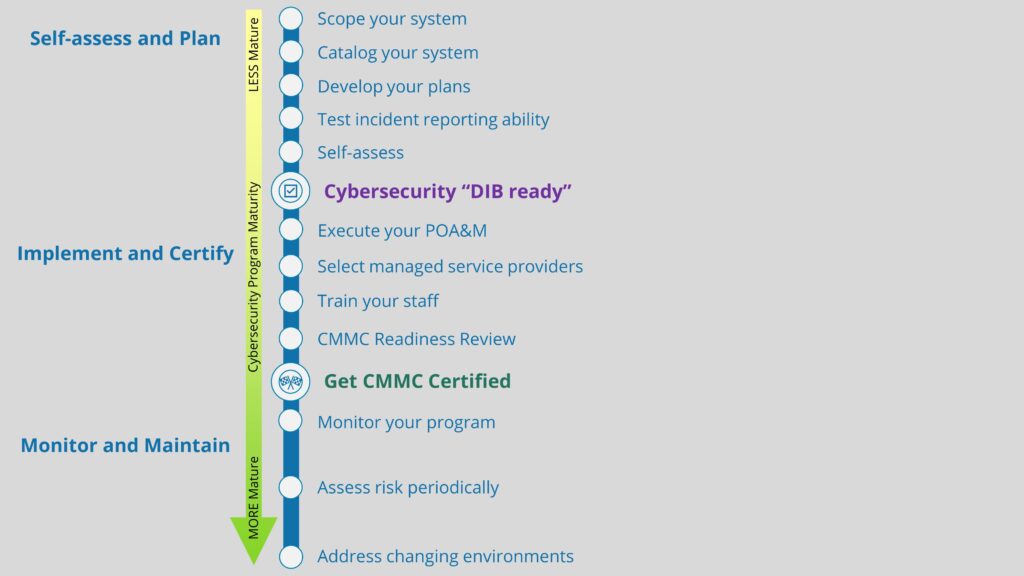
Department of Defense (DoD) contractors that handle Controlled Unclassified Information (CUI) are required, under DFARS clause 252.204-7012, to implement the 110 cybersecurity safeguards outlined in NIST SP 800-171. Our implementation of NIST 800-171 will eventually be assessed as part of receiving a CMMC certification. To prove that we have implemented NIST 800-171 correctly and pass a CMMC assessment, we will need to provide both justification AND evidence (what we will refer to as “objective” or “compelling” evidence) as to why and how we have fulfilled the underlying NIST 800-171A assessment objectives. Essentially, we must be prepared to prove to CMMC assessors that we have implemented the cybersecurity safeguards we claimed to have implemented in our System Security Plan (SSP). In this post, we will provide some objective evidence considerations for DoD contractors as they prepare to receive a CMMC certification. We will also look at examples of objective evidence for CMMC Level 1 controls to get you started.
What is objective/compelling evidence for CMMC?
We preface this post by stating that we are not lawyers, and this is not legal advice. Additionally, it’s not yet clear the specific process the CMMC assessors will use when assessments begin (though a draft version of this process was released July of 2022, and it’s… yikes!). Therefore, it may be valuable for your organization to seek legal counsel as you cover your bases for CMMC. However, this didn’t stop us from jotting down our own thoughts on this topic.
Objective evidence refers to evidence based purely on fact. It exists independent of personal bias or interpretation (what we call subjective evidence), and therefore can be observed, tested, measured, or verified in some way. Consider a situation where there is a car crash involving two drivers, and they both claim that the other driver is at fault for the accident. In order to determine who is responsible for the damages, objective evidence will be needed. This could include a police report documenting the scene of the accident, security camera footage, photos, eyewitness statements, and other observable elements. Without objective evidence, it becomes very challenging to prove that one driver was liable over the other, as only subjective evidence is available.
In the same way, DoD contractors will need to provide objective evidence that they have implemented the cybersecurity protections they stated within their SSP. Subjective evidence will not suffice for passing a CMMC assessment. The assessors will be looking to observe, test, measure, or verify your claims in some way. This means that those contractors pursuing a CMMC Level 2 certification should be prepared to provide objective evidence for all 320 assessment objectives within NIST 800-171A, if asked to do so. The nice aspect of this is that there are many different ways you can provide objective evidence, especially through documentation or examples of technical configurations. Additionally, there is some overlap in the NIST 800-171 framework, so objective evidence for one control or assessment objective may be used to support another control or objective. We’ll flesh this out more in the coming sections.
To differentiate between subjective and objective evidence in the context of a NIST 800-171 control, consider the third assessment objective for Awareness and Training safeguard AT.L2-3.2.1:
Managers, systems administrators, and users of the system are made aware of the security risks associated with their activities.
