On 4 November, the DoD announced significant CMMC updates, by publishing a new model — “CMMC 2.0” — on a revamped website, and outlining a new strategy for CMMC. The DoD also plans to release an updated interim rule request in the Federal Register as part of making CMMC a law.
This post will focus on our initial takeaways from the CMMC updates, and why these changes are good for small business DoD contractors. We’ll follow up in the next few weeks with a post describing the new model in more detail.
What has changed in CMMC 2.0?
The DoD Cybersecurity Maturity Model Certification (CMMC) updates make CMMC 2.0 a simpler model than the first iteration of CMMC. The image below shows the DoDs diagram of the new model vs. the old:
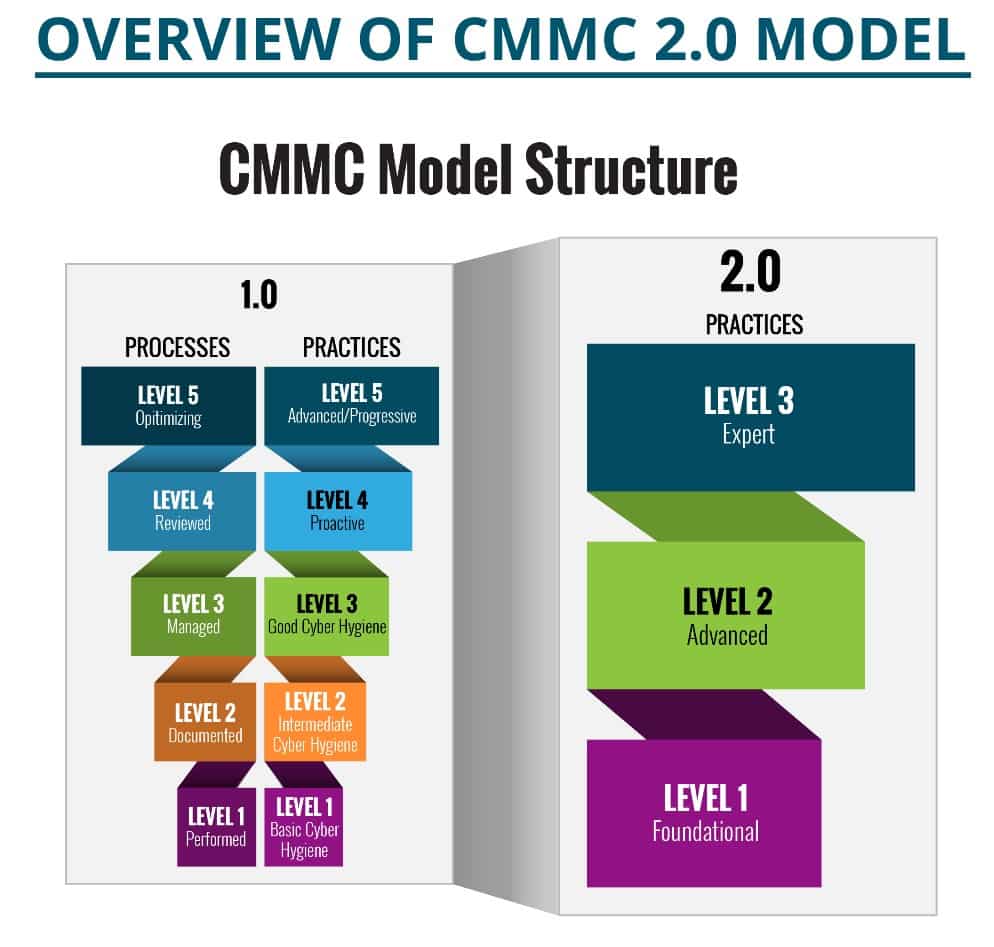
The most striking difference is, as you can see, in the CMMC 2.0 there are now three levels, instead of five. Level 1 hasn’t changed, the new Level 2 is the same as previous Level 3 (with some additional significant differences), and the new Level 3 is the old Level 4/5 (again there will be some significant additional differences).
