UPDATE 27 November 2024: Note that the DoD self-Assessment Methodology (DoDAM) and SPRS scoring only works for NIST 800-171 revision 2. The DoD has announced no plans to update the DoDAM and SPRS site for 800-171 revision 3. DoD contractors are under no 800-171 revision 3 obligations for the time being.
UPDATE 21 October 2024: we’ve updated this post to include the latest on the DoD Self Assessment and SPRS website reporting process, including the changes that DISA made to the SPRS v4.0 site in October 2024.
Overview of the DoD Self-Assessment Requirement
In a proposal published in the Federal Register, the DoD has outlined a new set
of rules it wants to add as clauses to the DoD Federal Acquisition Regulation Supplement (DFARS, the DoD contracting rules):
- 252.204-7019: Notice of NIST SP 800-171 DOD Assessment Requirements
- 252.204-7020: NIST SP 800-171 DOD assessment requirements
These new rules, which go into effect 30 November 2020, will supplement DFARS 7012 and can be added as clauses in contracts between the DoD and its supply chain vendors. We explain these rules in depth in a previous blog, so here we’ll give the nutshell version. Together, these rules require members of the DoD supply chain that potentially process Controlled Unclassified Information (CUI) to do two things to be considered for contract award (or to be part of the subcontractor team to execute the contract):
- Perform a “Basic” cybersecurity self-assessment according to
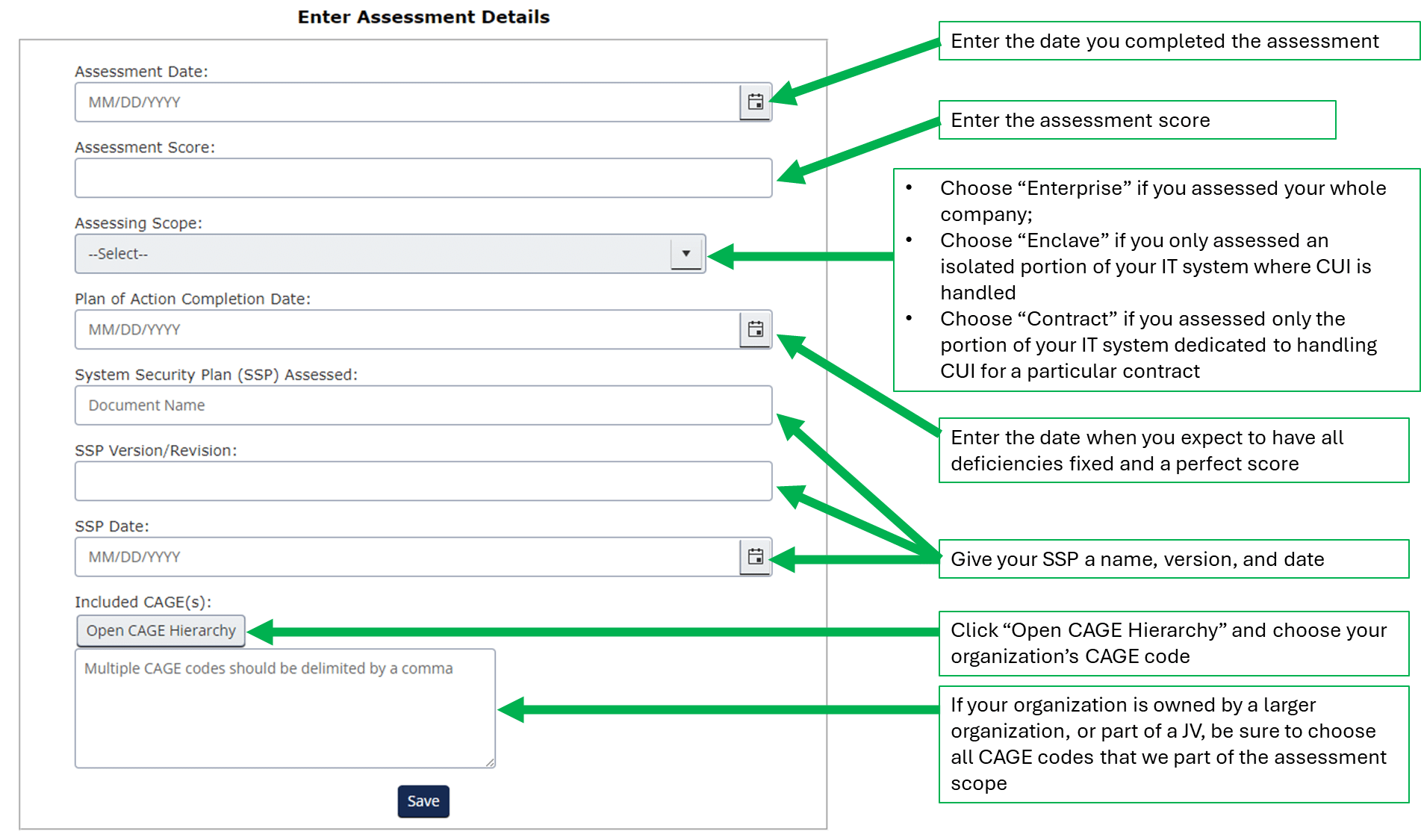
the DoD 800-171 Assessment Methodology (DoDAM) - Submit the following information through the Supplier Performance Risk System (SPRS) or via email to [email protected]:
- System security plan name
- CAGE codes supported by this plan
- Brief description of the plan architecture
- Date of assessment
- Total score
- Date score of 110 will be achieved
After 30 November you may see the clauses in Requests for Proposals (RFP) or contracts, or you may have your Prime contractor ask your organization to execute these tasks even sooner. So in this blog we’ll cover the basics of how to perform the DoD self-assessment and report your score.