AT.L2-3.2.1[c]
A DoD contractor may approach this action differently using subjective and objective evidence:
| Type of Evidence | Example |
|---|---|
| Subjective | Stating that the organization's employees are aware of company policies and have been trained to identify and report cybersecurity threats. |
| Objective | Providing documented proof of the training, including the training material, attendance records, or employee acknowledgement forms (such as a signed Acceptable Use Policy). |
Note that the subjective approach in this case is not necessarily fallacious or bad; it just isn’t enough to be considered proof. You may very well have similar language in your SSP, which is fine, so long as it describes in detail how your organization is implementing/achieving that objective. Then, couple this justification with objective evidence, and you should be in good shape.
That’s an overview of objective vs. subjective evidence in the context of CMMC compliance. If you have read this far and find yourself totally lost, consider grabbing a seat in our next CMMC Workshop, where we cover all the essentials of CMMC compliance in detail. If you’re ready to dig in deeper, read on!
Examine, Interview, Test
If you’ve had the pleasure of reading through NIST 800-171A, you may have noticed a section titled “Potential Assessment Methods and Objects” under each 800-171 control and its corresponding objectives. This section highlights three methods an assessor may use to conduct an assessment: Examine, Interview, and Test. These relate directly to verifying claims made in your SSP by inspecting the objective evidence you provide.
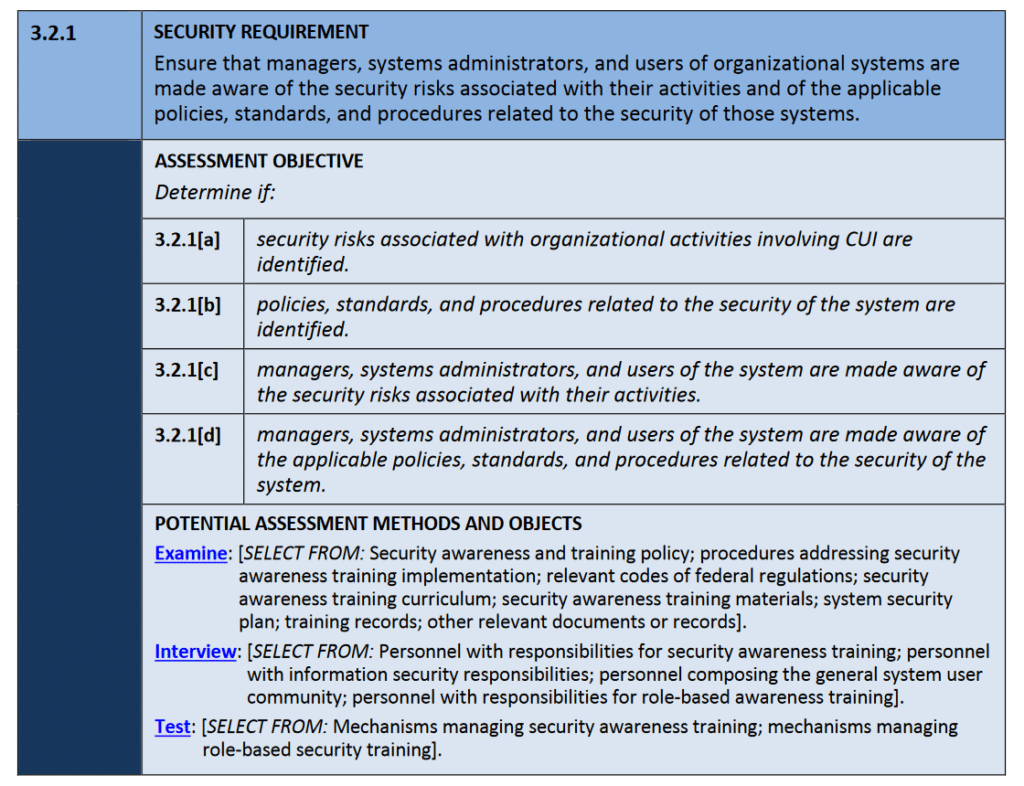
We recommend that you consider these assessment methods and objects as you gather your objective evidence. For instance, when addressing cybersecurity training requirements in AT.L2-3.2.1[c], you should be prepared to provide:
- materials to be examined, including training records or phishing simulation results,
- staff to be interviewed, including both those with IT/security-specific duties or general user responsibilities,
- mechanisms to be tested, including the training platforms in use or the functionality for reporting phishing emails.
It’s not likely that assessors will ask for all three assessment methods for all 320 assessment objectives. In some cases, it may not make sense to use one or more of the assessment methods. However, as we have learned with CMMC up to this point, it’s better to ensure our bases are covered than to cut corners or to do nothing. So, we recommend that your objective evidence aligns with these assessment methods and that you are prepared to provide all of them at any time. In the next section, we’ll provide some other examples of objective evidence for CMMC Level 1 controls for you to consider.