So the DoD removed the (old) CMMC Levels 2 and 4, and remade the (old) levels 3 and 5.
CMMC Level 1 is the same as before: it consists of 17 basic cybersecurity practices required to protect Federal Contract Information (FCI). All Federal Contractors will have to implement these basic protections for FCI before they can execute contracts and subcontracts. However, now with the CMMC updates, members of the Defense Industrial Base (DIB) will not have to have a CMMC certification for Level 1, we’ll be able to self-assess and attest to the implementation as we always have.
The bigger changes with CMMC 2.0 come into play at (the new) Level 2, which, as with previous Level 2/3 was reserved for those DIB members that handled the subset of more sensitive FCI known as Controlled Unclassified Information (CUI). CUI requires significant additional cybersecurity safeguarding. The DoD summarizes the new CMMC Level 2 on their website:
- Eliminates all maturity processes
- Eliminates all CMMC unique security practices:
- Advanced / Level 2 will mirror NIST SP 800-171 (110 security practices
Also, not all (new) CMMC Level 2 DIB members will have to pursue a CMMC certification. Instead, CMMC assessment / certification (still to be performed by CMMC Third-party Assessment Organizations (C3PAO)) will only be required in certain circumstances. As the DoD puts it:
- Allows the majority of contractors, associated with Foundational/ Level 1 and a subset of Advanced/Level 2 programs, to perform annual self-assessments
- A portion of the Advanced/Level 2 programs (contractors managing information critical to national security) will require triennial third-party assessments
- a subset of programs with Level 2 (“Advanced”) requirements do not involve information critical to national security, and associated contractors will only be required to conduct self-assessments
- Expert / Level 3 programs will require triennial assessments conducted by government officials
Additionally, the CMMC updates allow for Plans of Action and Milestones (POA&M):
- Allows the use of POA&Ms
- Highest weighted requirements cannot be on POA&M list
- DoD will establish a minimum score requirement to support certification with POA&Ms
It appears POA&M allowance may be tightly coupled with the DoD 800-171 Assessment Methodology scoring criteria.
The Expert / Level 3 practices in CMMC 2.0 will be based on a subset of NIST SP 800-172 requirements, as much of Level 4/5 in CMMC 1.0 had been.
Why the CMMC updates are good for small business contractors
The first best thing about CMMC 2.0 is that the “maturity” process requirements have been removed. Most of these were entirely redundant and were already called out in the NIST 800-171 standard. The Process requirements would only have us waste more time on the paperwork side of cybersecurity, and would not have contributed to securing our nation’s defense intellectual property. In the Totem™ Cybersecurity Compliance Management tool, these are the controls that end with .99x. There were three such controls and 19 Assessment Objectives included with each control family. If you have been building a System Security Plan (SSP) in our tool, just ignore those controls going forward.
The next best thing is the allowance of POA&Ms. A POA&M is like a set of “work instructions” that describe how an organization will remediate any deficiencies in its cybersecurity program. NIST 800-171 is an extensive standard of cybersecurity practices. Most small businesses that first encounter that standard will have many “gaps”, or deficiencies as they compare their current state of cybersecurity affairs against the requirements. Under CMMC 1.0, organizations were not allowed a POA&M at the time of assessment. In other words, you’d have to have a perfect cybersecurity program at the point of assessment. But there is no such thing as a perfect cybersecurity program, even for the IT systems that the DoD owns, and especially for younger small businesses that make up so much of the rich
diversity and intellectual firepower (so to speak) of the DIB. So the allowance of POA&Ms at assessment time (with certain caveats that the DoD will elaborate on in time) is a reflection of reality and sanity on the DoD’s part.
The last reason (that we’ll touch on in this post) why these CMMC updates are a good thing, is the reduction in third-party assessment mandates. Now only a subset of CMMC Level 2 organizations will have to pay the fees to achieve CMMC certification. The DoD’s own estimate for these assessments was an insane $60,000 annually. For our company, that would mean at least one line worker we couldn’t keep on staff because we’d be spending that money on CMMC certification. We’ll see how things shake out and how the DoD determines who has to get certified, but our bet is that most small business DIB members won’t be seeing a C3PAO in the near future.
