How to Address the Totem Top 5 Cybersecurity Safeguards in NIST 800-171 and the CMMC
Introduction and Revisiting the Top 5 Cybersecurity Safeguards
The CMMC includes a high number of cybersecurity safeguards that contractors need to implement and most have no idea where to start. In our Totem Top 5 blog, we identify the top 5 safeguards an organization should put in place to kick off a cybersecurity program. The Top 5 is essentially a curation of the “top” cybersecurity safeguard lists from three of the most well-respected cybersecurity organizations:
- The United States National Security Agency (NSA) “Top 10 Mitigations”
- The Australian Cyber Security Centre (ACSC) “Essential Eight”
- The Centers for Internet Security (CIS) “Basic Six”
We weight-ranked the top safeguards from each of these organizations and added in a little of our own dash of flavor with best practices we know have been important for us as a small business. At the end of this article you can download a CMMC compliance checklist to start implementing these top 5 cybersecurity safeguards.
The result is the Totem Top 5:
| Rank | Safeguard |
|---|---|
| 1 | Know Your Assets |
| 2 | Train Your Users |
| 3 | Patch Software and Operating Systems |
| 4 | Restrict Administrative Privileges |
| 5 (tie) | Harden System Components |
| 5 (tie) | Whitelist Software |
Inclusion of Software Whitelisting in the Top 5
You probably noticed the addition of “Whitelist Software” in this revisited Top 5. Our ranking in the original blog was done with napkin math; for this go round we used state-of-the-art statistical tools—an Excel spreadsheet—to do the weighted rankings, and found there was a tie between “Harden System Components” and “Whitelist Software,” so we included it here.
Whitelisting Software (aka “Application Control”) requires defining precisely what software will be allowed to run on an operating system (OS), and then configuring an application on the OS explicitly only to allow that defined software to execute. Windows OS has a native whitelisting application called AppLocker. There are other 3rd party applications, such as McAfee Application Control, that can be installed and engaged as well.
Software Whitelisting is a very effective tool to prevent the execution of malware on a system. In our original blog we evaluated the effectiveness of each of the Top 5 against a real-life phishing scenario we faced. In this scenario we received a phishing email with a malicious Microsoft Word document attached. The adversary’s attack—ultimately thwarted by us—aimed to take advantage of an unpatched Word installation to execute a command to download and install a keylogger. A properly configured software whitelist would have completely prevented the installation of the keylogger, adding yet another layer to our defense-in-depth.
Why Start with the Totem Top 5 Cybersecurity Safeguards for NIST 800-171 / CMMC Compliance?
To do business with the US Department of Defense (DoD), contractors and DoD supply chain members will have to implement many safeguards to protect the DoD’s Controlled Unclassified Information (CUI) processed, stored, and/or transmitted by contractor-owned IT systems. The National Institutes of Standards and Technology (NIST) 800-171 standards list many of those required safeguards, and these standards are incorporated and expanded upon by the DoD Cybersecurity Maturity Model Certification (CMMC).
Contractors and suppliers that want to do business with the DoD must obtain a CMMC certification to propose to or execute DoD contracts. Essentially the CMMC certification is a supply chain member’s “license to operate” with the DoD. For the hundreds of thousands of small business in the DoD’s supply chain, obtaining a CMMC certification is an extremely important milestone. For many of us, that milestone can seem like it’s on a distant horizon, or even worse, a mirage.
Mr. Jeff Dalton, one of the CMMC Accreditation Body board members, posted on LinkedIn that, philosophically, supply chain members shouldn’t worry about “passing” a CMMC assessment, but should instead concentrate on building a cybersecurity program that bests protects CUI, and this approach will naturally result in a certification. The Totem Top 5 is the perfect path to start building a cybersecurity program to best protect any data, so you may want to start there. Let’s explore how the Top 5 align with the 800-171 Controls and CMMC Practices.
