin identifying mitigations to drive down this risk. This is different from the average risk assessment methodology, because instead of identifying mitigations first and risk second, we work backwards, identifying risk first then the mitigations we will use to reduce our risk. In a separate matrix, the control types implemented to mitigate the vulnerabilities or threat for each threat event outcome are determined. There are four control types that could be implemented:
- Avertive: Warning banners, honeypots, acceptable use policy, user training
- Preventative: Access control enforcement, encryption, strong authentication
- Detective: Audit trails, intrusion detection systems, checksums, honeypots
- Corrective: Incident Response/Contingency plans, backup & restore procedures, redundancy
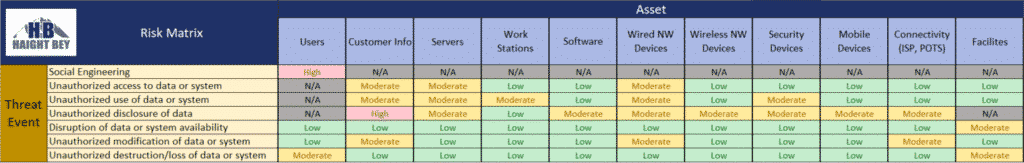
- In a separate matrix, impact and existing controls implemented are combined to determine risk according to the organization’s pre-determined risk equation. For example, three control types implemented x high impact = moderate risk. The risk level defaults to the impact level unless control type implementation threshold is reached (assumed risk).
The screenshots below are examples of our “assumed risk” cybersecurity risk assessment template for steps 3-5:
If you would like to download a copy of Totem’s “Assumed Risk”™ cybersecurity risk assessment template, you can do that here.
Center for Internet Security Risk Assessment Method (CIS RAM)
The second cybersecurity risk assessment methodology we will highlight is the Center for Internet Security (CIS) Risk Assessment Method (RAM). The CIS RAM is used to evaluate an organization’s implementation of the CIS Controls (CIS Version 8 is the most recent at the time of this writing), enabling the organization to conduct risk assessments according to how they have chosen to implement these CIS safeguards. The CIS RAM contains a variety of different templates, examples, and exercises to help simplify the risk assessment process.
As laid out in detail in the references mentioned above, the CIS RAM’s risk assessment process has two core components, each with their own subcomponents. Their methodology looks something like this:
- Risk Observation
- Identify company assets and owners of assets
- Identify how your organization defines risk and when it will/will not accept risk
- Review current safeguards in place
- Evaluate effectiveness of safeguards in place against potential threats
- Using likelihood and impact of a potential security incident, calculate a risk score, and determine if this risk is acceptable
- Risk Mitigation
- Identify additional safeguards that can be used to bring down unacceptable risk
- Evaluate effectiveness of additional safeguards
These components are evaluated differently depending upon the organizational maturity “tier” that your company falls under (Tier 1 being the least mature, Tiers 3 & 4 being the most mature). CIS has created a free CIS RAM workbook template that you can request alongside the CIS RAM documentation. This template is tied directly to the CIS RAM documentation, so you can use the workbook as your own tool for tracking and evaluating your progress with implementing the CIS Controls for your designated tier.
There’s plenty more we could discuss about CIS RAM, but this is a good starting point if your organization implements or chooses to implement the CIS Controls framework.
Factor Analysis of Information Risk (FAIR) Method
The Factor Analysis of Information Risk (FAIR) Institute has been one of the pioneers in advancing a standard cybersecurity risk assessment framework. Its development of the FAIR cyber risk framework has helped make information regarding cybersecurity risk management more accessible for security professionals across the world. By becoming a member of the FAIR Institute, you can even stay up to date on all the latest risk management best practices that FAIR recommends.
One of the core teachings of FAIR is that risk is uncertain, and therefore organizations should focus on the probability of a given event occurring before making a decision. What hopefully comes to mind when you read this is that risk is not assumed. We’ve already addressed the implications of a risk model based on probabilities instead of assumptions through our analysis of Totem’s “Assumed Risk”™ assessment methodology, so we won’t go into any more detail on that here. However, it is important to understand that probability is the key to a FAIR risk analysis.
FAIR defines risk as: “the probable frequency and probable magnitude of future loss.” FAIR explains that in order for risk to truly be measured during a given scenario, a series of steps must take place first.
- Definition: Define the risks
- Measurement: Measure the risks
- Comparison: Compare the risks to past, present, and future risks
- Informed Decision: Make informed decisions about risks
- More Effective Management: Management of risks is more effective because of the previous steps
Once an organization is certain about how they define risks and how this applies to their assets, it’s time for them to get to work applying the FAIR risk assessment methodology. Here is a basic overview of this methodology:
- Stage 1: Identify scenario components
- Identify the asset at risk
- Identify the threat community under consideration
- Stage 2: Evaluate Loss Event Frequency (LEF):
- Estimate the probably Threat Event Frequency (TEF)
- Estimate the Threat Capability (TCAP)
- Estimate Control Strength (CS)
- Derive Vulnerability (Vuln)
- Derive Loss Event Frequency (LEF)
- Stage 3: Evaluate Probably Loss Magnitude (PLM)
- Estimate worst-case loss
- Estimate probable loss
- Stage 4: Derive and articulate risk
- Derive and articulate risk
Without having studied in-depth the FAIR framework, this is likely more difficult to understand in theory. Check out this flowchart that sums it all up nicely.
As you can see, according to FAIR, risk starts and ends with probability. Leveraging analytics to determine risk can give your organization a considerable advantage, but this requires significant time and effort to tightly define, and it may require some “guessing”. Overall, the framework has proven to be successful over the years and should be considered by your organization. If you want to learn more about the various tools and resources offered by FAIR, check them out here.
Other Risk Assessment Tools
The number of resources your small business can use to conduct risk assessments are seemingly endless. Here are a couple more tools that we’ve found which may come in handy for you:
- Centers for Medicare & Medicaid Services (CMS) Information System Risk Assessment Template
- FedRAMP Risk Exposure Template
As there are so many different Risk Assessment tools and approaches out there, you may be wondering where to start. We designed our Totem Assumed Risk™ assessment methodology as an “entry level” into small business cybersecurity risk assessments. So, if you’re not sure, start with our methodology. And come join us in our monthly Workshops, where we discuss small business risk assessment and mitigation!
Don’t forget to check out our free eBook below, where we talk all about Totem’s approach to risk management. We’ve got our fellow DIB members in mind with this one!
Good luck out there!
-Nathan Cross, Cybersecurity Engineer



