More and more of Totem’s clients have received cybersecurity compliance questionnaires from their customers, as part of due diligence activities in a supply chain risk management process. These questionnaires have been sent to our clients through supply chain management portals such as Exostar, or directly via email as spreadsheets. In this post, we provide some suggestions on how DoD contractors can respond to such a questionnaire when it is based on the National Institute of Standards and Technology Cybersecurity Framework (NIST CSF).
The questionnaire, aka “attestation”, contains a list of expected cybersecurity safeguards, and the responders (you) are required to identify which safeguards your organization has implemented to protect your customer’s (the requestor’s) data. The responder is expected to provide evidence of implementation, and to address non-implemented controls with details and a timeframe for implementation. The customer will use your responses to assess the level of risk your organization (as a supplier) represents to their sensitive information. If you haven’t yet, your organization will probably also see similar cybersecurity risk questionnaires from your insurance providers, especially if you have a cybersecurity policy with them.
Provenance of the NIST CSF questionnaires
In the past, we saw a lot of the attestations, especially through Exostar, use the SANS Critical Security Control (CSC) framework as the list of safeguards to respond to. (Although some Exostar managers annoyingly seem to require answers to an older version of the Critical Security Controls (CSC) GRRR!!).
Lately however, we are seeing the NIST Cybersecurity Framework (CSF) as the “standard” used in more of these questionnaires. (SpaceX, for example, relies on the CSF in its vendor/supplier questionnaire.) The CSF is lovely and widely adopted, so we are happy about this. However, as we explained in this post, the CSF is a framework, not a standard, and so the response process can be made easier by identifying the controls in a more granular (and more easily “assess-able”) standard that correspond to the CSF. We call this process “mapping” or “doing a cross-walk”. Mapping allows the responder to provide more meaningful responses. Luckily for those of our clients that are in the DoD supply chain and subject to NIST 800-171 controls for the protection of Controlled Unclassified Information (CUI), NIST provides a CSF <–> 800-171 mapping. This mapping will help responders (you) address the NIST CSF questionnaire.
However, there are some caveats and considerations:
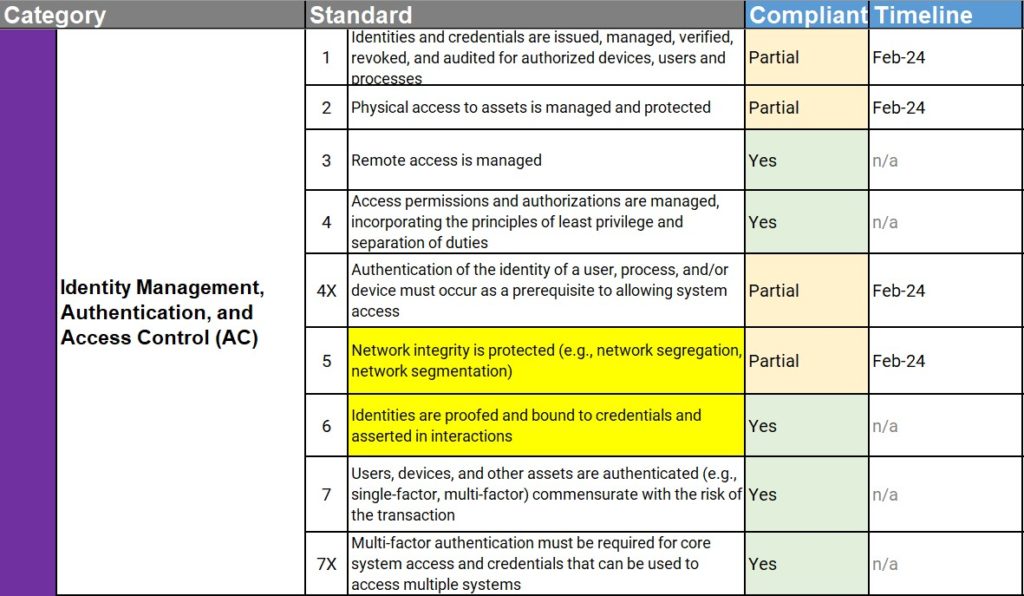
The questionnaire will list the NIST CSF ID (e.g. “ID.AM-1”) and the description (e.g. “An inventory of devices and systems exists and is maintained.”), and ask the responder to fill out information in the following columns (these are the typical columns; your particular questionnaire may have slightly different wording):
Compliant? (Yes/No/Partial)
Timeline (For implementation if not fully Compliant)
Evidence (Description of proof that the requirement has been implemented.)
