What is DFARS Cybersecurity Requirement?
The DoD created the DFARS Cybersecurity Requirement because our precious military secrets are actively being stolen by US adversaries. These secrets are our competitive advantage that helps the US maintain the most powerful military in the world, defending the best ideas in the world: representative democracy governing a capitalist marketplace. The US Department of Defense (DoD) classifies some of its information formally as SECRET or TOP SECRET and takes significant measures to protect this information. Other information is less sensitive, but still confidential and worthy of protection. The DoD allows its contractors to process much of this less sensitive—but still important—information in their internal IT networks. The adversaries know this, and increasingly target contractors to steal DoD secrets. Thus, DoD contractors are a major source of information leakage that leads to compromise of US military competitive advantage. The DoD has decided to do something to plug those leaks.
Through a regulation called the DFARS (DoD Federal Acquisition Regulation Supplement), which all DoD contractors must abide, contractors that process certain types of sensitive information for the DoD are expected to safeguard that information. This information is called Covered Defense Information (CDI), which is a subset of Controlled Unclassified Information (CUI) and contractors that don’t protect it stand to lose existing contracts and access to bidding on future contracts.
DFARS Cybersecurity Requirements
The DFARS cybersecurity requirement includes two main regulations: They are to provide “adequate security” to protect CDI in the contractor’s IT system and be able to identify cybersecurity incidents, report them to the DoD.
- Provide “adequate security” to protect CDI in the contractor’s IT system. Adequate security is provided by configuring your system according the safeguards listed in the National Institutes of Standards and Technology (NIST) Special Publication (SP) 800-171, Protecting Controlled Unclassified Information in Nonfederal Systems and Organizations. we’ll talk more about 800-171 shortly.
- Be able to identify cybersecurity incidents, report them to the DoD, and maintain incident related information for at least 90 days. We’ll talk about incidents and reporting in week 4 of this class.
NIST 800-171 Controls
Currently the DFARS Cybersecurity Requirement includes two parallel programs, CMMC and the DAM, both of which are nested in the NIST SP 800-171 requirement . The DFARS cybersecurity requirement is a list of things your organization must do to secure your IT system. By “your IT system” I mean:
- All of the IT components that process CDI, including workstations, laptops, servers, printers, routers, WiFi spots, firewalls, cloud services, vendor portals, etc.
- The policies and processes that govern how those IT components function
- The people that use those components and interact with CDI—the users
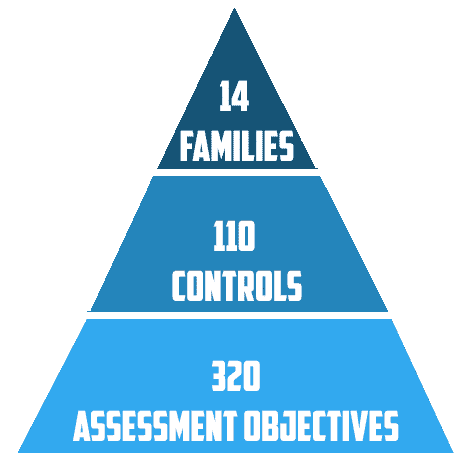
As of this writing, 800-171 has 110 “controls”. Control is another word for safeguard—a thing you must do to protect information. You can think of these controls as high-level requirements for the organization, just like at a high-level your organization is required to pay taxes and social security contributions for employees. There are several ways to pay those taxes, and there are multiple ways to meet the 800-171 controls.
The 800-171 controls are broken into fourteen (14) families, or groups of related controls. Let’s look at an example control. Control 3.1.8[1] says the organization must:
Unsuccessful logon attempts are when we put in the wrong username and/or password. This can happen for lots of reasons, but adversaries will most certainly cause many unsuccessful attempts as they try combinations of common usernames and passwords to gain access to the system. This type of “brute force” attack can be thwarted by implementing a control like 3.1.8. NIST provides a “Discussion” to attempt to explain the rational of this control in 800-171. Here’s the Discussion for 3.1.8:
You can see this DFARS Cybersecurity Control provides some supplemental guidance, but it doesn’t tell you what your organization needs to do. It doesn’t tell you how to implement or prove compliance in an audit. NIST does provide, however, in the 800-171 companion document 800-171A, some help for what your organization actually needs to do to ensure the control is integrated into your environment. This help comes in the form of what NIST calls “Assessment Objectives”, i.e. what an auditor would look for to determine if the control has been properly implemented. Just like an IRS auditor would ask for receipts as proof of expenses, a DFARS cybersecurity auditor will ask you to prove how you meet the controls. You can think of these objectives as Actions the organization must take to effectively implement the control. In fact, at Totem.Tech, we refer to Assessment
Objectives as “Organizational Actions”. The Assessment Objectives for control 3.1.8 are:
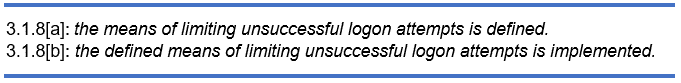
So NIST is telling us that to limit the unsuccessful logon attempts, we must define a means of limitation and then configure the system to engage those limiting means. Kind of circular, perhaps. Some controls have associated Assessment Objectives that are better than others at explaining how to implement them. Your best bet is to consult with a cybersecurity expert if you are not confident interpreting the controls.
