Securing Critical Infrastructure
In 2011, hackers infiltrated US water treatment systems, resulting in physical infrastructure damage and thousands of homes being left without water.
In 2012, DHS reported that cyber attacks against power and nuclear systems grew by a staggering 52%.
In 2013, the United States took action. The Obama Administration introduced Executive Order 13636, “Improving Critical Infrastructure Cybersecurity”. The order instructed National Institutes of Standards and Technology (NIST) to work with industry partners to develop a shared framework for addressing cybersecurity concerns. After extensive collaboration and discussion, the NIST Cybersecurity Framework was unveiled.
What is the NIST Cybersecurity Framework?
The NIST Cybersecurity Framework is voluntary guidance designed to protect critical infrastructure, a term which applies to energy, water, transportation, healthcare, agriculture, dams, emergency services, and other essential systems. As you might imagine, these unique industries inhabit vastly different information security environments. One of the crowning achievements of the NIST CSF was to distill cybersecurity best practices into a set of core, essential security practices that could be applied to any organization, regardless of industry.
These practices are called the Framework Core, which revolves around five universal functions: Identify your assets and the risks facing them, Protect your information systems, Detect any suspicious activity, Respond appropriately to security events, and Recover from any system disruption. These essential cybersecurity functions apply equally to every organization.
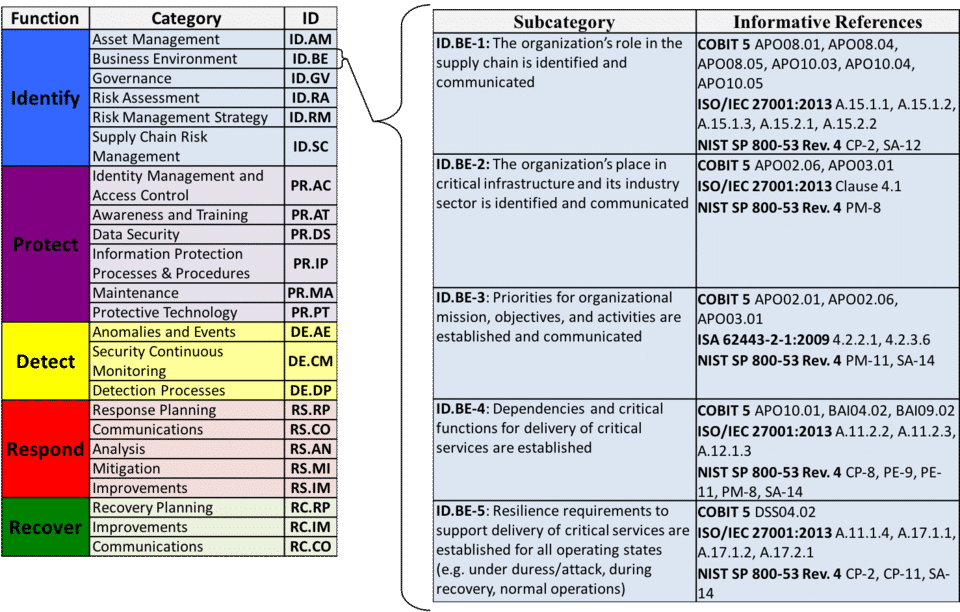
Those five functions are then broken down into categories. For example, take a look at the yellow section in the graphic. To detect suspicious activity, you need to track ‘Anomalies and Events’, practice ‘Security Continuous Monitoring’, and develop robust ‘Detection Processes’.
The categories in turn are broken down into subcategories. Wherever you see the word ‘subcategory’ in NIST CSF, think “something my organization should be doing” or an Action Item for the organization’s cybersecurity program. If you’re already compliant, great! Where that is not the case, the ‘Informative References’ lists cybersecurity guidance that can help. The documents listed there range from free US government guidance like the NIST Special Publications 800-series to the globally recognized ISO 27000 series.
How to Use the NIST Cybersecurity Framework
The NIST CSF was designed to protect critical infrastructure, but NIST has been very clear that small-to-medium businesses are welcome to use the framework. In fact, because the framework is written with simple, non-technical language, it may be ideal for companies just starting their own security programs. If your organization is interested in using the NIST CSF, consider starting with the following steps:
- Explore the educational resources that NIST has The sections for New Users and Online Learning will help you get off to a smooth start. In fact, if you are a Federal government contractor required to implement NIST 800-171 to protect Controlled Unclassified Information (CUI), NIST provides examples of successful integration of the CSF and 800-171.
- Use the framework to assess your organization’s security program. Combine the results of this internal assessment with your organization’s risk appetite and threat Together, this forms your Current Cybersecurity Framework Profile.
- Examine your Current Profile Based on your organization’s tolerance for risk and the known threats, have you implemented an appropriate amount of security controls? If not, start developing an optimized, ideal CSF Profile: this will be your Target Profile. It will help you track the priorities needed to achieve your desired security posture.
As you explore the CSF and begin applying it to your own company, contact us with any questions you may have. With over a decade of experience implementing NIST security frameworks, we’re ready to help you develop a robust security plan tailored to your company’s operating environment, threats, and risk tolerance. No problem is too big and no question is too small– our cybersecurity consultants are here to help!



