UPDATE 27 November 2024: we’ve updated this post on small business cybersecurity risk assessments to include a description of our “Assumed Risk” assessment methodology as incorporated into our Totem™ Cybersecurity Compliance Management tool. You can request a free trial of this tool here. Alternatively, you can still download a legacy (not updated) spreadsheet version of our methodology from the bottom of this post.
How do small businesses commonly execute cybersecurity risk assessments?
A small business qualitative cybersecurity risk assessment typically goes something like this:
- Develop a list of things of value to the organization such as users, intellectual property, customer info, IT components, facilities, etc. We call these things “assets”.
- Develop a list of vulnerabilities associated with those assets, especially in user and IT component assets. For example, users are susceptible to social engineering, and a vulnerability scan on IT components will undoubtedly turn up missing patches and insecure configurations.
- Develop a list of threats the organization faces, such as social engineering, loss/theft, hacking, etc.
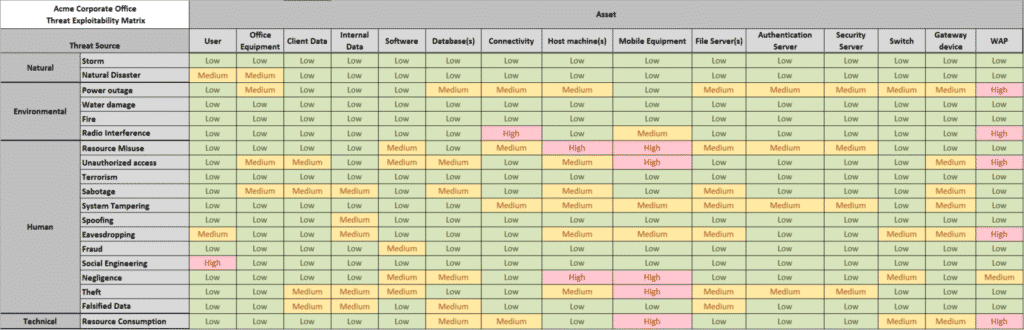
- In a matrix, iterate through each threat and determine the probability of that threat exploiting each vulnerability.
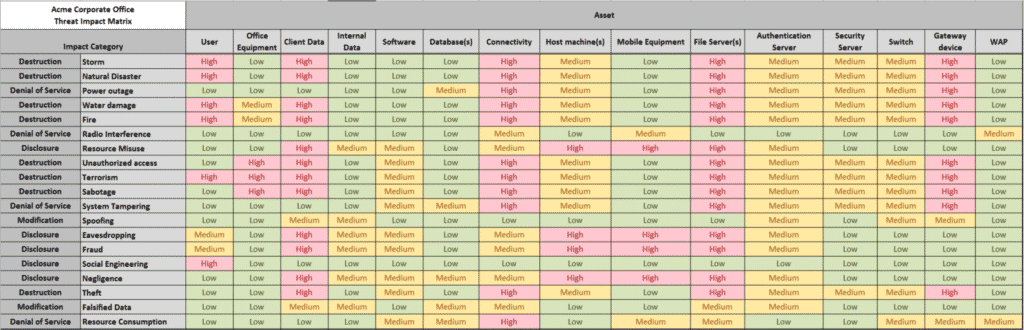
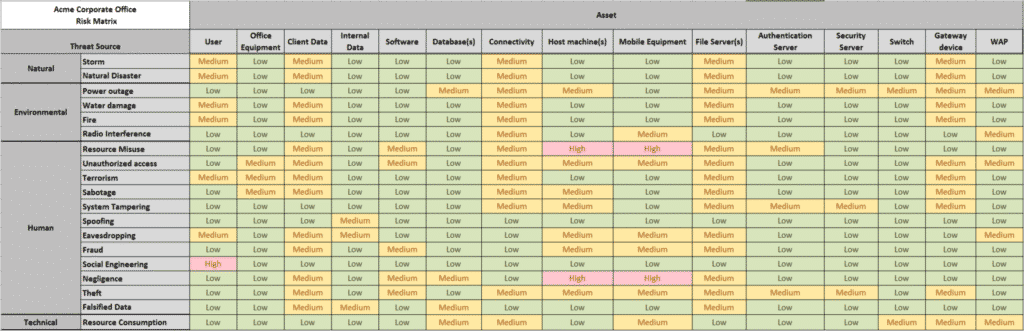
- In a separate matrix, combine probability and impact to determine risk, according to some algorithm, e.g. low probability x high impact = moderate risk.