It’s important to note: these requirements will only pertain to those RFP/contracts with the clause embedded in them and that also have clause 252.204-7012 or some other indication that CUI is or will be processed as part of the contract. So, if you only handle Federal Contract Information (FCI) and/or are only targeting CMMC Level 1, you won’t need to perform the Basic self-assessment and report your score.
Executing the DoD 800-171 Assessment Methodology
The DoD 800-171 Assessment Methodology has actually been around since November 2019, when it was published by the Office of the Secretary of Defense after the completion of a pilot assessment program executed by the DoD Contractor Management Agency (DCMA) on several large prime contractors. DCMA spun up a capability called the Defense Industry Base Cybersecurity Assessment Center (DIBCAC) to execute the program. For more on DIBCAC, see this interview with it’s head, Mr. John Ellis.
We previously detailed the 800-171 Assessment Methodology and scoring system in this blog, which has a free tool for you to conduct a preliminary Basic assessment. But we’ll reiterate the basics here:
- Each facet of a contractor organization covered by a CAGE code must be tied to an IT System Security Plan (SSP). The SSP is like a set of blueprints for the organization’s cybersecurity program.
- Each SSP will be evaluated against a scoring rubric, with a maximum score of 110 possible.
- A perfect score is 110—indicating a robust set of policies and technical implementations as described in the SSP
- Each of the 110 controls in 800-171 is assigned a “weighted subtractor” value; non-compliance with that control means the assigned value is subtracted from 110
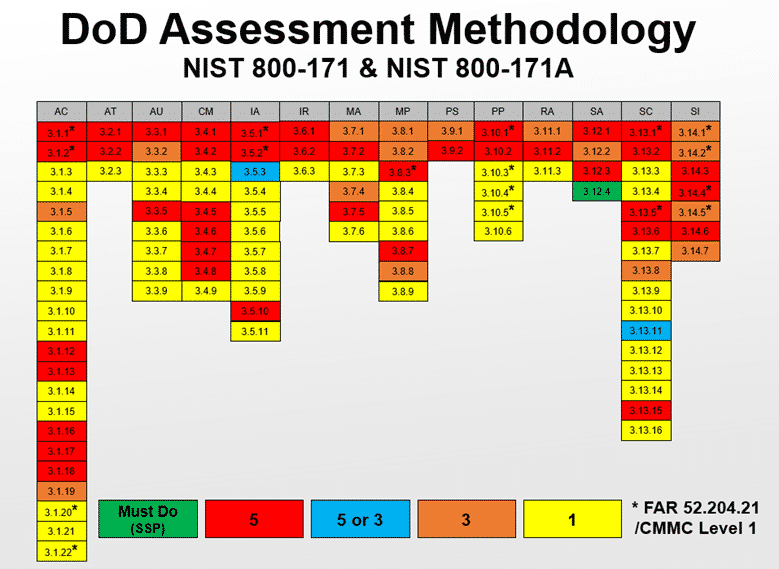
- Some controls are worth 5 points, some 3, and some 1. They aren’t all worth 1 point. This means that a negative score is possible
- There are 42 controls worth 5 points, which include:
- The 17 basic safeguards required of all Federal contractors’ IT systems, as outlined in the FAR Clause 52.204-21, and
- Other controls that “would allow for exploitation of the network and its information.”
