Most small business Department of Defense (DoD) contractors do not have the resources to hire a full-time IT staff, which is why we typically look to outsource this capability to an IT Managed Service Provider (MSP). MSPs do the “day to day” IT stuff, like managing user accounts and maintaining workstations and servers. This means that IT MSPs are being trusted with administering technologies, tools, and processes which come into contact with sensitive information, such as Controlled Unclassified Information (CUI), on a regular basis. Given this, not only do IT MSPs have a large part to play in helping their DoD contractor clients prepare for the Cybersecurity Maturity Model Certification (CMMC), but they themselves may also be bound to CMMC by virtue of the sensitive information they are helping administer. So, how should MSPs proceed? What level of care towards CMMC compliance do MSPs need to demonstrate? We’ll explore these questions in this post, and we will provide guidance on how MSPs can prepare for an assessment and be better equipped to assist their clients with CMMC.
We’ll preface this blog by clarifying that we are not an MSP, nor are we getting paid millions by one to write this blog (maybe someday…). We are just a fellow DoD contractor looking to share our experiences, frustrations, and successes with the Defense Industrial Base (DIB). So, you can expect us to remain “MSP-agnostic” in terms of the recommendations given in this post.
Overview of the current CMMC and MSP situation
Recall that the backbone for protecting CUI under CMMC is the NIST 800-171 framework. This framework outlines 110 controls – along with 320 “Organization Actions” (see NIST 800-171A) – which, along with an incident response capability, must be implemented in order to be compliant with the mandate, DFARS clause 252.204-7012. So, CMMC is how the DoD will hold us accountable to NIST 800-171 and enable us to continue doing business with the federal government.
Implementing NIST 800-171 is a significant burden to bear, especially for small businesses. It is expensive, and although it isn’t necessarily difficult to implement, it takes time – a long time – hence our frequent use of the term “journey” when describing preparation for CMMC. However, an IT MSP can take some of this pressure off their clients’ shoulders by “absorbing” some of these requirements. As we teach in our CMMC Workshops, roughly 51% of the NIST 800-171 Organization Actions can be partially or fully taken on by an MSP. So, in many ways, your MSP is going to put in just as much effort in getting you ready for CMMC as you will.
While a sizeable amount of your cybersecurity program could conceivably be outsourced to an MSP, not all of it can be. The establishment and ownership of your organization’s cybersecurity “culture” – the policies, expectations, and overall buy-in from company staff – must come from within. An MSP will not be able to provide you with this culture, and this accounts for a good portion of NIST 800-171.
Side note: we created a free MSP Shared Responsibility Checklist outlining the Organization Actions that your MSP can conceivably assist with, along with other helpful CMMC considerations for your MSP, which you can download at the end of this post.
Why should my MSP care about CMMC?
Contention within the DIB has reared its ugly head in recent years over whether or not our MSPs will themselves be required to receive a CMMC certification, given how heavily involved they are in the process. Thankfully, in December of 2021, the DoD released its CMMC Scoping Guide, which provides helpful clarification for nailing down our assessment scope, and it even addresses this particular point of contention. In the guide, the DoD identifies MSPs as a type of “External Service Provider” (ESP), and they state the following:
“An ESP can be within the scope of applicable CMMC practices if it meets CUI asset criteria."
