UPDATE 13-October-2025: NIST 800-88 revision 2 has been published. We’ve updated any references to NIST 800-88r1 in this post to the latest revision.
Important revisions in this version compared to SP 800-88r1 (2014) are as follows:
The document’s focus has shifted from providing guidelines for hands-on sanitization decisions to maintaining the confidentiality of sensitive information by establishing an agency or enterprise media sanitization program as part of media disposal or reuse.
Program-focused guidelines now improve the alignment of media sanitization with cybersecurity standards (e.g., SP 800-53, ISO/IEC 27040), update certain sanitization methods to be in tune with the state of practice, and address trust establishment in the vendor’s implementation of sanitization techniques for clear and purge sanitization methods.
Apart from cryptographic erase (CE), which is commonly used across all encrypted media, all sanitization techniques and tool details have been replaced with recommendations to comply with IEEE 2883, NSA specifications, or an organizationally approved standard.
A focused set of guidelines have been added to the CE technique to expand the types of cryptographic keys that may be used for CE, consolidate content from different parts of text to a dedicated section, provide guidelines for key sanitization using the state of practice ISO/IEC 19790 zeroization, and clarify when the use of externally managed keys is potentially acceptable.
To clear, to purge, or to destroy? Indeed, that is the question.
Since dumpster diving grew in popularity during the 1980s, businesses have shown increased awareness regarding how they dispose of sensitive information. In today’s digital world, sensitive information disposal extends beyond what you throw in the trash, now encompassing even how you clear the files on your computer. Safe disposal of sensitive data is crucial for all Internet users, but for Department of Defense (DoD) contractors that are handling Federal Contract Information (FCI), including FCI’s more sensitive subset Controlled Unclassified Information (CUI), federal regulations require a specific disposal process to be followed. A DoD contractor’s adherence to these requirements, namely their implementation of NIST SP 800-171, will soon be evaluated as part of a Cybersecurity Maturity Model Certification (CMMC) assessment.
In this post, we will summarize the requirements for CUI and FCI sanitization, and we will share how to know when one sanitization strategy is appropriate compared to another. If you want to learn more about these requirements, feel free to grab a seat in our next CMMC / NIST 800-171 Workshop!
The NIST 800-171 requirements for FCI / CUI sanitization
NIST 800-171 has two requirements for CUI sanitization:
Ensure equipment removed for off-site maintenance is sanitized of any CUI.
NIST 800-171 Control 3.7.3
Sanitize or destroy system media containing CUI before disposal or release for reuse.
NIST 800-171 Control 3.8.3
We’ll circle back to control 3.7.3 later in this post. As for 3.8.3, it’s important that we clarify that this control applies to sanitization of all FCI, not just CUI (CUI is a subset of FCI). How do we know this? We can refer to FAR clause 52.204-21, which outlines the federal contractor cybersecurity requirements for protecting FCI and what to expect for those pursuing CMMC Level 1. In this framework, we find the following:
Sanitize or destroy information system media containing Federal Contract Information before disposal or release for reuse.
FAR 52.204-21(b)(1)(vii) / CMMC Practice MP.L1.3.8.3
In other words, this is considered a CMMC Level 1 control, and it therefore applies to sanitizing all FCI, not just CUI. All Level 1 controls are also included for those pursuing a CMMC Level 2 certification. This is somewhat “hidden” in the sense that it isn’t apparently obvious, since the NIST 800-171 documents only specify sanitization of CUI. But for those pursuing CMMC, assessors will want to see that you’re sanitizing all FCI.
The assessment objectives for 3.7.3 are the following:
System media containing FCI/CUI is sanitized or destroyed before disposal.
NIST 800-171A Assessment Objective 3.8.3[a]
System media containing FCI/CUI is sanitized before it is released for reuse.
NIST 800-171A Assessment Objective 3.8.3[b]
When you undergo your CMMC assessment, the assessors will use these objectives to determine if you are properly sanitizing FCI/CUI. See the following section for explanations of both objectives.
What does it mean to sanitize media containing FCI/CUI?