- There are 14 controls worth 3 points, which if not implemented “have a specific and confined effect on the security of the network and its data”
- The remaining 54 controls are worth 1 point. See the image below for a graphical representation of the score values for each control.
- Two of the controls, 3.5.3 (multi-factor authentication) and 3.13.11 (FIPS-validated cryptography), are worth either 5 or 3 points, depending on the level on non-compliance
- If the organization does not have an SSP, no score is possible. For the purposes of scoring we suggest treating no SSP as a zero out of 110 and immediately subtract 110 points.
To execute the Basic DoD self-assessment, the organization evaluates its compliance with each of the 110 controls. For each control that does not meet the requirements prescribed by 800-171, subtract the weighted subtractor (either 5, 3, or 1) from 110. The score result at the end of the assessment will be a number, such as “95”.
We’ve built a tool to help you through this assessment. In the tool, each of the 800-171 controls is interpreted as a single Yes or No answerable question. Answer “Yes” if your organization has implemented the control; answer “No” if not, and the weighted score is subtracted from the overall value.
If your organization is being pressed for an immediate reporting of your DoD self-assessment results, use our tool to help calculate a preliminary score. We say “preliminary” because it only leads you through a rough assessment of compliance with each of the 110 high-level controls. Because you are required to report the score to the government, you’ll want to make sure it is as accurate as possible. (There is no indication that poor scores are factored into award selection, but it is the Contracting Officer’s prerogative what to do with the scores) Therefore eventually you’ll want to make sure you eventually self-assess against all of the “Assessment Objectives” associated with the 110 controls. The Assessment Objectives are listed in the NIST 800-171A publication, which is a companion document to NIST SP 800-171. All told, there are 320 Assessment Objectives for the 110 controls. The DoD follows these objectives closely when they perform their Medium or High-level assessments (see below for a differentiation between Basic, Medium, and High).
Since we are going to be assessed against these objectives, we better make sure we execute the actions for each objective, so we actually refer to these objectives as “Organizational Actions”. Our Totem™ Cybersecurity Compliance tool includes these Organization Actions and so provides a robust and granular security assessment workflow that will generate a more accurate score. Contact us if you’d like a free 30-day trial of the tool. Or join us in one of our workshops where we’ll teach you how to conduct your self-assessment and interpret the requirements for you.
Reporting your DoD Assessment Methodology score via SPRS
Once you’ve generated your score, the new DFARS rules require your organization to maintain your current score in the SPRS, meaning the Basic DoD self-assessment can be no more than three years old. To get access to the SPRS website, your organization unfortunately must jump through some hoops. Your organization will need to:
- (Update 10/10/2024): Get registered on the DoD’s Procurement Integrated Enterprise Environment (PIEE) site. You can find guidance on how to register a new account here. Alternative, if you have a CAC card or an ECA certificate, you may be able to login to the site using those credentials. We have instructions on how to obtain an ECA certificate in this blog.
- (Update 09/10/2021): Setup a workstation according to these instructions for accessing the PIEE site: https://piee.eb.mil/xhtml/unauth/web/homepage/machineSetup.xhtml
- Browse to https://piee.eb.mil using an approved browser and click Register from top right, then follow the instructions here: https://www.sprs.csd.disa.mil//pdf/PIEE-NonGovInstructions.pdf. NOTE: you’ll need your organization’s CAGE code to register. Call the DISA Help Desk early in the process if you run into delays: 866-618-5988 or email.
- UPDATE (11/16/2020): If the person at your organization that will be doing the reporting is other than the Electronic Business Point of Contact (EB POC) as listed in SAM.gov, it seems that person may have to have a role of Contractor Administrator (CAM) in PIEE to be able request the proper role in SPRS. The following are instructions from DISA for obtaining a CAM role:
- Your role of Contractor Administrator (CAM) must be authorized by your Electronic Business Point of Contact (EB POC) as listed in SAM.gov.
- If your EB POC has not yet submitted your appointment letter, they will need to complete and return this letter before you can be activated.
- The latest version of the CAM Appointment Letter may be downloaded here: https://piee.eb.mil/documentation/CAM-VendorAppointmentLetter.pdf
- The CAM letter should be filled out as follows:
- CAM Full Name, Email and Phone number should be the information of PIEE user being appointed as the CAM.
- The Cage Code should be listed in part #1 where it states “Commercial and Government Entity (CAGE) codes”.
- The user must sign on the Signature of CAM Appointee.