The screenshots below are from a cybersecurity risk assessment template and show the results of a steps 4-6 of a typical cybersecurity risk assessment exercise, done with the most common tool for executing risk assessments: a spreadsheet.
However, for most small businesses, steps 2 and 3 in this cybersecurity risk assessment template are a significant challenge because:
- The business lacks a process to identify vulnerabilities, and
- The business does not have the expertise or tools to conduct a threat modeling exercise to determine specific threats.
An "Assumed Risk" approach for your cybersecurity risk assessment
- Therefore, we’d like to present a different, “entry-level” approach for small business cybersecurity risk assessment based on assumed risk, threat event outcome, and layers of currently employed mitigations. In this approach, the cybersecurity risk assessment goes something like this:
- Develop categories of things of value to the organization—asset classes—such as users, customer info, workstations, servers, facilities, etc.
- Utilize a standard list of possible threat event outcomes should any threat source exploit any vulnerability. This list includes the following:
- Social Engineering
- Unauthorized access to data or system
- Unauthorized use of data or system
- Unauthorized disclosure of data
- Disruption of data or system availability
- Unauthorized modification of data or system
- Unauthorized destruction/loss of data or system
- In a matrix, iterate through each asset class and determine the impact to the organization—high, moderate, or low (or some finer granularity, if desired)—should each threat event outcome affect that asset class.
- In a matrix, iterate through each asset class and determine what control types are implemented to mitigate the vulnerabilities or threat for each threat event outcome. There are four control types that could possibly be implemented:
- Avertive: Warning banners, honeypots, acceptable use policy, user training
- Preventive: Access control enforcement, encryption, strong authentication
- Detective: Audit trails, intrusion detection systems, checksums, honeypots
- Corrective: Incident Response/Contingency plans, backup restore procedures, redundancy
- In a separate matrix, combine impact and existing control implementation, to determine risk, according to some algorithm, e.g. three control types implemented x high impact = moderate risk. Risk level defaults to impact level, unless control type implementation threshold is reached (assumed risk).
Benefits of the "Assumed Risk" approach
This is a much simpler and less daunting approach to a cybersecurity risk assessment and will encourage the practice amongst small businesses, because:
- Most small business executives and administrators have a good sense of the impact to the business as well as the controls and mitigations they current have in place, so steps 4 and 5 are much more palatable, and,
- The threat events and control types are pre-determined for the business, so vulnerability assessment and threat modeling are unnecessary.
The algorithm for determining cyber risk assumes that each organizational asset class is at risk for each threat event and incorporates an understanding that the organization must utilize a defense-in-depth approach to lower risk. Hence, to lower the risk score, the calculation requires multiple different types of controls to be implemented for each asset class against each threat event outcome. In the calculation example given in step 5, if fewer than three control types were implemented, the algorithm would default the risk value to the impact value, in this case “high”. The organization could actually tweak the algorithm to suit its risk appetite, for example:
- tweak the parameters based on its risk appetite, e.g. two controls types vs. three required to mitigate risk down one level
- change the algorithm to calculate “low” risk for asset classes protected by all four control types
Our cybersecurity risk assessment module can be utilized by organizations just beginning their cybersecurity program. As the organizational cybersecurity program matures, the organization can undertake more sophisticated cybersecurity risk assessments. The key is to get the organization in the habit of performing cybersecurity risk assessments so they can prioritize risks to mitigate.