Let’s say a small business DoD contractor manufactures components which are later used in building heavy machinery. The company likely handles FCI and CUI in both physical (paper) and digital (electronic files) form.
Assume engineering drawings, marked CUI, are handled in digital form and are stored locally on employee workstations while in use. As soon as the FCI/CUI touches the local workstation hard drive, that drive becomes “contaminated” in the sense that it must be sanitized (and other 800-171 requirements not discussed here, such as hardening or FIPS-validated cryptography, may also apply). However, sanitization does not always need to occur right away nor does it only imply destruction. For instance, say an engineer working for this small business decides to leave the company for another job. The company collects the employee’s workstation and, given that it is still in good condition, wants to re-issue it once the employee’s replacement is found. However, the engineer regularly handled CUI engineering drawings, so the drive must be sanitized before the workstation is passed off to the next employee.
What must the company do? 800-171 control 3.8.3 does not expound upon what is meant by “sanitize”, though if you read the Discussion portion of the control, you’ll see that it references another NIST document, 800-88. This is a very important document that you will want to use to determine your organization’s sanitization strategy. Within the document, you’ll find that sanitization means taking one of three courses of action (Clear, Purge, Destroy — each of which we’ve summarized in lay terms):
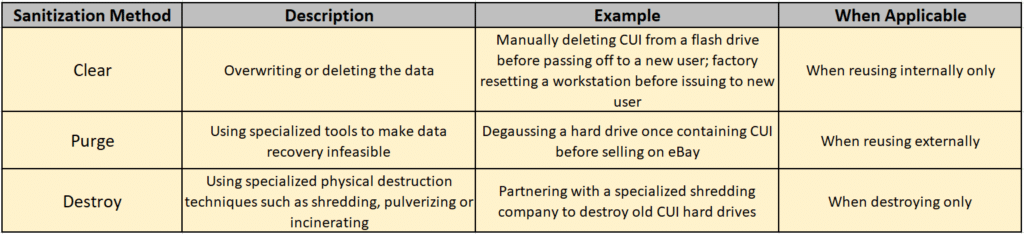
If you intend to reuse media internally that contains FCI/CUI, you can sanitize that FCI/CUI simply by overwriting it, which means using specialized software to erase all traces of information from the drive. Note that simply deleting the FCI/CUI files is not enough, as right-click–>delete only deletes disk references to the file location, and not the file itself. In the case of onboarding a new user and reusing a prior workstation, it may be easier from an IT administration standpoint to just factory reset the device, which also is a sufficient method of clearing.
When it comes to external reuse of FCI/CUI-laiden media, such as selling the old hard drives online, clearing is not sufficient. You will need to purge the drives, which could include taking either logical or physical sanitization measures. Logical purging of hard drives/SSDs that support encryption can be done using a Cryptographic Erase function. From our observation, small business DoD contractors tend to not have the interest in dissecting and following the nuances of logical purging of their FCI/CUI media, and they tend to steer away from this option. It’s important to note that physical purging methods, such as degaussing, effectively render the media unusable, ultimately defeating the purpose of reselling (exception being selling non-hard-drive components for spare parts, perhaps).