Notes
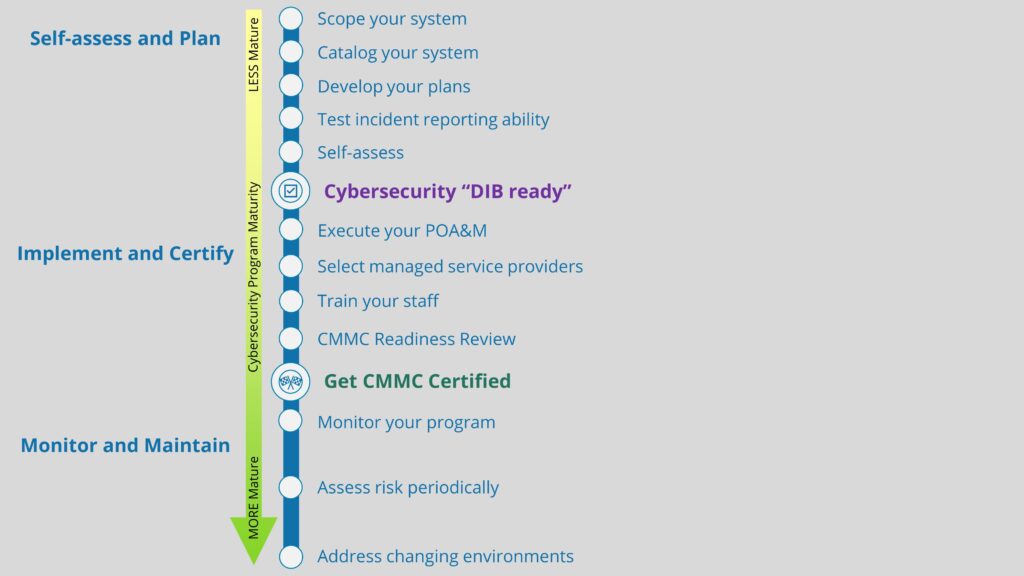
The requestor may “tailor” the CSF to add or remove some of the requirements. (SpaceX has what they call the “Enhanced” Attestation, in which they add additional requirements to the base NIST CSF.) The controls listed with an “X” in control number in the main image of this post are examples of these “Enhanced” controls from SpaceX.
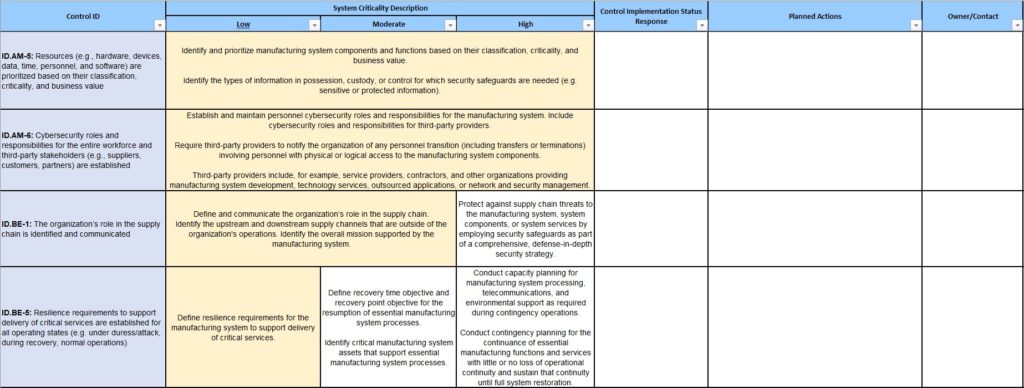
Sometimes this tailoring will include a “System Criticality Description”, where the cybersecurity safeguard requirement will differ based on whether the customer feels their information is of Low, Moderate, or High sensitivity. You’ll need to reconcile these criticality-tailored controls against the NIST 800-171 control set. The image below shows an example of such a CSF-based questionnaire tailored for criticality.
The NIST CSF <–> 800-171 mapping does not address all the CSF requirements. In other words, there are more CSF requirements than NIST 800-171 controls. And more than one 800-171 control may be used to address a single CSF requirement. CSF and 800-171 are therefore not “one-to-one”. So this attestation process is not exactly straightforward.
Our suggestions for how DoD contractors can respond to a NIST CSF attestation
Here are our suggestions for approaching a NIST CSF questionnaire / attestation, if your organization is implementing NIST 800-171:
Available from NIST: CSF <–> NIST 800-171 mapping worksheet.
Make a new column in the NIST CSF attestation worksheet. Title the column “800-171 equivalent” or something like that, and copy each related 800-171 “CUI Requirement” (control(s)) from the mapping spreadsheet (which you downloaded in step #1) to the appropriate row in the attestation. This mapping provides a reference point for marking the status of each CSF control, as you’ll do in step #3.
