Version 1.0 of the DoD CMMC is Out!
The days of Department of Defense (DoD) contractor cybersecurity self-assessment are coming to an end with the new CMMC certification. As we’ve mentioned in our online educational series on DoD contractor cybersecurity, the current paradigm of self-assessment against the DoD Federal Acquisition Regulation Supplement (DFARS) requirement to protect Controlled Unclassified Information (CUI) is going to be supplemented with a third-party certification starting in 2020.
This CMMC certification, issued by an independent third-party according to the Cybersecurity Maturity Model Certification (CMMC) standard, will be required for some contracts as early as September 2020. Without a CMMC certification, your organization won’t be able to propose to new contracts or execute ongoing contracts. In this blog, we’ll give an overview of the current CMMC model, and implications for small- to mid-sized DoD contractors.
The New CMMC Model
Currently, the DFARS cybersecurity clause outlines two main requirements:
- Provide “adequate security” for CUI by implementing the safeguards listed in the National Institutes of Standards and Technology (NIST) Special Publication 800-171 (SP 800-171)
- Implement a cybersecurity incident response and reporting plan
Current NIST Assessment Requirements
There are 110 safeguards (controls) listed in the NIST 800-171 standard, and contractors are currently tasked with self-assessing compliance to that standard and attesting their level of compliance to the DoD. The DoD released a handy assessment methodology in November 2019 to help contractors perform this self-assessment. The methodology also contains a scoring system, and contractors voluntarily submit their scores to the DoD. But things are going to change with the CMMC requirements.
Upcoming Compliance Changes
Ellen Lord, Under Secretary of Defense for Acquisition and Sustainment, said in a January 2020 press briefing announcing the formal release of the CMMC model: “we are looking at late spring/early summer timeframe to complete a new defense acquisition regulation, a new Defense Federal Acquisition Regulation, or DFAR.”
This DFARS update will mandate the CMMC, which will incorporate both of the existing two requirements mentioned above and additionally require contractors to have their compliance with the DFARS/CMMC certified by a third-party assessment organization (C-3PAO), as opposed to self-assessing/attesting. Essentially the CMMC certification will be a “license to operate” in the DoD space, and without a CMMC certificate, contractors will not be able to compete on RFPs nor execute contracts.
The DoD has convened a board tasked with developing criteria for accrediting the C-3PAOs, and C-3PAO selection is supposed to take place over the first and second quarter of FY2020.
What Does the CMMC Certification Consist Of?
The CMMC certification is comprised of 5 levels of cybersecurity maturity, ranging from level 1 “Basic” to level 5 “Advanced”. Each contract will be assigned a CMMC Level the contractor must meet to execute the contract. Maturity is determined by the level of implementation of cybersecurity practices (aka safeguards, controls) spread across 17 domains. The image below, found in CMMC model briefing materials, depicts the model.
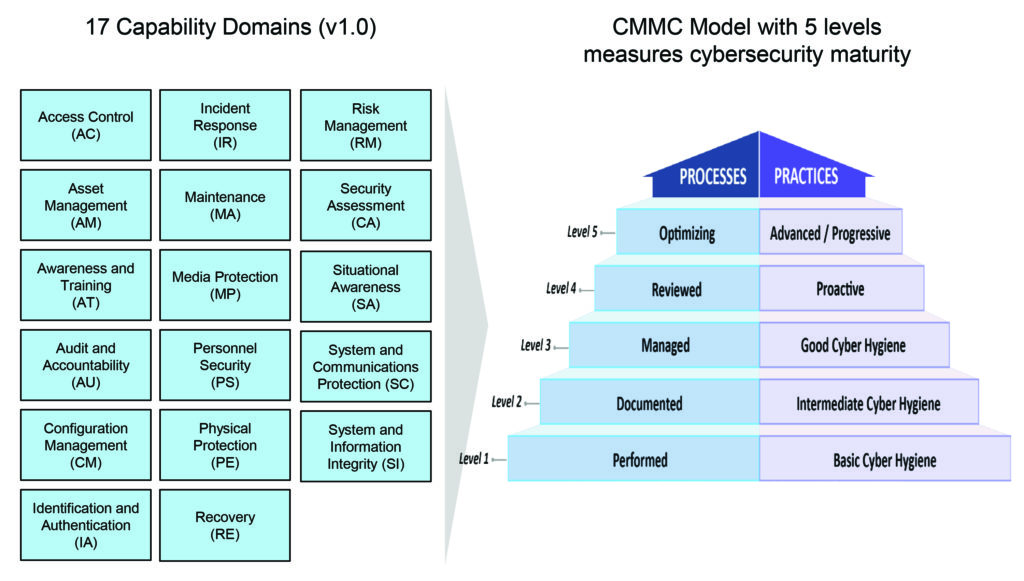
Those of you familiar with DFARS 7012 / NIST 800-171 will understand “domains” as “families” and “practices” as “controls.” In fact, Level 1 of the CMMC requirement has 17 practices which are the 17 basic cybersecurity safeguards already required by the FAR clause 52.204-21 for the protection of Federal Contract Information (FCI). CMMC Level 3 includes all 110 NIST 800-171 controls as well as 20 additional practices, for a total of 130 controls.
