Background on the CMMC requirement to separate the duties of individuals
Members of the DoD supply chain – the Defense Industrial Base (DIB) — that handle Controlled Unclassified Information (CUI) are required to implement the cybersecurity safeguards in the National Institutes of Standards and Technology (NIST) Special Publication 800-171. These contractors also must eventually be certified under the DoD Cybersecurity Maturity Model Certification (CMMC) at least Level 2. In NIST 800-171 and CMMC L2 there is a requirement (AC.L2-3.1.4) to “Separate the duties of individuals to reduce the risk of malevolent activity without collusion.”
What does it mean to separate the duties of individuals, why is this a requirement, and how do DIB members – especially small business contractors – effectively implement this safeguard? This post will provide answers to those questions as well as a downloadable worksheet that organizations can use to plan and demonstrate separation of duties.
What does separation of duties mean?
According to NIST, separation of duties:
refers to the principle that no user should be given enough privileges to misuse the system on their own.
Essentially, to separate the duties means making sure no one individual has access to all the “keys to the kingdom”. And the wording of the safeguard emphasizes that theme with the statement that separation of duties reduces the risk of bad behavior “without collusion.” In other words, two or more individuals would have to team up to perpetrate cyber mischief in the organization.
Why is this a requirement?
Continuing with NIST definitions, separation of duties is:
a security principle that divides critical functions among different staff members in an attempt to ensure that no one individual has enough information or access privilege to perpetrate damaging fraud.
And the CMMC Assessment Guide goes on to say
A company must avoid situations in which conflicts of interest or even lack of knowledge can create security problems. This can be accomplished by splitting important duties and tasks between employees in order to reduce intentional or unintentional execution of malicious activities, when those involved are not colluding. This allows the organization to minimize employees' fraud, abuse and errors. Summarizing, no one person should be in charge of an entire critical task from beginning to end.
In terms of protecting CUI, the DoD wants us to ensure no one individual has unfettered access that would potentially allow compromise of all our information or technology. The DoD is concerned about the “insider threat”, where individuals authorized to access CUI systems or information could – intentionally or not – leave “backdoors” open into the systems, abscond with information, or delete or destroy system components. It’s all about putting another layer of defense in place to ensure our CUI doesn’t make it’s way into our adversaries hands or otherwise get lost.
The good news in all this is that the DoD hasn’t explicitly made up our minds for us. They’ve allowed us to create custom separation of duties policies. Therefore, it’s up to us to determine how to separate the duties in our environments and enforce that separation as necessary.
The bad news is this enforcement can be a serious challenge for small businesses where a single individual may play multiple roles and shoulder many disparate duties. The CEO/President at many small businesses tends to “wear all the hats” and perform all the duties. Is he or she supposed to intentionally alleviate him or herself from some of those duties, effectively “hanging up some of those hats”? Perhaps. In the rest of this post, we explore how a small business can approach separation of duties.
How do small businesses effectively implement separation of duties?
NIST gives a general example of what duties should be separated and how that separation can occur:
- Separation of duties includes dividing mission functions and system
support functions among different individuals or roles; conducting
system support functions with different individuals (e.g., configuration
management, quality assurance and testing, system management,
programming, and network security); and ensuring that security personnel
administering access control functions do not also administer audit
functions. - For example, the person authorizing a paycheck should not also be the one who can prepare them.
- The same person should not test security mechanisms, conduct security audits, and release software for delivery. Policy is created and implemented so that the development team does not do testing and the test team does not do development. This eliminates your ability to intentionally or unintentionally develop a weak security solution that is not identified through testing or is released prematurely before unit, integration, regression, operational and security testing are complete.
- You are responsible for the management of several key systems within your organization. You assign the task of reviewing the system logs to two different people. This way, no one person is solely responsible for the execution of this critical security function.
- You are a system administrator. Human resources notifies you of a new hire, and you create an account with general privileges, but you are not allowed to grant access to systems that contain CUI. The program manager contacts the team in your organization that has system administration authority over the CUI systems and informs them which CUI the new hire will need to access. Subsequently, a second system administrator grants access privileges to the new hire.