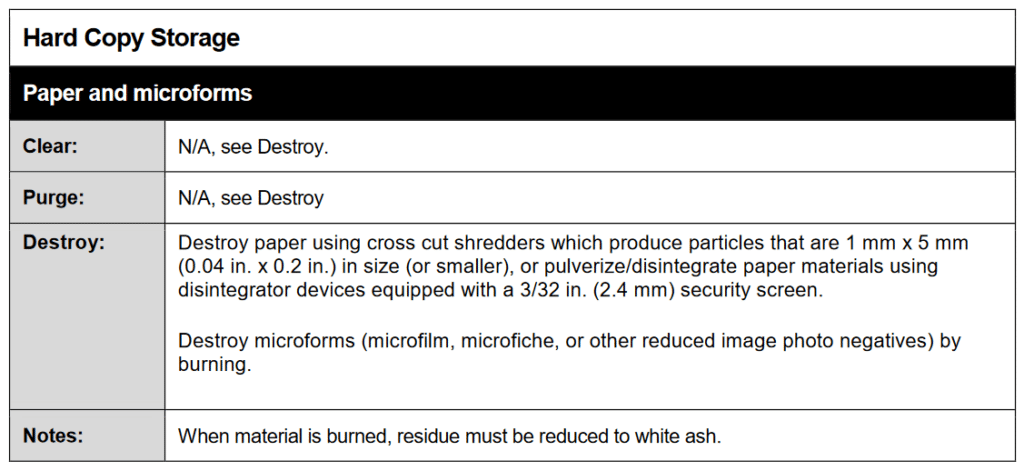
You may decide to just avoid the hassle and have the media destroyed once you’re ready to dispose of it. Unfortunately, destruction of FCI/CUI-laiden media is not as simple as drilling a few holes through the drive or taking your frustration out via a sledgehammer. For the media devices, per NIST 800-88, you’ll need to have them disintegrated, pulverized, melted, or incinerated (who said CMMC wasn’t fun?). For paper FCI/CUI or other “flexible media”, meaning media that has been removed from its outer protective container, shredding is an option. However, even your standard paper shredder won’t suffice, as specific shredding dimensions (1mm x 5mm or smaller — see image below) are needed. These nuances are described beginning on page 27 of NIST 800-88, where sanitization requirements for different media types are listed. For example, if you handle paper FCI/CUI, you’ll need to sanitize in the following fashion:
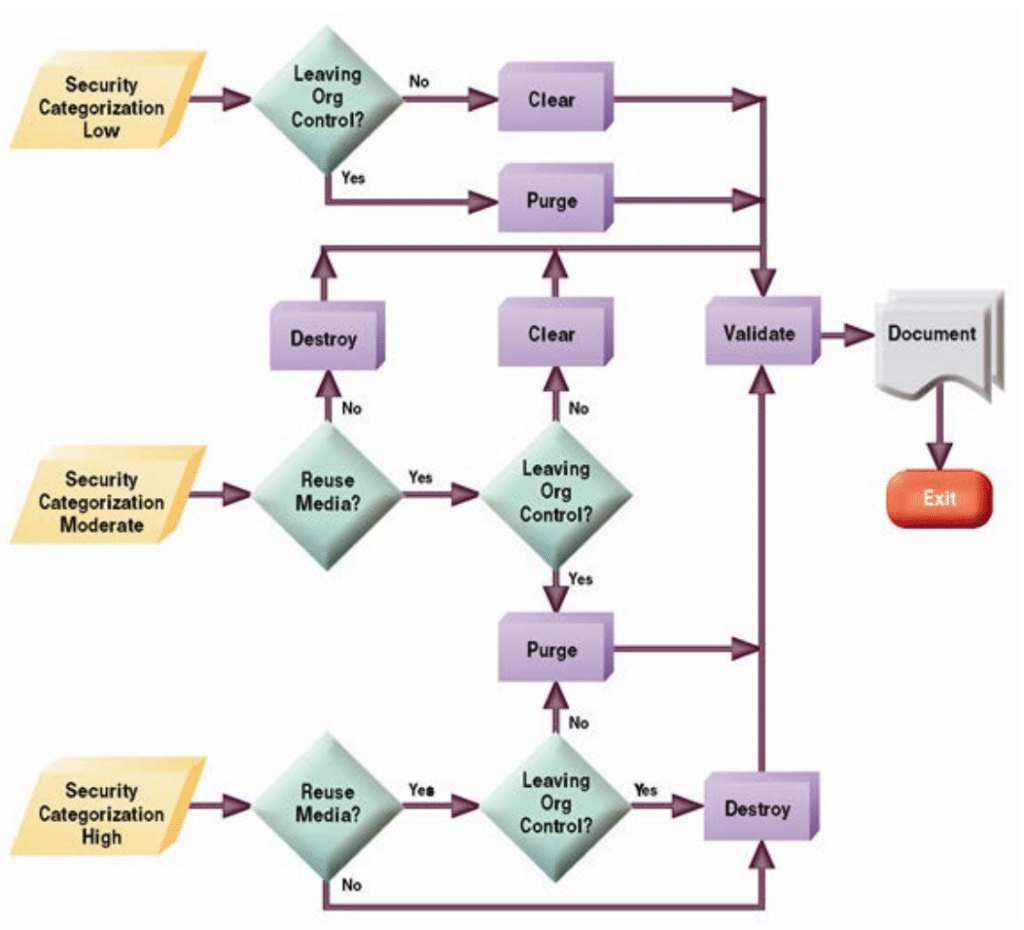
NIST also offers a handy decision flowchart depicting sanitization actions to take depending upon certain conditions. CUI has the Security Classification of “Moderate”, so follow the middle path in the flowchart:
When it comes to destruction, we all inevitably arrive at the conclusion that this is something we’ll need to outsource to a media destruction company. See the next Recommendations section for more on this.
