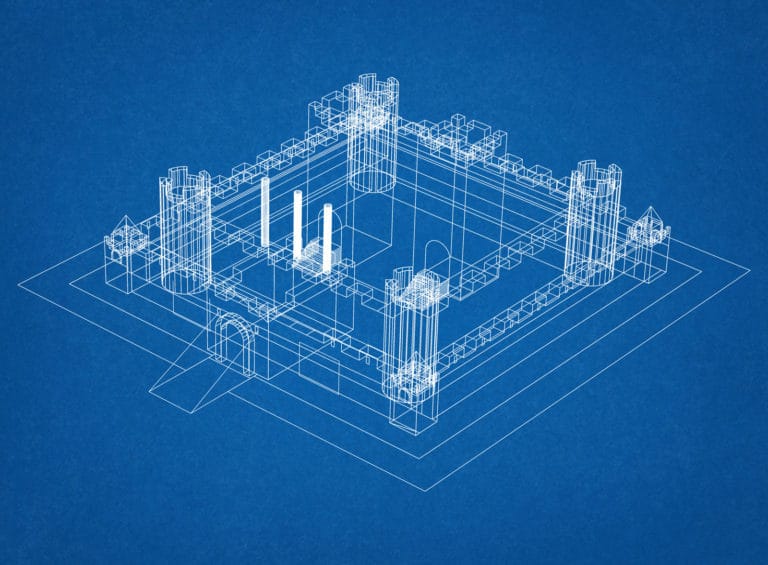
Information is your organization’s second most valuable asset (after the people, of course!) You need to protect that information with multiple layers of security, kind of like a castle. A System Security Plan is like the blueprints for your organization’s cybersecurity castle. Without a System Security Plan, the cybersecurity castle (or cybersecurity “program”) is bound to be built inefficiently, which costs the organization time and money. Even worse, a poorly planned castle can be breached by the enemy—a compromise resulting in data theft or destruction—which then costs the organization much more: reputation, regulatory fines, lawsuits, etc. Furthermore, NIST 800-171 and the DoD’s Cybersecurity Maturity Model Certification (CMMC) require an System Security Plan (SSP) for the protection of Controlled Unclassified Information (CUI). Here’s how Totem can help:
How Totem can help your small business develop a NIST/CMMC System Security Plan (SSP)
Your organization can rely on Totem to help develop its System Security Plan (SSP) in three interrelated ways:
- Attend one of our DFARS/NIST/CMMC Workshops. We educate you on the basics of System Security Planning, and provide you with a small business SSP template, which saves days of time developing one from scratch.
- Subscribe to our Totem™ Cybersecurity Compliance Management software. Totem™ has a simple, intuitive SSP workflow built in, and includes access to the SSP template.
- Engage us for a custom DFARS/NIST/CMMC gap assessment and strategic policy planning session. Let us do the heavy lifting and build a custom SSP for your organization.
Each of these options aligns with our DFARS/NIST/CMMC Preparation Methodology. With our approach, you’ll
- start by gaining an understanding of the requirements,
- continue by cataloging and categorizing your organizational assets –including the CUI you handle– according to government guidelines,
- and then perform an assessment against the NIST 800-171 standard in parallel with building an 800-171-aligned System Security Plan (SSP).
In the Workshop, we teach you how to do all these things, and provide access to the Totem™ Cybersecurity Compliance Management tool to help conduct a security controls assessment, manage the System Security Plan itself, and execute a Plan of Actions and Milestones (POA&M). After the Workshop, you can subscribe to Totem™ to continue managing your SSP; after all, there is always something to do to make your organization more secure. Just as a castle requires constant maintenance and improvement as the enemy threat changes, the SSP is a “living” thing, requiring regular maintenance as the regulations or your environment, or both, change. Instead of the hassle of an SSP in Word or Excel format, our Totem™ tool is the perfect place to maintain your SSP.
If, after the Workshop, you realize your organization needs a little more help, you can engage us for a one-on-one gap assessment. During this engagement, we’ll use the Totem™ tool workflow to craft your NIST/CMMC System Security Plan. In your SSP we’ll lay out in detail the expectations your organization should establish for its castle (policies), and then describe how that castle should work (enforcement mechanisms).
If you have an existing System Security Plan in any format, you can easily import it into Totem™. Totem™ includes an intuitive search feature, and we ensure the requirements set is up-to-date, so you don’t have to worry.
We’ve been managing SSPs for the DoD and US Federal Government enterprise IT (big ones, like the US Air Force and Centers for Medicare and Medicaid Systems (CMS)) for over a decade now. We’d love to bring that experience and know-how to bear on your small business cybersecurity compliance needs. We’ll help you develop common sense, cost-effective SSP, and help your organization stay compliant so you can continue to work on DoD programs. Click the button below if you’d like to know more about how we can help with your System Security Plan.