In the case of 3.1.8, if your organization uses Windows workstations, limiting unsuccessful logon attempts is as simple as configuring a local Windows security policy setting, or using Windows Group Policy to push the configuration out to all workstations in your domain. It should be noted that any component that has a logon feature and that processes CDI must have a similar limitation on unsuccessful logon attempts. So if, for instance, you use cloud-based file sharing systems like Citrix ShareFile or Microsoft Office 365, these components need to have similar settings configured.
Some controls require technological configurations like 3.1.8, while others require a policy definition. Many of the controls, when coupled with their Assessment Objectives, require a mix of policy and technology to fully implement the safeguard. For instance, control 3.14.5, in the System and Information Integrity family, requires the organization to “Perform periodic scans of organizational systems and real-time scans of files from external sources as files are downloaded, opened, or executed.” Essentially, the organization must run antivirus software, and that software must be used regularly. The Assessment Objectives for this DFARS Cybersecurity Requirement needs both a policy definition and a technical apparatus to enforce that policy:
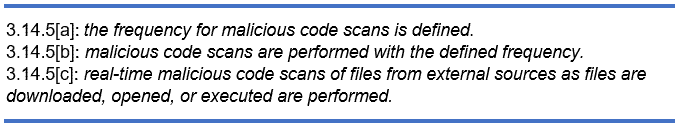
The organization must define how often the antivirus software runs scans (policy), and then configure the antivirus to scan according to the policy (technology). When we tally them all up, there are 320 Assessment Objectives[2] across the 14 families of 110 controls in the DFARS Cybersecurity Requirement.
The 14 families range across a broad spectrum of safeguards an organization must take to protect CDI. The control families require your organization to secure the technological, operational, and managerial aspects of your IT system that processes, stores, or transmits CDI.
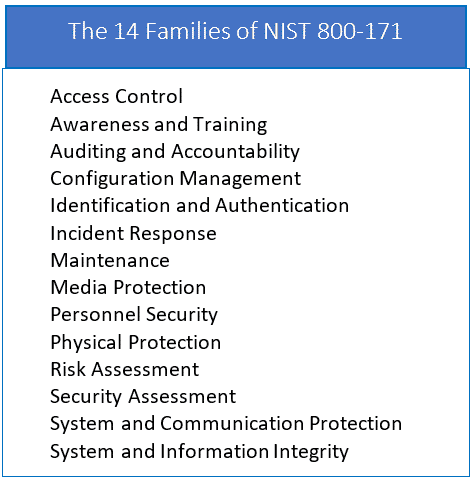
Your organization is also required to do things like perform background checks on employees that process CDI, and to adequately train employees in the safeguards they are expected to maintain. There are also controls that cover the protection of the physical facilities and buildings that house and support your IT system. There are also requirements to periodically ascertain vulnerabilities in your system and categorize the risk those vulnerabilities represent to the system and the CDI it contains.
DFARS Cybersecurity Requirement Includes: System Security Plan, Corrective Action Plans, and Plan of Action & Milestones
Implementing all these DFARS Cybersecurity Requirements means your organization has to develop a robust and mature cybersecurity program. To develop the program, the organization must do the following:
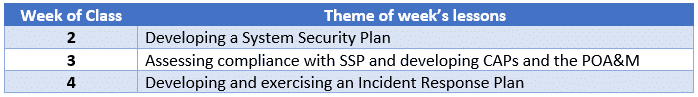
- Develop a System Security Plan (SSP) outlining the implementation details—both policy and technical—for each of the 110 controls
- Assess the current state of implementation of the SSP against the 800-171 standard
- Develop Corrective Action Plans (CAP) to close gaps between current implementation state and the SSP, and manage these CAPs in a Plan of Action and Milestones (POA&M)
- Develop and exercise an Incident Response Plan
In our online DFARS online workshop, we’ll explore more in depth each of these four things your organization must do:
For now, it’s important for you to understand the DFARS exists, that DoD contractors must abide by it, and that it calls out a set of safeguards that contractors must build into their system. Those safeguards are listed in the 800-171 document from NIST.
To determine if your organization processes CUI, and whether or not every DoD contractor needs to comply to the DFARS Cybersecurity Requirements, we encourage you to enroll in our DFARS/NIST 800-171/CMMC workshop.
Good Hunting!
–Adam Austin
Cybersecurity Lead