- The Electronic Business POC must print and sign.
- Your Electronic Business POC is listed on the System for Award Management (SAM) website (http://www.sam.gov) per your cage code.
- Please email us the letter [email address is included on the form] and don’t forget to include the WAWF Username.
- If you need further assistance, feel free to call us 1-866-618-5988.
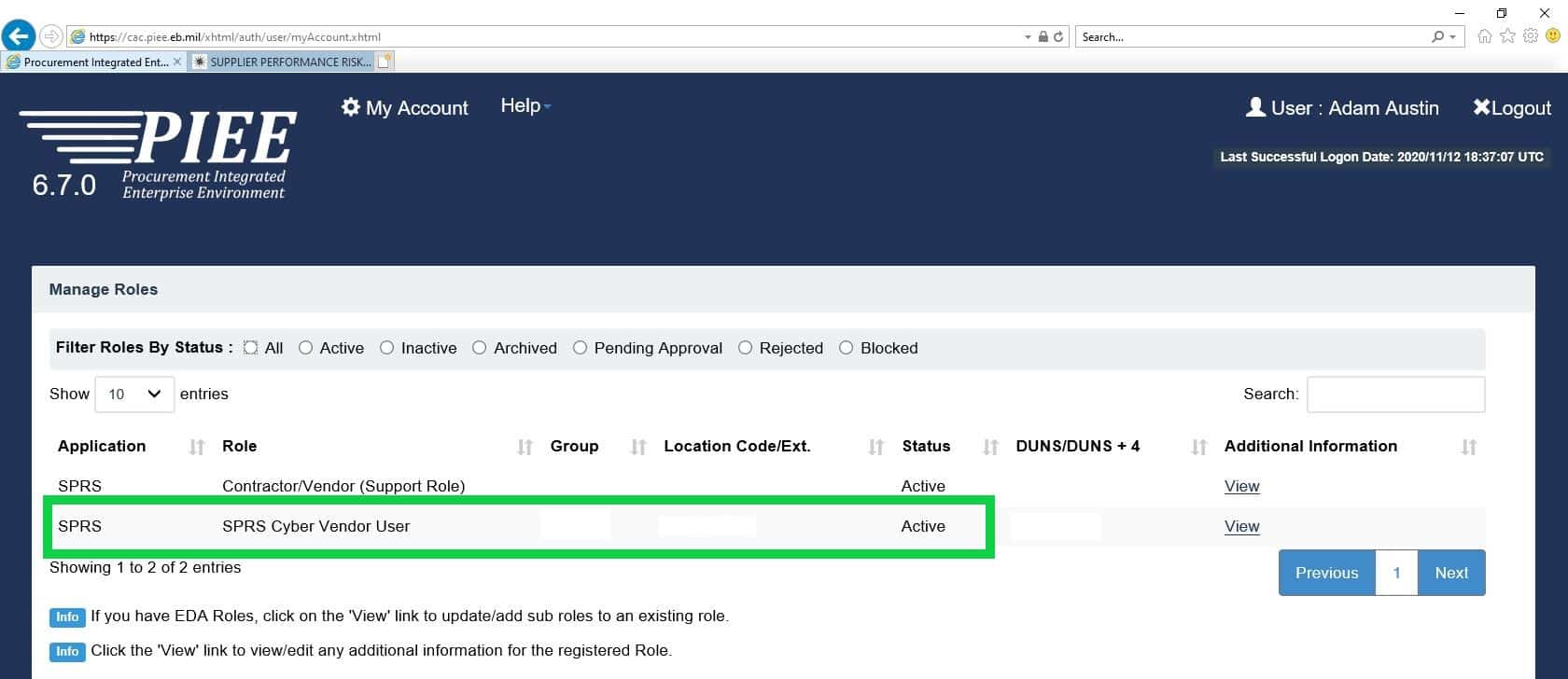
- Also note, the instructions appear to be incorrect so you need to make sure you request the “SPRS Cyber Vendor User” role and not the “Contractor/Vendor (Support Role)” as indicated in the PIEE instructions. Submit your application and wait for an email with your account approval.