OK, so what are the “CUI asset criteria”? Once again, we will refer to the Scoping Guide for clarification. Identified below are five different categories of CMMC assets:
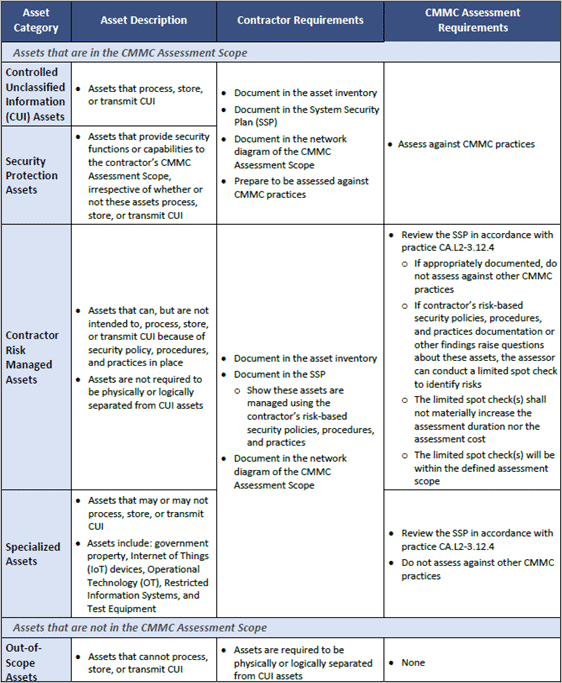
If your MSP is administering CUI Assets (the top category in the table above), assets that process, store, or transmit CUI, they will need a CMMC certification. Pretty clear-cut. Examples of CUI Assets could include your workstations or servers; systems that you have likely already tasked your MSP with managing. Also consider a file server with CUI documents being stored on it, and your MSP performs regular maintenance on the file server.
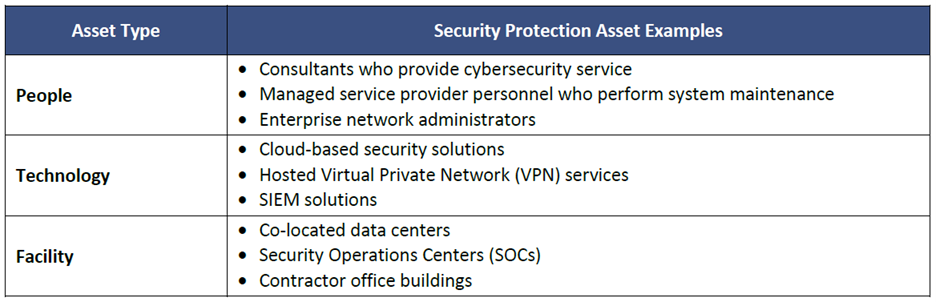
Now, the contention arises most frequently when considering the Security Protection Assets category. These assets are those which provide security functions or capabilities within the contractor’s assessment scope, and thus are required to conform to CMMC. For example, one of the most burdensome requirements for small businesses under NIST 800-171 is that of auditing and accountability – monitoring your environment and holding users accountable for their actions. Most small businesses outsource this capability to an MSP (or Managed Security Service Provider – MSSP), who may utilize a tool such as a security incident & event management (SIEM) to perform the event log and network traffic collection and analysis. Although the SIEM tool itself does not process, store, or transmit any CUI, it is being used to assist with meeting the CMMC requirements for protecting CUI, and thus, per the Scoping Guide, the administrator of the tool (the MSP) must conform to CMMC. The guide also includes some other examples of Security Protection Assets:
It may seem like a serious stretch at first for MSPs to have to receive a CMMC certification, but the reason for this requirement is that most of the tools utilized by your MSP (or other service providers) will likely require administrative access into your environment. The DoD is concerned with an adversary compromising the service provider and using their administrative power to gain access to your CUI. How can the MSP mitigate this risk? The DoD’s answer is to have them get CMMC-certified as well.
As of right now, if you only handle Federal Contract Information (FCI) but not CUI, then your MSP will still need a CMMC certification, but instead of Level 2, they will seek Level 1. Of course, this assumes that they have no other clients who handle CUI. Furthermore, some MSPs may even need to worry about CMMC Level 3, as small business clients that work on some high-value national security programs will target this level. On the other hand, most pursuing CMMC Level 3 are large prime contractors who will most likely have their own internal IT team.
Your MSP must be ready for CMMC
We cannot stress this enough: getting ready for CMMC takes a long time. When we approached our previous MSP with news that they will need to receive their own certification, they decided that they weren’t willing to take the journey with us, and we were “fired” as their clients. If you are working with an MSP, but you have not yet discussed CMMC with them, the time to do so is now. If you would like some help discussing these requirements with your MSP, just let us know. Even better, invite them to attend one of our DFARS/CMMC Workshops. Don’t wait until assessments begin to ensure your MSP is along for the ride.