Examples of FCI/CUI sanitization process
Now that you understand some of the methods by which a small business DoD contractor should sanitize its FCI/CUI, let’s look at a few examples. We’ll refer to the decision flow pictured in the prior section to determine which sanitization steps must be taken.
A small business DoD contractor previously stored CUI documents on an old unencrypted USB flash drive. To comply with NIST 800-171 encryption requirements, the organization acquires a new FIPS-validated external hard drive. It transfers the CUI from the old USB to the new encrypted hard drive, overwrites (clears) the CUI from the old USB using a software overwriting tool, validates that the CUI has been removed, and stores the USB for later reuse. Though CUI no longer resides on the USB, given that it was at one point “contaminated” with CUI, it is marked for destruction at the end of its lifecycle. The organization maintains a sanitization log and documents all sanitization actions taken. If new sanitization processes are introduced, the organization documents these in its SSP.
An engineer employed by a small business DoD contractor is maintaining CUI drawings on his workstation. The workstation is old and is beginning to run slow, so the engineer requests a new one be purchased, and the request is approved. The engineer transfers all data from the old workstation to the new one. He removes the old CUI hard drive from the workstation and locks it away for eventual destruction. The organization hires a shredding service (that agrees to the NIST 800-88 sanitization standard, see below) to destroy the CUI hard drive and any other FCI/CUI paper or media, and receives a destruction certificate from the shredding service validating that the destruction occurred. The organization maintains a sanitization log and documents all sanitization actions taken. If new sanitization processes are introduced, the organization documents these in its SSP.
A small business DoD contractor handles paper CUI in the form of travelers and engineering drawings. Once the paper CUI is no longer needed, it is disposed of in a locked shredding bin for eventual destruction. The organization hires a shredding service (that agrees to the NIST 800-88 sanitization standard, see below) to destroy the paper CUI, and any other FCI/CUI marked for destruction, and receives a destruction certificate from the shredding service validating that the destruction occurred. The organization maintains a sanitization log and documents all sanitization actions taken. If new sanitization processes are introduced, the organization documents these in its SSP.
Assuming other industry requirements are not at play, and that the media never once stored FCI or CUI, no actions are required. However, if the media contains sensitive information pertinent to business operations, it is recommended that a sanitization process be followed.
Recommendations for FCI/CUI sanitization
We recommend that, once your organization has deemed its FCI/CUI media has reached its end of life/internal reuse, it set aside the media and lock it away (following 800-171 requirements for physical security), then destroy and dispose of it. This would include locking away the FCI/CUI-laiden digital media components, such as hard drives, SSDs, and/or flash drives, as well as any paper FCI/CUI. There is no requirement in NIST 800-171 or 800-88 as to how frequently FCI/CUI needs to be destroyed, though a cadence still should be established and described in your System Security Plan (SSP). Most companies accumulate paper media quicker than digital media (old flash and hard drives), so you’ll probably want to destroy paper media more frequently than digital media. One option for digital media is to hang on to it (locked away) and then destroy the media either every three years or when a major event occurs within the company (whichever occurs first), such as acquisitions or closing of the business.
