
The importance of cybersecurity user training in NIST 800-171
We’ve made the assertion in our Totem Top 10 that, after you have gathered a complete inventory of all your IT system assets and identified

We’ve made the assertion in our Totem Top 10 that, after you have gathered a complete inventory of all your IT system assets and identified

The DoD Industrial Base (DIB) has long awaited guidance on what IT system components are in scope for cybersecurity protections under the National Institutes of

The Cybersecurity Maturity Model Certification (CMMC) program began with the ambitious goal of introducing compliance and oversight to roughly 300,000 defense contractors. Not surprisingly, this
UPDATE 20 December 2024: This post is about the proposed CMMC rule, which has now been finalized. Therefore, this post has been superseded by our
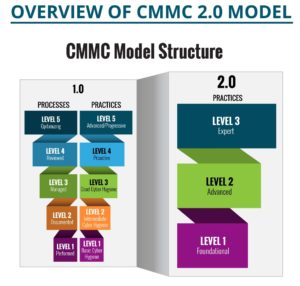
On 4 November, the DoD announced significant CMMC updates, by publishing a new model — “CMMC 2.0” — on a revamped website, and outlining a
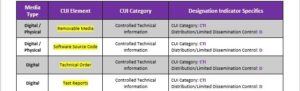
Employee CUI Handling Guide Small businesses in the DoD contractors, subcontractors, and vendors –members of the DoD Industrial Base (DIB)–have lots to do to secure

We were intrigued by a comment we recently received from Brian Ruthrauff on our password policy blog with regard to storing CUI system credentials in

Cybersecurity Risk Assessment Within the Defense Industrial Base Risk management is a part of business. Although the level of risk companies face depends upon a
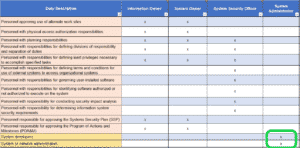
Background on the CMMC requirement to separate the duties of individuals Members of the DoD supply chain – the Defense Industrial Base (DIB) — that