UPDATE 20 December 2024: This post is about the proposed CMMC rule, which has now been finalized. Therefore, this post has been superseded by our post providing an overview of the final CMMC Framework. Please read that post for the latest on the CMMC rule.
On November 4th, 2021, the Department of Defense (DoD) announced major changes to the Cybersecurity Maturity Model Certification (CMMC). This announcement described a transition of the model to a newer, simpler “CMMC 2.0” – a revamped version of the earlier CMMC 1.0. The most notable changes to this model included those to compliance levels, self-assessments, and the cybersecurity controls themselves. This announcement has already sent shockwaves throughout the Defense Industrial Base (DIB), as small business defense contractors are beginning to wonder how this decision will impact them, and if the tireless effort they put into CMMC 1.0 will carry over into this new phase under CMMC 2.0.
We took some time to let this announcement sink in before providing a detailed response. In this blog, we’ll expand upon our initial CMMC 2.0 announcement by looking back on the path that has brought CMMC to this point, followed by a deeper analysis of the new CMMC 2.0 model. Finally, we will outline how your organization can continue to “fight the good fight” in preventing cyber threats under CMMC 2.0. We cover the CMMC in detail in our Workshops, so be sure to join us if you’d like to explore specifics on how to implement CMMC in your small business!
How did we get here?
When CMMC 1.0 was first published in January of 2020, it came as a shock to many DoD contractors. However, their shock was primarily the result of years gone by of business done with the federal government that included little to no cybersecurity awareness or accountability. Over time, the DoD supply chain had been getting hit hard by cyber-attacks, resulting in losses in the billions of dollars and losing highly sensitive information to adversaries. The DoD, tired of watching its supply chain continually succumb to these attacks, released CMMC 1.0 as its solution for holding its contractors accountable to abiding DFARS 252.204-7012, which requires protection of Controlled Unclassified Information (CUI) through implementation of a given set of cybersecurity safeguards (aka “controls”) as defined by the National Institute of Standards and Technology (NIST).
Although the initial purpose behind CMMC 1.0 was good, one of its most glaring issues was that it put small businesses in a position that they likely couldn’t afford to be in. The DoD has estimated that for those pursuing a Level 3 (version 1.0) certification, they would need to spend roughly $180,000 in compliance-related costs ($60,000/year over three years). For some medium and most large businesses, this likely wouldn’t be an issue. For small businesses, however, this number has forced them to reconsider if it’s even worth continuing to do business with the federal government. When sharing with our small business peers this cost estimate, their response is either a very audible gasp, or some remark made in disbelief. How is a 10-person machine shop supposed to know anything about cybersecurity, much less be able to implement several hundred robust requirements?
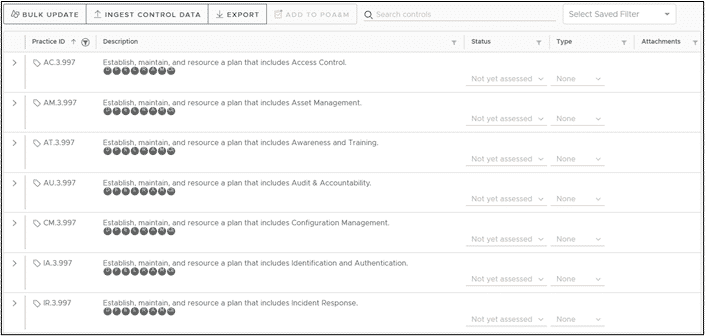
For good or bad, compliance with standards is the reality of doing business with the federal government. Since many DoD contractors process sensitive information such as CUI, they are significant targets for nation-state level adversaries such as China, Russia, Iran, and North Korea. So, we should understand the need for cybersecurity accountability. However, CMMC 1.0 simply was not the solution the DIB needed. It seemed to do more hurt than harm for small businesses, for instance by specifying a myriad of redundant controls (e.g., all .997, .998, and .999 controls, see image below) that did nothing but add heaps of unnecessary paperwork. With all these issues beginning to mount and tension growing within the DIB, it was foreseeable that significant changes were coming to CMMC. When the DoD announced CMMC 2.0 on November 4th of 2021, some of the tension began to subside. Although it has yet to make it into law, and thus won’t appear in any contracts for a while, CMMC 2.0 is a step in the right direction, which we will discuss more about in the next section.