Objective evidence examples for CMMC L1
To help get you started, we have put together a table outlining examples of objective evidence for all CMMC Level 1 controls. Please keep in mind that these cover the control level, not the assessment objective level, the latter of which is more granular and what the assessors will be seeking evidence for. These examples are to help with the brainstorming, and you can decide which assessment objective(s) to apply them to.
| Control | Description | Objective Evidence Examples |
|---|---|---|
| AC.L1-3.1.1 | Limit information system access to authorized users, processes acting on behalf of authorized users, or devices (including other information systems). | Examine: List of users within Active Directory Test: Show how user permissions are limited in Active Directory |
| AC.L1-3.1.2 | Limit information system access to the types of transactions and functions that authorized users are permitted to execute. | Examine: Groups defined within Active Directory Test: Show how group permissions are limited in Active Directory |
| AC.L1-3.1.20 | Verify and control/limit connections to and use of external information systems. | Examine: List of external systems accessed by organization Examine: List of internal systems accessed outside organization Interview: Personnel involved in approving/configuring external access |
| AC.L1-3.1.22 | Control information posted or processed on publicly accessible information systems. | Examine: Records from monthly review of publicly available information systems to ensure no CUI is present Interview: Personnel involved in performing this review |
| IA.L1-3.5.1 | Identify information system users, processes acting on behalf of users, or devices. | Examine: List of users within Active Directory Examine: List of processes acting on behalf of authorized users Examine: List of approved system devices |
| IA.L1-3.5.2 | Authenticate (or verify) the identities of those users, processes, or devices, as a prerequisite to allowing access to organizational information systems. | Examine: Group Policy Object (GPO) in Active Directory for requiring credentials Test: Show that unidentified users/devices cannot connect to system |
| MP.L1-3.8.3 | Sanitize or destroy information system media containing FCI/CUI before disposal or release for reuse. | Examine: Data sanitization policy Examine: External data sanitization vendor process Test: Demonstrate sanitization process |
| PE.L1-3.10.1 | Limit physical access to organizational information systems, equipment, and the respective operating environments to authorized individuals. | Examine: List of employees issued keys/RFID badges and their allowed access points Test: Demonstrate that restricted areas are only accessible by authorized individuals |
| PE.L1-3.10.3 | Escort visitors and monitor visitor activity. | Examine: Visitor log book Examine: Security camera recordings |
| PE.L1-3.10.4 | Maintain audit logs of physical access. | Examine: Visitor log book Examine: Employee RFID access logs Test: Demonstrate how employee RFID access logs are gathered and monitored |
| PE.L1-3.10.5 | Control and manage physical access devices. | Examine: List of employees issued keys/RFID badges and their allowed access points Examine: Policy describing how access devices are disabled when an employee leaves the organization Test: Demonstrate that facility is secured when correct alarm codes are entered |
| SC.L1-3.13.1 | Monitor, control, and protect organizational communications (i.e., information transmitted or received by organizational information systems) at the external boundaries and key internal boundaries of information systems. | Examine: Diagram outlining network infrastructure design Examine: List of existing firewall rules Test: Show how Network Traffic Analysis tool is used to monitor environment |
| SC.L1-3.13.5 | Implement subnetworks for publicly accessible system components that are physically or logically separated from internal networks. | Examine: List of self-hosted email or web servers Test: Show how self-hosted email or web servers are separate from corporate network |
| SI.L1-3.14.1 | Identify, report, and correct information system flaws in a timely manner. | Examine: Email report of identified vulnerabilities Examine: Meeting minutes from IT meetings where vulnerabilities were discussed and corrected |
| SI.L1-3.14.2 | Provide protection from malicious code at appropriate locations within organizational information systems. | Examine: List of system components with antivirus installed Test: Show how antivirus solution is installed, configured, licensed, and updated Test: Show how antivirus provides real-time protection |
| SI.L1-3.14.4 | Update malicious code protection mechanisms when new releases are available. | Test: Show antivirus vendor process for applying updates Test: Show how antivirus is updated Test: Show how antivirus is flagged if out of date |
| SI.L1-3.14.5 | Perform periodic scans of information systems and real-time scans of files from external sources as files are downloaded, opened, or executed. | Examine: List of performed antivirus scans Test: Show configuration for frequency of antivirus scans Test: Show how antivirus provides real-time protection |
There you have it, a quick list of objective evidence examples for all CMMC Level 1 controls. If you are pursuing Level 2, you will want to do this for all 320 assessment objectives. Again, as you may have noticed browsing through the chart above, there is some overlap between controls, so objective evidence you use for one control may be useful for supporting another.