The screen shot below shows our “Assumed Risk” cybersecurity risk assessment module interface as used to perform methodology steps 3-5, for the risk of unauthorized disclosure of protected information:
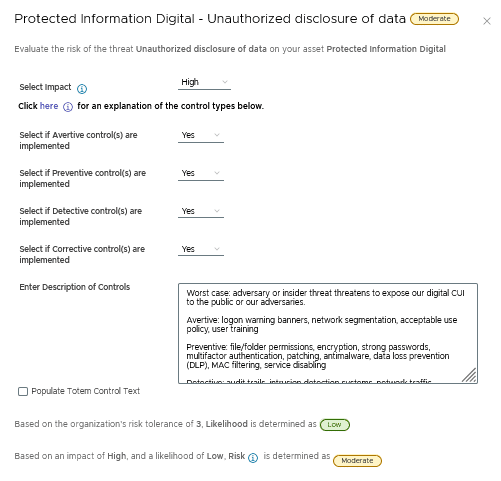
Working from top to bottom in this image, you can see we’ve selected a “High” impact for this risk, since if our protected information were disclosed to an adversary, it could have catastrophic consequences for this small business.
Next we selected “Yes” for each of the four types of controls, to indicate with have at least one of each type of controls (mitigations) in place. The “Description of Controls” text field below those selections shows that we’ve identified the specific mitigations this small business has in place that help counter the threat of unauthorized disclosure.
The rest of the risk calculation is up to the methodology built into the tool, and the “risk appetite” selected for this small business. Since we selected “Yes” for each of the four control types, the tool calculates the overall liklihood as “Low”, and adjusts the overall risk score down from “High” to “Moderate”.
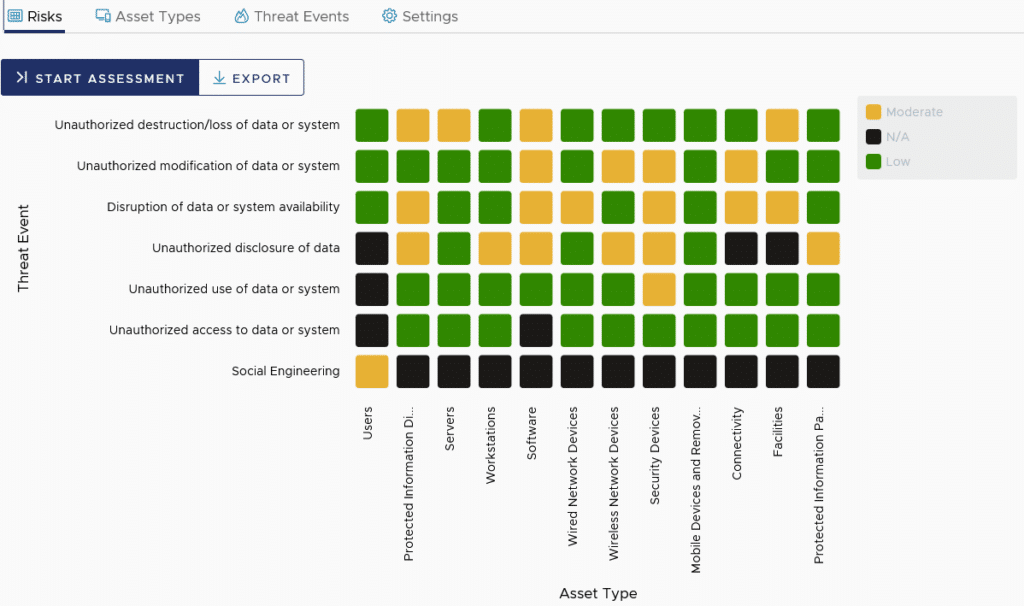
The screen shot below shows the overall risk matrix — or “heat map” — for this particular small business, once all risks have been assessed. The goal of the business would be 1) to ensure there are no High risks (which would have shown as red squares on this matrix), and 2) to strive to drive down all Moderate (yellow) risks to Low (green), as feasible.
Wrapping up
So there you have it: an explanation of an “entry-level” cybersecurity risk assessment methodology, and a demonstration of the tool that can be leveraged to complete the assessment. Those of us that handle Controlled Unclassified Information (CUI) on Federal government contracts are actually required by the NIST 800-171 standard to perform such risk assessments at least annually, so we’ll need some tools to help us.
If you’d like a free trial of the Totem™ CCM tool, which incorporates the “Assumed Risk” assessment methodology described in this post, contact us.
We also offer a legacy (not updated) spreadsheet which incorporates this “Assumed Risk” assessment methodology, which you can download using the form below.
Good Hunting!
–Adam