So, what is CMMC 2.0?
CMMC 2.0 now becomes the DoD’s methodology for holding its supply chain accountable to the implementation of the FAR 52.204-21 and DFARS 252.204-7012 clauses, which means that it will replace CMMC 1.0. The overarching goal of the model remains the same, however: protect Federal Contract Information (FCI) and Controlled Unclassified Information (CUI). To simplify the assessment process (and clear up a lot of confusion, let’s be honest), the CMMC model has been reduced from five tiers to three:
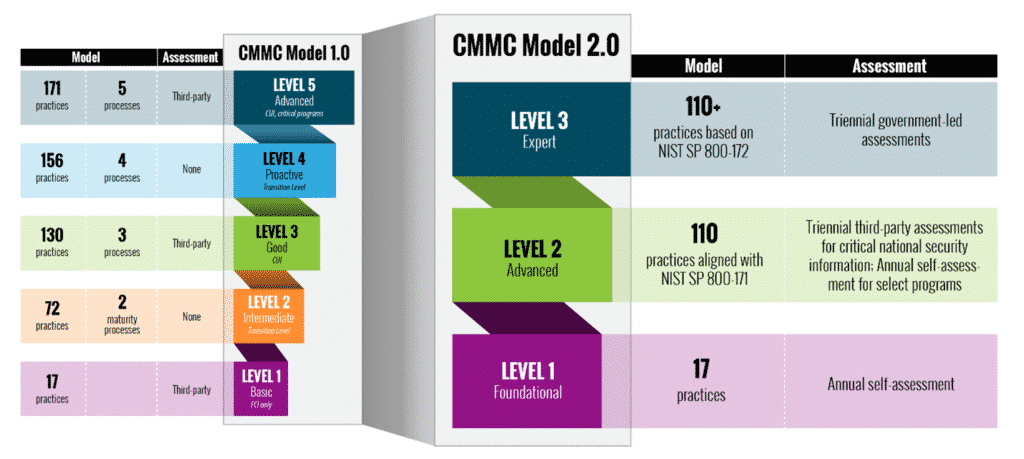
Under CMMC 1.0, Levels 2 and 4 were labeled as “transition levels” for contractors moving from 1 to 3 or 3 to 5. In other words, if a contractor is handling CUI but is not a significant target of a nation-state adversary, they would have pursued a Level 3 certification, but they would still be required to complete the two maturity processes for Level 2 and the three for Level 3. Confused yet?
Well, it turns out that these “maturity processes” did nothing other than increase the amount of unnecessary paperwork on the side of the contractor. It’s unnecessary, because these processes were already identified as part of NIST cybersecurity standards – in addition to the fact that a robust cybersecurity program requires such processes by default – so the DIB should already be focused on implementing them. And, once again, the small businesses would be the ones suffering most as a result, as they typically do not have the resources or manpower to assign to the meaningless paperwork required. So, this was certainly a welcomed change across the board, as contractors can get back to focusing on the NIST control sets that actually matter.
With some of the confusion cleared up, contractors can begin by identifying which level their organization falls under:
- Level 1 (Foundational) – Nothing has really changed with this level in the newer model. If you handle FCI but not CUI, you fall into a Level 1. These organizations are expected to implement the “FAR 17” – the Federal Acquisition Regulation’s 17 most basic cybersecurity controls. According to FAR 52.204-21, ALL Federal contractors are required to implement these 17 basic safeguards, which focus for instance on physical protection and access control. Although this is the lowest level, implementing these controls is not an overnight process, so contractors should remain diligent when doing so. By the DoD’s estimates, the majority (60%) of businesses in the DIB will only have to focus on CMMC Level 1.