These are good examples, but there are hundreds of duties at even the smallest organization, so how specifically can a small business define all the duties that are to be separated, and then enforce that separation? And how can separation of duties be demonstrated to assessors?
Here’s our rule of thumb: in general, policy making (governance) duties should be separated from policy enforcing. Stated differently: the people that configure systems to ensure the rules are followed — or are obliged to follow the rules — should not be those making the rules and vice versa. Otherwise, we have the classic “inmates running the asylum” situation. Note that this duty separation may mean a President has to relinquish the role of IT System Administrator, if possible. We understand this certainly isn’t possible in a one-person shop; in these cases, the assessors are going to have to allow some exceptions to this general principle.
Our approach to implementing this general rule of thumb is multi-step:
1) Define at a high level the categories of duties that are to be separated. We suggest establishing in a policy (in your System Security Plan, SSP) the following minimum high-level separations:
-
- The following duties shall require separation:
- IT Administration and Human Resources/Payroll
- Access Authorization and IT Administration
- IT Governance and IT Administration
- The following duties shall require separation:
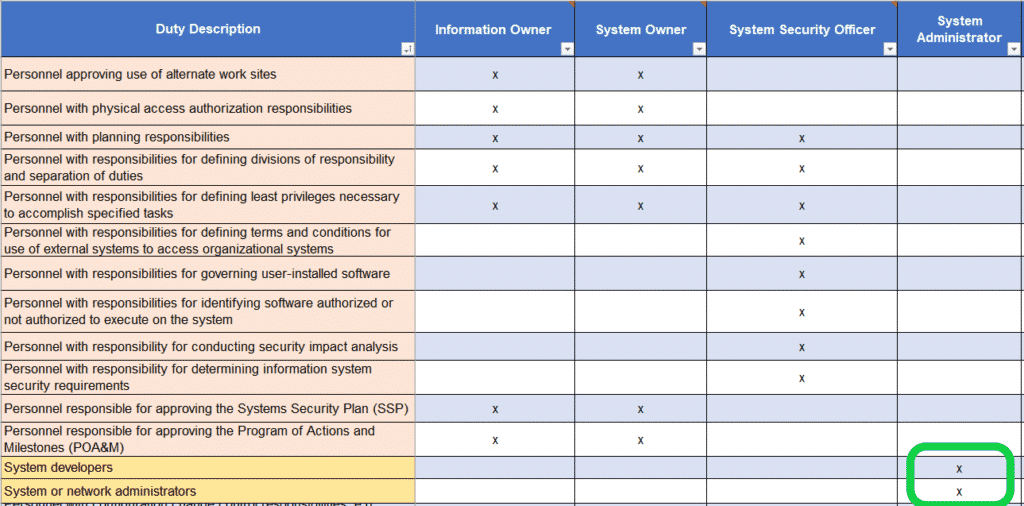
2) Next, list out all the roles and duties at your organization. This can be quite a complex list, even for small businesses. We’ve created a separation of duties matrix to get you started on this process. Here’s a snapshot of a portion of that matrix:
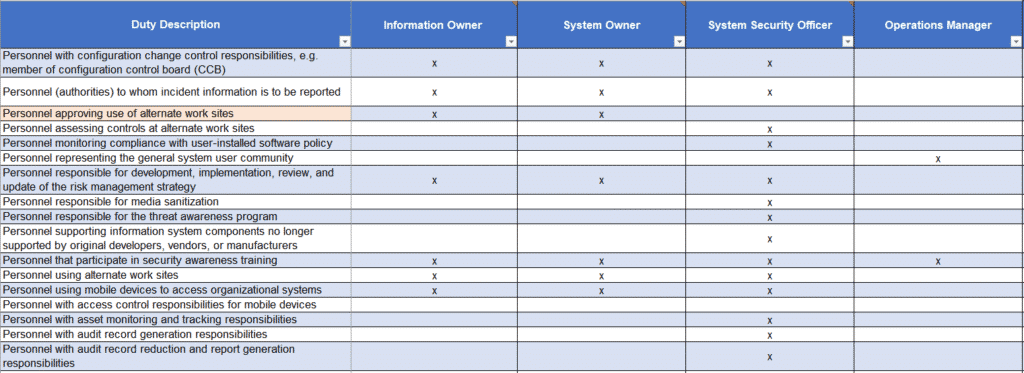
The columns in the matrix are general roles at an organization, including Information Owner (usually the President/CEO/Functional Manager), Operations Manager, etc. Some of these roles may not be relevant to your organization, and some roles may be missing, so feel free to customize the roles as you see fit.