The table below shows each of the Totem Top 5 and the associated 800-171 Controls / CMMC Practices (download the Totem Top 5 cybersecurity safeguards CMMC compliance checklist at end of this article):
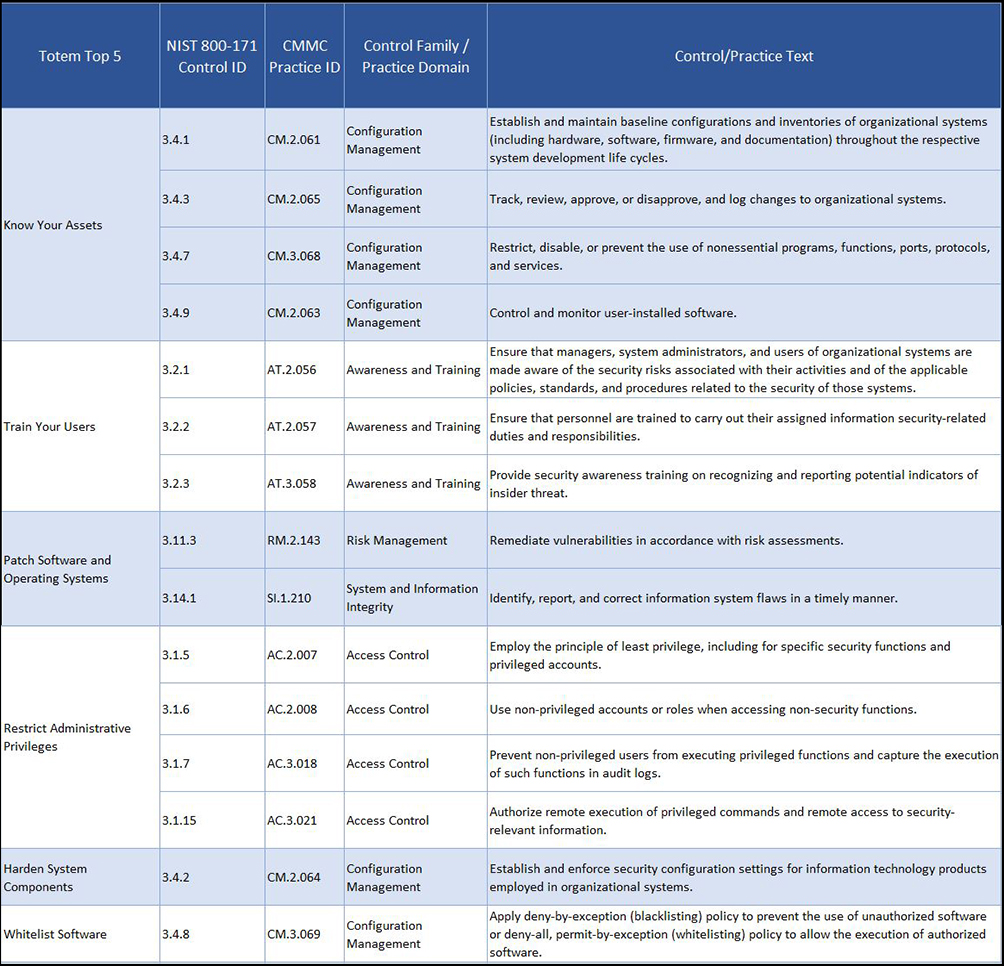
As you can see, the Totem Top 5 encompasses 15 controls in the NIST 800-171 and CMMC. And most of the Configuration Management family/domain is included in this list, aligning nicely with our assertion that cybersecurity starts and ends with configuration management. It is also interesting to note that only one of these 15 controls/practices is included in the FAR 17 or CMMC Level 1: “Identify, report, and correct information system flaws in a timely manner,” which is associated with our Top 5 “Patch Software and Operating Systems.”
If you are struggling with where to begin in the development of your organization’s cybersecurity program, you have a couple of possible routes:
- begin with the FAR 17 Controls and immediately move toward compliance with CMMC Level 1
- begin with the 15 Controls associated with the Totem Top 5 and immediately move toward best protecting CUI
Either route you choose puts you on a good path to compliance and passing the CMMC.
Free Download - Totem Top 5 Cybersecurity Safeguards CMMC Compliance Checklist
If you’d like to use the Totem Top 5 as your guidepost to start working towards your CMMC compliance, fill out the following form and we will email you our Totem Top 5 CMMC compliance checklist.