- Level 2 (Advanced) – Formerly Level 2/3. If your business is in the manufacturing sector, and/or provides parts and services for weapons, and it is very likely that your small business will fall under this category. Level 2 contractors will be implementing significantly more controls than they would in Level 1, as they must comply with the 110 cybersecurity safeguards laid out in NIST 800-171. The nice thing about CMMC 2.0, however, is that NIST 800-171 is now the only standard for Level 2 compliance, which means that the unique security practices introduced by CMMC 1.0 are no longer required. Note that NIST has recently announced plans to make some updates to the 800-171 standard, so the number of controls and the safeguards they task us with implementing could change. Approximately 40% of businesses in the DoD supply chain handles CUI, and therefore will need to focus on Level 2 or Level 3.
- Level 3 (Expert) – Formerly Level 4/5. Large prime contractors and those of us that work on super critical national security programs that are significant targets of nation-state adversaries and any Advanced Persistent Threat (APT) will have to focus on Level 3. These organizations handle CUI, but they also likely handle secret and, potentially, top-secret information. Level 3 requirements are derived from NIST 800-172, which details 35 advanced controls that a Level 3 organization must implement in addition to the 110 controls from NIST 800-171. The DoD estimates that fewer than 1000 members of its supply chain will be subject to Level 3.
What about assessments?
The assessment “ecosystem” the DoD tasked the CMMC Accreditation Body with nurturing sparked a lot of confusion under CMMC 1.0 and, thankfully, CMMC 2.0 has provided some changes to the assessment model and ecosystem. In CMMC 1.0, all DIB members would have to pay a CMMC third-party assessment organization (C3PAO) to assess our implementation of the controls required by our target CMMC Level, at least once every three years. According to the new model, self-assessments actually may be performed depending on a couple of factors: 1) the level your organization falls under and 2) the type of information you are protecting.
- Level 1 – All contractors in this group will be required to perform annual self-assessments. As the DoD puts it, these contractors are not protecting sensitive national security information, so there is no need for a third-party or government assessments. Companies will continue to use the Supplier Performance Risk System (SPRS) for submitting their self-assessment scores to the DoD, and they will also need to provide an affirmation from a senior official that they are meeting the FAR 17 requirements.
- Level 2 – Similar to Level 1, if the CUI a contractor handles does not include sensitive national security information, they will be allowed to perform an annual self-assessment. However, if they do handle this national security information, they will need to hire a C3PAO to assess them on a triennial basis. The DoD estimates about half of all Level 2 organizations (approximately 40,000 of us) will need to have a C3PAO assessment performed once the CMMC becomes law. At the time of this writing, there are only five authorized C3PAOs accredited by the CMMC-AB within the CMMC ecosystem.
- Level 3 – Self-assessments are not an option, as all contractors within this level will be assessed by a government team (probably the Defense Contractor Management Agency’s (DCMA) DIB Cybersecurity Assessment Center (DIBCAC)) on a triennial basis. C3PAOs will not be assessing for CMMC Level 3 compliance.
What about POA&Ms?
Under CMMC 1.0, for a contractor to be considered compliant, they must have implemented all controls required for their given level at the time of assessment. This means that Plans of Action & Milestones (POA&Ms), a detailed set of corrective action plans to remediate any deficient control implementation, were not allowed for the assessment – it was either a perfect cybersecurity program or nothing. It was odd that POA&Ms were not allowed, given that both the DoD’s own Risk Management Framework (RMF) and the NIST 800-171 standard allow the use of POA&Ms for ongoing cybersecurity risk management.