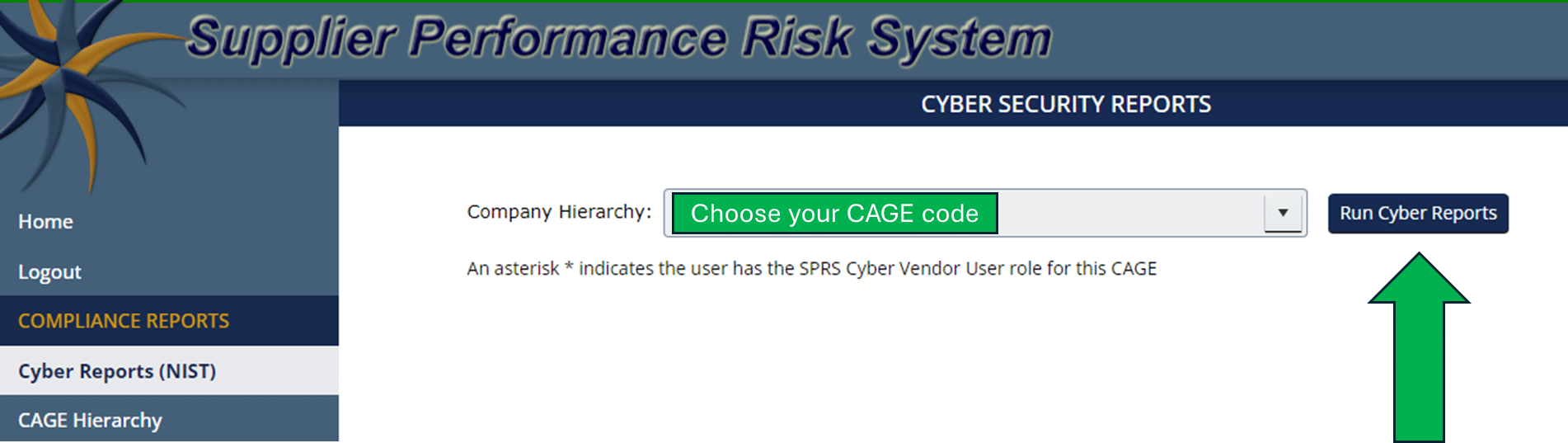
- Once you are into SPRS, you’ll need to follow the instructions described here: https://www.sprs.csd.disa.mil/pdf/NISTSP800-171QuickEntryGuide.pdf. NOTE: heed the instructions and screenshots that once you click the “Cyber Reports (NIST)” link in SPRS, you may need to “create a header” in the reporting interface to actually be able to report your score.
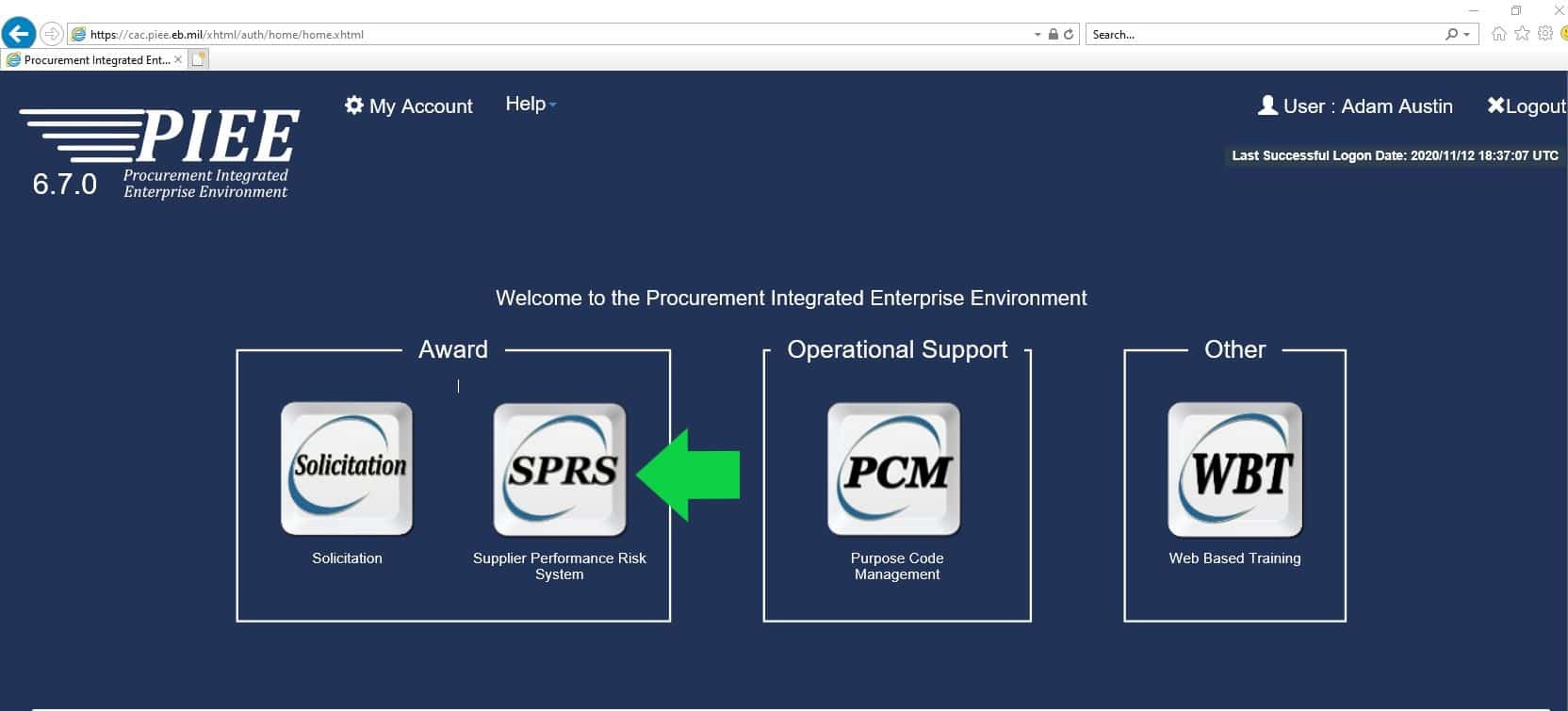
UPDATE (10/21/2024): The images below take you through the process of reporting your score once you have access to SPRS v4.0:
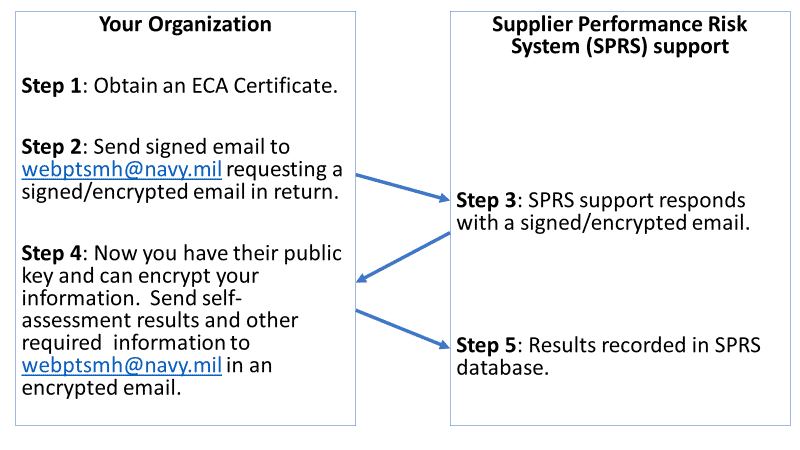
Alternately you can submit your DoD self-assessment score via encrypted email to [email protected]. You’ll need an ECA certificate to report via this method. The protocol diagram below explains what the person at your organization with the ECA certificate will need to do to be able to send your information to the email address:
We explain the whole score generation and reporting process in detail in our Workshops. Come join us!
DIBCAC Medium or High 800-171 assessments and CMMC assessments
The DoD self-assessment explained above generates what the DoD considers a “Basic” or Low confidence assessment score. DCMA DIBCAC is currently and will continue to conduct higher confidence assessments (“Medium” or “High” confidence) and post the scores in SPRS:
- Medium—DCMA does an off-site review of your SSP to verify your Basic assessment score
- High—DCMA conducts an in-depth off- or on-site assessment of your entire cybersecurity program, utilizing the assessment objectives published in NIST SP 800-171A.
For these Medium or High confidence DIBCAC assessments, DCMA is selecting small business members of the supply chain that perform work on “programs of interest” or that may face greater cyber threats.
If they select your organization, they’ll reach out at least 30 days in advance of the High assessment to give you time to prepare. If you are selected, it will take some time for you to prepare. You’ll need to get all your cyber “ducks in a row”, including documentation such as the SSP and “compelling evidence” that you’ve implemented the SSP. During the assessment, you can expect a cadre of DIBCAC assessors to conduct a two-faceted assessment—part virtual for the logical controls and part on-site for the physical controls.
UPDATE (10/21/2024): C3PAOs will also report the results of official CMMC Level 2 Assessments through SPRS. We’re not quite sure how that will look and feel yet, but we’ll certainly publish another post detailing that mechanism once it’s in place.
Let us know if you need help preparing for the assessment. We are happy to help!
As always, good hunting!
Adam