Additionally, be sure to check out the free downloadable MSP Shared Responsibility Checklist at the end of this post and share it with your MSP. It highlights the NIST 800-171 Organization Actions that your MSP should be able to fully/partially assist with, and it also provides some helpful tools for how they can get started on their own CMMC journey. The CMMC Scoping Guide recommends that DoD contractors “evaluate [their] ESP’s shared responsibility matrix”, which should identify the security objectives that are being handled by the MSP and those that are being handled by the contractor. This resource can help get you started.
How Totem can help MSPs help their clients
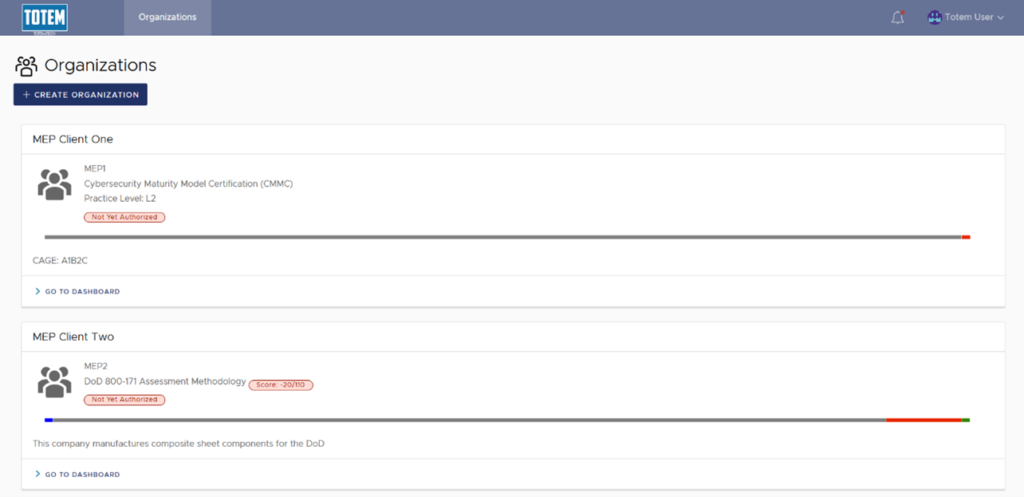
DoD contractors are relying heavily upon their MSP’s expertise and capabilities to help get them ready for CMMC. As such, it is crucial that MSPs have the right tool to manage their clients’ cybersecurity program components, including their System Security Plan (SSP), Plan of Action & Milestones (POA&M), and Incident Response Plan (IRP). This is a lot to keep track of, and it can easily get out of hand. If you are an MSP and looking for a tool to help your clients prepare for CMMC, we can help.
We built our Totem™ Cybersecurity Program Management tool with MSPs in mind. We offer an Enterprise package, where you will receive your own Totem™ instance and be able to manage all of your clients’ cybersecurity programs (including yours) in one place. Totem™ was designed to be affordable for small businesses pursuing CMMC compliance, and through the Enterprise package, MSPs can get their clients access to the tool at a significant discount. Contact us if this interests you.
Final thoughts
Well, there you have it: if you are an MSP, and you have administrative access into at least one client’s environment which processes, stores, or transmits CUI, you will need to begin preparing to receive a CMMC Level 2 certification. For clients with only FCI: CMMC Level 1. Welcome to the journey!
If you are unsure where to begin, grab a seat in one of our quarterly Workshops, where we explore the current DFARS/NIST/CMMC requirements in depth. Or, consider how you might leverage our Totem™ tool to continue assisting your clients with CMMC. Feel free to drop us a line if you just want to chat – we love talking about all this stuff!
Keep fighting the good fight!
–Nathan Cross, Cybersecurity Engineer
Download our free MSP Shared Responsibility Checklist!