CMMC 2.0 rightfully made the change to allow for POA&Ms. However, this does not mean that a contractor can just throw everything into their POA&M and call it a day. The following is verbatim from the DoD’s new CMMC 2.0 website:
[CMMC 2.0] allows companies, under certain limited circumstances, to make Plans of Action & Milestones (POA&Ms) to achieve certification.
When it says, “under limited circumstances,” this is because there will be restrictions to both who can use POA&Ms as well as what cybersecurity controls will be allowed on POA&Ms. We know that the controls with the greatest significance will not be allowed, but these controls have not yet been identified. It appears POA&M allowance may be tightly coupled with the DoD 800-171 Assessment Methodology scoring criteria.
What does CMMC 2.0 mean for my small business right now?
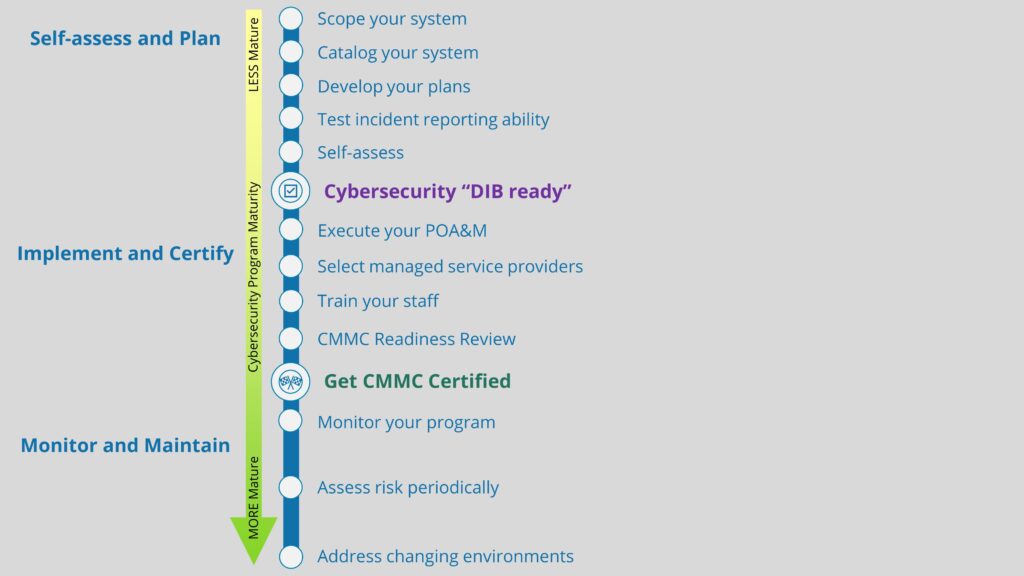
With the upending of CMMC 1.0, we know that it is going to take time for CMMC 2.0 to get up and running, probably in the neighborhood of one to two years. However, your small business should be careful to not think that this is an excuse to delay meeting these requirements. As a DoD contractor ourselves, we have realized that CMMC implementation is a journey – a long one at that – and a “sprint at the end” mentality will not work. The standards for CMMC certifications are high, which is why it is going to take considerable effort and time to get everything in order by the time of assessment. The DoD has done us all a favor by giving us considerably more runway here, but we cannot forget why we’re even doing all of this: to improve our cybersecurity so we can better protect our nation’s sensitive information. Delaying only gives the adversaries more time to wreak havoc and make off with this information.
That's all, folks
We know that the compliance journey is a stressful one, since the amount of information we are required to ingest and act upon is quite large. That’s why we run Workshops where we explain everything there is to know surrounding CMMC, NIST 800-171, and DFARS 252.204-7012. Additionally, we’ll help you build a System Security Plan (SSP), Plan of Action & Milestones (POA&M), and Incident Response Plan (IRP) customized for your organization. Using our Totem™ tool, you’ll also be able to manage everything needed for compliance in one central location.
As always, feel free to hit us up with any questions. We love talking about all this stuff!
Thanks for reading!
-Nathan