Insider Threat - "The Nut in Front of the Keyboard"
Commonly, the first thing that comes to mind for the term “threat to cybersecurity” is a firewall, data server, or other technical device failure of some kind. Based on my experience, the biggest “threat to cybersecurity” device on the network is typically the nut in front of the keyboard. Meaning, it’s the employees who have direct access to an organization’s sensitive resources that typically cause the most havoc. Recently, a nationally reported event of a fellow veteran reinforced that notion to me.
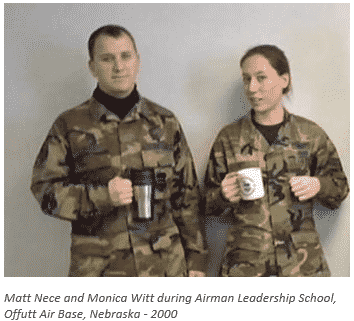
Monica Witt was in the Air Force from 1997 to 2008. In 2000, we were in the same class for Airman leadership School at Offutt Air Force Base, Nebraska. She was also in my study group consisting of four students. This same study group often studied and rehearsed speeches in my house. I also deployed with her on reconnaissance missions with the Cobra Ball rapidly deployable aircraft, which flies Joint Chiefs of Staff-directed missions of national priority to collect optical and electronic data on ballistic targets. Due to the sensitivity of the operation, I still can’t say exactly what we were doing on those specific missions, but, she was in the plane with direct access to Top Secret Information as it came in. Monica separated from the Air Force in 2008 and then worked for the Department of Defense in a counterintelligence capacity until 2010.
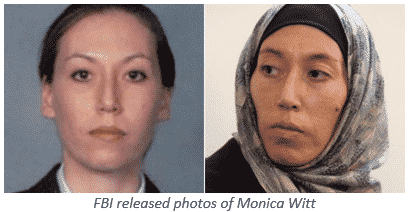
In 2012, she went to Iran for a New Horizon Organization convention where she was recruited by Iranian agents. In 2013, she defected and provided the Islamic republic with assistance and intelligence stemming from her work with the US government. Earlier this year, she was indicted by a federal grand jury in the District of Columbia for conspiracy to deliver national defense information to representatives of the Iranian government and declared a fugitive. This information was key to specific cyberespionage operation targeting U.S. intelligence officers, many of which were her prior colleagues. Thankfully, I was not a victim of those attacks. Monica Witt is the textbook example of an extremely dangerous insider threat.
How can small businesses detect insider threats?
The human factor continues to be the biggest menace to a hardened cybersecurity posture. According to a 2018 data breach report by SecurityMagazine 93% of all the data breaches could be traced back to an employee. Most attacks are results of employees making simple mistakes like falling for phishing attempts, using malware-laden USB storage devices on work computers, sharing credentials, or visiting malicious websites. The deliberate insider threats such Monica Witt’s espionage effort can be the most damaging to an organization’s data integrity. There are specific safeguards that can be put in place to help prevent these attacks.
1) Empower Employees
The first and last lines of defense are the employees who access sensitive data on a regular basis. Encourage the proper mindset, best practices, and promote vigilance. For example, email is where employees make the most cybersecurity mistakes. In this case, boost strategies like double-checking with any user who sends them a link or attachment and never sending sensitive information through unencrypted email. Furthermore, encourage use of strong passwords which they do not overuse or share with anyone. Embolden employees with the proper knowledge to identify and report a possible insider threat. For example, an employee suddenly starting to work extra time on-premises or logging in at odd hours or on weekends can indicate something dubious. Another example, an employee frequently roaming around areas that have nothing to do with his or her work or copying sensitive business information can also raise red flags.
2) Evaluate New Hires
Doing a thorough background check is essential. If there is something in a potential employee’s past that raises red flags, it could compromise their ability to protect an organization’s sensitive data at risk. For example, what if an employee is hired who has a history of getting fired from previous positions for being the cause of massive data breaches or a criminal history. Background checks are a crucial defense against these kinds of embarrassments, which is why total confidence is needed in a new hire.
3) Establish Device Use Policies
Over two billion people around the world currently own a cell phone according to many estimates. The days of handing out a company pager or a Blackberry phone are long gone. It is a foregone conclusion employees are using their privately-owned devices for work purposes on daily basis. In this case, a clear and concise Bring Your Own Device (BYOD) policy is essential. Key points of this policy should include are what devices are permitted to handle company data, what devices can be connected to a company workstation (NONE is the best answer here), what apps will be allowed or banned, and clear distinction who owns what apps and data on all BYOD devices. The essential principal in a BYOD policy is to attain the most stringent accountability of all sensitive data in an organization.
There are many other strategies to help defend Insider threats beyond what is listed here. The three key principals of “empower employees, evaluate new hires, and establish device use policies” should be three major pillars to any organization’s cybersecurity posture. During my Air Force career, I routinely broadened and reinforced my cybersecurity awareness mindset through annual training (CDSE course) and intelligence briefings. Even then, I never imagined my old classmate, Monica Witt would defect to Iran and commit cyberespionage. It’s near impossible to stop everyone, especially those who were as shrewd as she was. The best thing we can do is continue to educate ourselves and be vigilant. The more people get empowered with cybersecurity awareness, the less chance the adversaries have.
–Matt Nece
Cybersecurity Engineer