What hasn't changed with the CMMC updates
The CMMC updates don’t mean small business DoD contractors can rest on their laurels. Far from it. The FAR 52.204-21 clause for the protection of FCI still exists in all Federal contracts. New clients come through our doors weekly with their “hair on fire” because they are losing money because the Primes want them 100% compliant with this clause before they will send them another Purchase Order. And even the basic cybersecurity protections mandated by this clause can be a challenge for a small business.
The DFARS 252.204-7012, 7019, and 7020 clauses will still be in contracts for those of us that handle CUI. NIST 800-171 is still a requirement, and is an extensive standard. DFARS 7019 is still in contracts as well and requires a self-assessment and accurate reporting of your Supplier Performance Risk System (SPRS) score. If you’re not abiding the regulation and/or reporting inaccurate scores, the DoD has threatened use of the False Claims Act.
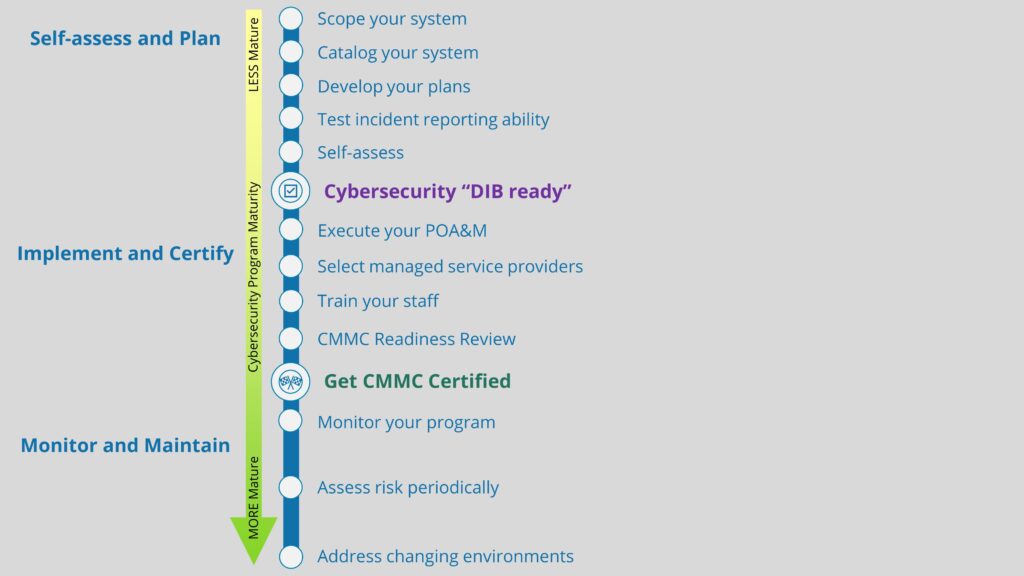
So the CMMC updates don’t really buy us any extra time in securing the FCI and CUI we are privileged to handle by virtue of executing a DoD contract. We need to be moving now to implement the required safeguards. If anything, CMMC 2.0 relieves us of significant paperwork burden as well as the unreasonable expectation of perfection during assessment of our cybersecurity programs.
For you Managed Service Providers (MSP) out there, you still need to get your clients’ IT system squared away to meet the FAR and DFARS requirements, and there is no indication from the DoD that you will be exempt from CMMC 2.0 requirements. So keep on making those improvements!
How Totem is helping
Our Totem™ tool and our Workshops have been around since before CMMC was even a gleam in a Pentagon bureaucrat‘s eye. We aren’t going anywhere.
Totem™ has the FAR and NIST 800-171 standards built into it (in fact the tool was built around these standards), so you can continue to work on your FCI and CUI compliant cybersecurity programs. The tool continues to keep track of your SPRS score dynamically. We’d love to let you take Totem™ tool for a test drive.
We also love just to talk about this stuff, so get in touch and let us know how we can help!
Good Hunting!
Adam