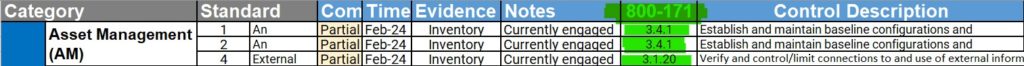
You can now reference the Compliance status for the 800-171 controls in your self-assessment (You can find this on the Control Status page if you’re using our Totem™ tool, or in the “Organizational Answer” column if you’re using our free SPRS scoring worksheet). Mark the Compliant status in the requestor’s NIST CSF attestation worksheet accordingly.
- If you have completed your NIST 800-171-based System Security Plan (SSP), you now have a policy for at least all the CSF requirements that have a mapping to 800-171, so at a minimum those controls should be marked “Partial” in the Compliant? column. If your self-assessment says “Implemented” or “Compliant” for all the associated controls, mark the attestation spreadsheet as “Yes”.
- If your self-assessment (or the Totem tool) says “Noncompliant” or “Not Implemented”, mark the attestation Compliant? column as “Partial”. Partial because you at least have the policies captured in your SSP, even if the policies aren’t fully enforced through safeguard implementation.
- If you haven’t completed at least the policy building in your SSP for any of the CSF requirements, you’ll need to mark the Compliant? column as “No.”
In the Evidence column for all the mapped controls, we recommend not getting too specific. You don’t know — and don’t have any control over — who the audience for this attestation is. So you don’t want to give up the “keys to the kingdom”, so to speak. In essence, don’t provide too many specifics about your cybersecurity program to an audience you aren’t sure of. We suggest stating something like this (customize the bracketed sections for your company’s specifics):
“<Your organization name> maintains a DFARS 252.204-7012-compliant NIST 800-171-based System Security Plan (SSP), Plan of Action and Milestones (POA&M), and Incident Response Plan (IRP) along with the following associated artifacts: Acceptable Use Policy, SSP Introduction, CUI and System Inventory, Security Engineering Process Guide, Configuration Management Plan, Computer Incident Response Aid, Network Topology and Data Flow Diagram. <Your organization> maintains the plans in <a 3rd-party compliance management tool [the Totem tool; replace as necessary with a description of how you maintain the plans]> and the artifacts in our Quality Management System (QMS) [or equivalent document control process]. <Your organization> will be pleased to host a virtual review of these plans and artifacts, if desired.”
Once you have addressed the Evidence column in the NIST CSF questionnaire, you’ll need to analyze the leftover non-800-171-mapped CSF requirements. It may take several hours to do this analysis and you may need to get creative in your response.
Some of these leftovers will actually be mapped to 800-171 despite what NIST’s mapping spreadsheet says. A good example of this is CSF requirement PR.AC-6, “Identities are proofed and bound to credentials and asserted in interactions”, which is not listed on the mapping but ties directly back into the first two controls in the 800-171 IA family: 3.5.1 and 3.5.2. You just need to map some specific 800-171 controls to those requirements on the attestation, and address the Compliant? and Evidence fields as described in #3 and #4 above.
Some of the leftovers will not map so easily. For instance, some contractors require their vendors to develop a supply chain risk management (SCRM) plan, if one doesn’t already exist. No such requirement exists in NIST 800-171, so your organization will have to develop an SCRM. NIST provides guidance for SCRM, but Totem can also help!
For any 800-171-mapped requirements marked “Partial” or “No” in the Compliant? column of the NIST CSF attestation, you’ll need to mark in the Timeline column the estimated completion date for those related NIST 800-171 controls. You should have developed a Plan of Actions and Milestones (POA&M) for any non-compliant NIST 800-171 controls. So, simply copy and paste the Estimated Completion Date for those related 800-171 controls from your POA&M into the corresponding row in the NIST CSF attestation worksheet.
For non-mapped CSF requirements, you’ll need to determine how long it will take you to implement those requirements and mark the Timeline column accordingly.
Summary and wrap up
The bottom line when faced with a NIST CSF based cybersecurity questionnaire is that the CSF is pretty high level, and to effectively attest to its implementation you’ll need to map that framework to a “rubber meets the road” standard. DoD contractors handling CUI have to meet such a standard anyway: NIST 800-171. So you can “map” NIST 800-171 to the NIST CSF (NIST provides the crosswalk document) and answer the questionnaire accordingly.
We understand this may be a lot to try to absorb from a post. If you’re struggling with filling out an attestation, contact us to schedule a working session and we’ll be happy to help. If you don’t have an SSP or any of the artifacts mentioned in step #4 above, check out our free tools page.
We also conduct hands-on DoD contractor cybersecurity Workshops multiple times a year, so if your organization needs help meeting its DFARS 252.204-7012, NIST 800-171, and/or CMMC obligations, consider joining us!
Good Hunting!
-Adam