The rows in the matrix list all the individual duties that may be practiced at an organization. This list is adopted straight from the NIST SP 800-171A Assessment Objectives, which catalogs all the personnel a CMMC Assessor may choose to interview during a CMMC assessment. What better way to cover all your bases than to identify each and every duty that may be assessed! There are almost 100 duties listed in the matrix. (As with roles, some of these duties may not be relevant to your organization. Our matrix is just a template; adjust as you see fit.)
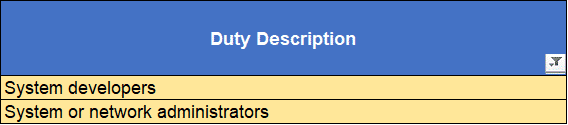
3) Third, identify the duties that must be separated according to the general principle established above. In our matrix, we identify those separate duties by colored cells:

So the governance and authorization duties (pink cells):
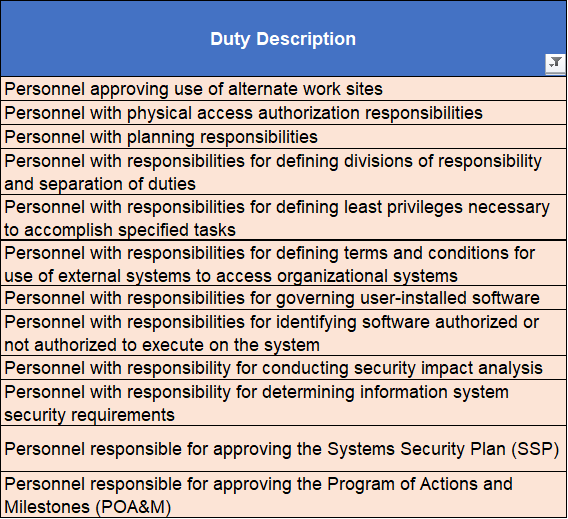
Are to be separated from the IT Administration duties (yellow cells):
4) Next, take some time and go through the matrix, marking an “x” in each cell that represents a duty that a role should perform. You’ll want to make sure that a role doesn’t perform both governance and administration duties, so no role should have an “x” in both pink and yellow rows in our color-coding scheme. (We’ve taken the liberty in the downloadable matrix of filling in “x” in the duties commonly performed by the various roles. Again, adjust as you see fit for your organization.)
In our example, you can see the System Administrator role only performs the System Development and Administration duties. All policy making, planning, approving, and authorization duties are performed by other roles, and vice versa:
5) The penultimate step is to make sure job, duty, and/or role descriptions maintained by your organization (in job listings, employee handbooks, standard operating procedures, etc.) are updated to reflect the allocated duties. Then ensure all personnel are trained on their duties and to understand what roles are allowed to perform which duties. Doing this will help ensure separation of duties is inculcated as part of your organization’s mature cybersecurity culture. This will help you pass a CMMC Assessment.
6) Lastly, you’ll want to ensure there are logical and physical access controls in place, where possible, to enforce the duty separation. For instance, your information and system owner (probably a President, CEO, or functional manager) should not be system administrators. That person therefore should not have Domain Administrator privilege accounts in Windows Active Directory. Conversely, your System Administrators should not be in charge of authorizing new accounts, so they should not be the ones to sign off on a new hire form that authorizes new account creation. And so on and so forth…
Wrapping things up
Separating the duties of individuals in a business is a best practice, in fact, it is one of the tenets of cybersecurity. Perhaps more viscerally, enforcing separation of duties is a requirement for many of us who want to do business with the DoD and pass a CMMC assessment. Defining and demonstrating separation of duties can be a challenge for a small business, but we’ve created a separation of duties matrix – which you can download below – to assist in that process. Let us know if you have any questions about this tool.
By the way, we cover this topic and many more at our quarterly CMMC Workshops. We’d love to have you with us in our next cohort!
