
Is BYOD allowed for CMMC compliance?
What a loaded question. Buckle up, folks… this could get spicy. When looking to meet the Cybersecurity Maturity Model Certification (CMMC) requirements, many Department of

What a loaded question. Buckle up, folks… this could get spicy. When looking to meet the Cybersecurity Maturity Model Certification (CMMC) requirements, many Department of
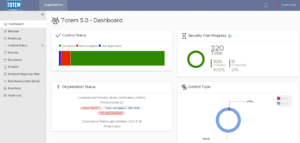
Totem Technologies is thrilled to share the release of our biggest software upgrade to date, Version 5.0 of our Totem™ Cybersecurity Compliance Management tool! Packed

This is the million-dollar question for Defense Industrial Base (DIB) members, isn’t it? Totem has many clients that do not appear to handle (store, process,

Microsoft. When you hear this word, what goes through your mind? Is it joy? Perhaps frustration? Maybe it’s robust features like Azure. What about Azure Virtual

Why I chose Totem Tech I am currently a sophomore attending Brigham Young University (BYU) and a declared cybersecurity major. Early this year, like many
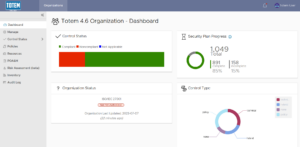
Totem Technologies is excited to share the latest features and updates now included in version 4.6 of our Totem™ Cybersecurity Compliance Management tool! Significant updates

For Department of Defense (DoD) contractors and subcontractors pursuing compliance with the Cybersecurity Maturity Model Certification (CMMC), few controls have been as challenging (and costly)

Over the past five years, we’ve helped over a thousand small business Defense Industrial Base (DIB) manufacturers meet their obligations to secure Federal Contract Information

Small businesses are the backbone of the United States economy, as they comprise upwards of 99% of all businesses. Given the sheer number of small

(385) 492-3405

Copyright © 2024 Totem Technologies, LLC
All rights reserved. Privacy Policy.