We’ve been advising our clients that implementing NIST 800-171 should get your organization most of the way to a CMMC Level 3 certification; assuming you have your System Security Plan (SSP) and budget squared away, 800-171 will get you 85% (110/130) there.
What Level CMMC Certification Will I Need to Hold?
Per the CMMC Frequently Asked Questions (FAQ), all DoD contractors will eventually have to hold at least a CMMC Level 1 certification, as all of us process at least some FCI. Those of us who process Control Unclassified Information (CUI) as well will have to hold at least a CMMC Level 2, and more likely a CMMC Level 3 certification.
Levels 4 and 5 of the CMMC requirement add some additional practices that will be outlined in the soon-to-be-released NIST 800-171B supplement, and are designed to be implemented by those contractors that are targets of Advanced Persistent Threat (APT, e.g. nation state level adversaries, the big guys like China, Iran, Russia, and some organized crime syndicates).
Additionally, as part of a CMMC certification, contractors’ cybersecurity “Process” level will be assessed, whereby they have to demonstrate some level of confidence in the “predictability and reliability” of the practice implementation. Process maturity levels range from “Performed” (least mature) to “Optimizing” (most mature). Those of you familiar with Carnegie Mellon’s Capability Maturity Model Integration (CMMI)® for software or systems engineering will be familiar with these Process maturity levels. An “Optimized” cybersecurity program would have a well-documented cybersecurity program (e.g. System Security Plans) across all aspects of the organization, with measured metrics and feedback loops established to continuously improve the program.
Pros and Cons of the DoD's CMMC Model
Here’s our view of a few of the pros and cons of the CMMC model:
Pros of the DoD's CMMC Model
Each Practice is published with a sort of narrative expounding upon the requirement. This narrative consists of:
- Discussion of the requirement, providing authoritative supplemental guidance and references
- CMMC Clarification with action words, e.g.: “Control and limit personal devices like laptops, tablets, and phones from accessing the company networks and information.” from Practice AC.1.003
- Examples painting a picture of a scenario you can build your implementation around, e.g. “Because FCI is not shared publicly, you remind your coworkers to use their company laptops, not personal laptops or tablets, when working on the proposal over the weekend.” from Practice AC.1.003
- References to control sets and standards from which the practice was derived
The model also contains a nice Glossary, as well as a “Source Mapping” table with a cross-walk between CMMC requirements and controls from other Federal government standards, such as the NIST Cybersecurity Framework (CSF).
Cons of the DoD's CMMC Model
If NIST 800-171 isn’t redundant enough, Level 3 of the CMMC requirement has 20 additional controls, with additional redundancy. For example, in the Audit and Accountability domain (identical to the family of the same name in 800-171), there are the following Practices:
- AU.3.048: Collect audit information (e.g., logs) into one or more central repositories.
- AU.3.051: Correlate audit record review, analysis, and reporting processes for investigation and response to indications of unlawful, unauthorized, suspicious, or unusual activity.