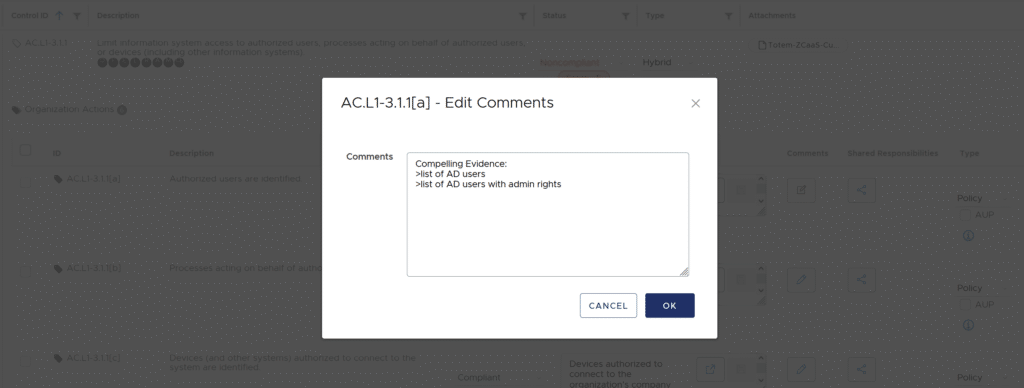
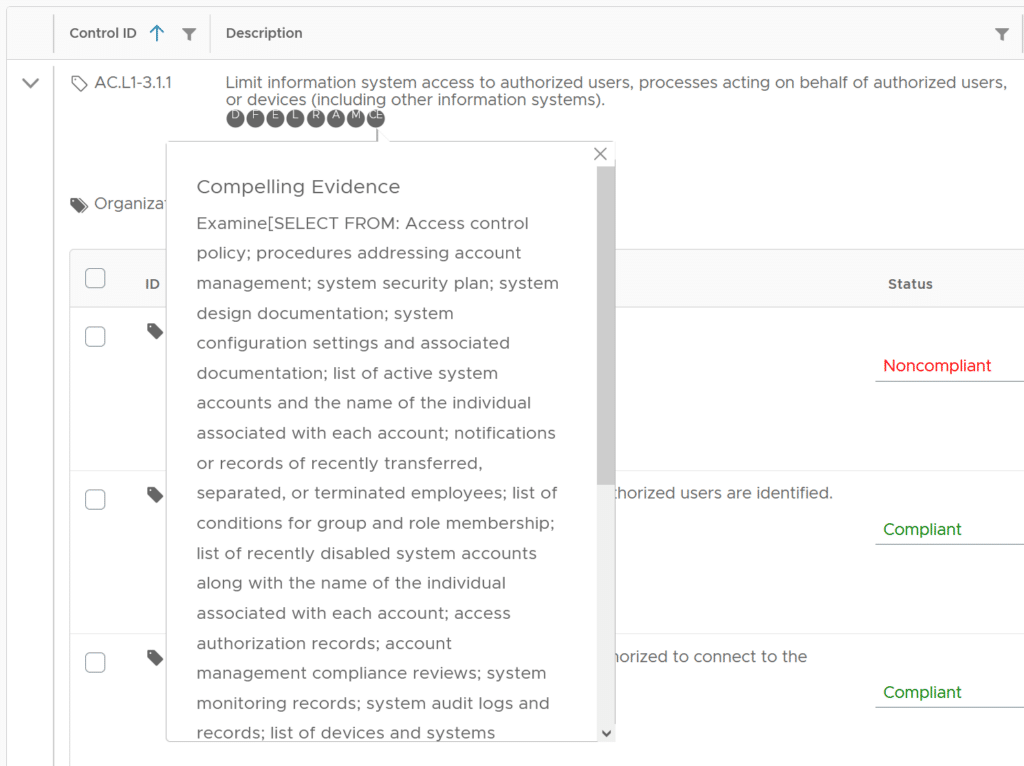
By the way, our Totem™ Cybersecurity Compliance Management tool has a designated field for you to identify compelling evidence for all 320 objectives. You can also easily refer to the NIST 800-171A Potential Assessment Methods and Objects, which are baked into the tool as well. Additionally, users can leverage existing templates that we have created to reduce the paperwork burden, including identifying compelling evidence. Let us know if you’re interested or want to request a free trial!
Wrapping up
In this post, we defined objective/compelling evidence and the role it is intended to play in passing a CMMC assessment. We then discussed the expected methods assessors will use to analyze our objective evidence, then concluded by brainstorming examples of objective evidence for all CMMC L1 controls. If you have made it to the end of this post, you should feel prepared to begin gathering your own objective evidence.
If you find you want a little more help, Totem stands ready to support. Come grab a seat in our next CMMC Workshop, or engage us for a CMMC Gap Assessment, where we will do the heavy lifting in assessing your cybersecurity program, building necessary policies and corrective action plans, and identifying objective evidence. If you have questions about this blog, CMMC, or cybersecurity in general, drop us a line!
Keep fighting the good fight!
–Nathan Cross, Cybersecurity Engineer