Next, when it’s time to find a media destruction company, many vendors will claim to offer “secure” destruction services. “Secure” is subjective and can be misleading, but NIST 800-88 is pretty clear what is expected. Ensure the vendor’s destruction capabilities align with NIST 800-88, (especially the shredding dimensions needed). If the vendor’s processes do align with 800-88, it’s very likely that they will be touting it. When it comes to a CMMC assessment, the assessors will likely ask which vendor you are using and may request to see the vendor’s sanitization processes as compelling evidence.
Finally, as alluded to earlier in this post, there is another NIST 800-171 control concerning CUI sanitization: 3.7.3. This control (only applicable to CUI and those pursuing CMMC Level 2) requires that any IT components be sanitized of CUI before they are taken off-site for maintenance. We recommend, if possible, forbidding the off-site maintenance of IT components that store CUI locally, such as servers or workstations, and instead destroy and replace those media devices when necessary. Other IT components, such as printers, can be a little more tricky to address, given that often they are leased out. Any printers designated for off-site maintenance should be inspected by the organization prior to removal to ensure they have been sanitized of CUI. For instance, the organization can ensure that the printer’s memory has been purged and it is configured not to store copies of information on the internal hard drive. If your organization has already established secure baselines for its IT components (another 800-171 requirement…), you should verify the recently-repaired component against your secure baseline.
Wrapping up
This post described the sanitization requirements for FCI and CUI in accordance with NIST 800-171 and NIST 800-88. We looked at different methods for sanitization, when one method would be applicable compared to another, and what to keep in mind as you pursue CMMC compliance.
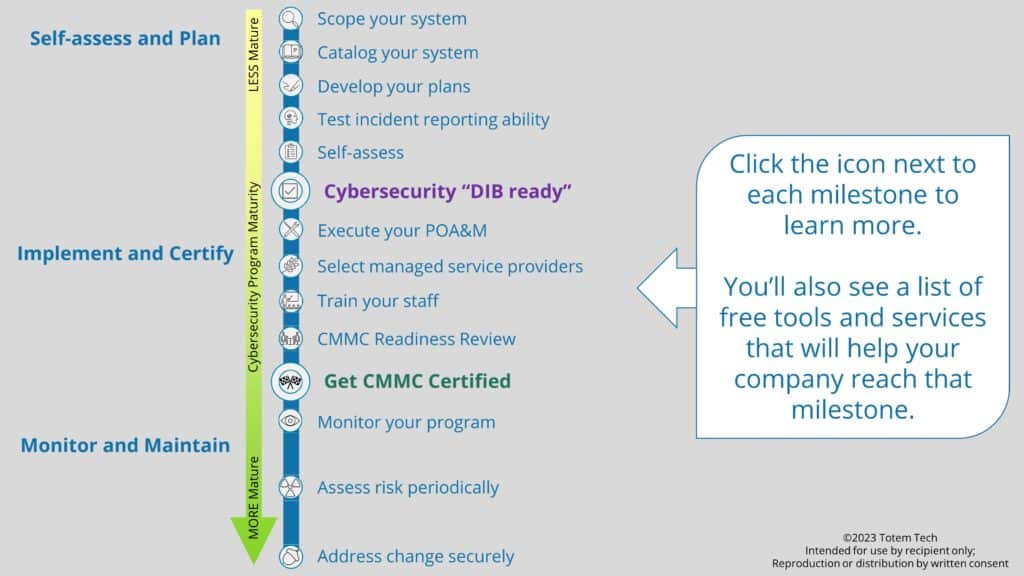
CUI sanitization is a critical component to ensuring CMMC compliance. For an overview of all the steps needed to ensure you are “Cybersecurity DIB Ready”, browse our CMMC Compliance Roadmap or download it below. Or if you’d like a little help along the way, we invite you and your staff to grab a seat in our next CMMC Workshop. We cover media sanitization in-depth in one of our Workshop lessons!
Keep fighting the good fight!
–Nathan