- AU.3.052: Provide audit record reduction and report generation to support on-demand analysis and reporting.
AU.3.051/052 require a Security Information and Event Management (SIEM) tool anyway, which is what is explicitly called out by AU.3.048. So why do we need 048?
NIST 800-171 clearly defines how each control is to be assessed in its companion 800-171A document, it is unclear how the additional non-800-171 Practices in the CMMC requirements are to be assessed by the C-3PAO. We can only hope a companion “CMMC-A” document is developed and published by the C-3PAO board
How Does the CMMC Certification Affect Small- to Mid-sized DoD Contractors?
We have given an overview of the CMMC model. So what does this mean for you as a small- to mid-sized DoD contractors?
Acquiring a CMMC certification is going to be a challenge for any sized DoD contractor, especially small- to mid-sized. A cynical point of view gravitates to the notion that the CMMC Model was pushed by large prime DoD contractors to overburden small business contractors to the point where they can’t maintain viability on contracts. In this manner, the large primes regain the share of contracts set aside for small businesses. Ms. Lord and Katie Arrington (Chief Information Security Officer for Acquisition) repeatedly dismiss that notion in the CMMC release briefing. For example, Ms. Lord says in the CMMC briefing:
“One of my biggest concerns is implementing CMMC for small and medium businesses, because that’s where a large part innovation comes from. We need small and medium businesses in our defense industrial base, and we need to retain them…
…We understand that CMMC could be a burden to small companies particularly, and we will continue to work to minimize impacts, but not at the cost of national security.”
The briefing went on to clarify that only a subset of contractors will be affected by CMMC in 2020. Ms. Arrington stated that the DoD will incorporate the CMMC model into only “10 RFIs and 10 RFPs this year [2020]” and estimates each contract will affect 150 contractors. So at most about 1500 (10×150) contractors will see CMMC certification requirements in 2020. Ms. Lord hinted that these new contracts with CMMC requirements will be primarily for nuclear arsenal upgrades and missile defense. The RFPs will require “some CMMC Level 3, CMMC Level 1, and there may be one or two that have the 4 or 5 CMMC levels.”
The CMMC certification will then be included in new RFPs and modifications to existing contracts over a period of six years, as the DoD will “identify candidate programs that will implement the CMMC requirements during the F.Y. 2021 through F.Y. ’25 phased rollout… All new DOD contracts will contain the CMMC certification requirements, starting in F.Y. ’26.”
Who Will Be Required To Have a CMMC Certification in 2020?
The bottom line is that not all of us will be required to have a CMMC certification in 2020, but many (~1500?) of us will. The rest of us will be phased in over time. We strongly recommend working your Plans of Action and Milestones (POA&M) to implement all of NIST 800-171 as soon as possible, as you don’t want to get into scramble mode when an RFP drops with CMMC requirements. As some of you have significant strides to take to fully implement 800-171 (e.g. Audit and Accountability or Configuration Management controls) the earlier you start the better, as a scrambled implementation may be impossible in the time frame, and won’t look good for your Process maturity level anyway.
For now, the DoD 800-171 Assessment Methodology (we call this the “DAM”) is in full swing, and DoD contractors are actively being audited by the DoD Contract Management Agency (DCMA). The DoD has emphasized that the DAM is essential to preparing for a CMMC certification, and that the DAM and CMMC are complimentary and concurrent and will work in parallel even after the CMMC certifications are fully up and running. So you need to keep chugging along with 800-171 compliance even though the CMMC requirements are looming. Furthermore, the DoD has stated that self-assessment and DAM score reporting can be a competitive advantage for proactive contractors.
The bottom line is that it’s hard to argue that CUI doesn’t bear protection, and that self-attestation of your organization’s cybersecurity program isn’t the best method of ensuring protective measures are in place. But the CMMC certification probably doesn’t sound like good news to most of you, probably sounds like more work at best, and a paper drill with serious consequences at worst. We tend to agree, but reserve final judgment until we see how the CMMC model shakes out. In the meantime, we recommend you grab a towel and don’t panic.
Good Hunting!
–Adam

