The Emergence of the Internet of Things (IoT)
New concepts or inventions can be scary at times. Fire can be a danger to living organisms, space can be full of dangerous unknowns, and IoT devices can be a danger for credentials. With these dangers in mind, why do we continue to utilize these products? New frontiers have that sort of effect on people for a plethora of reasons, including the ill-studied nature of the idea. As for the “Internet of Things”(IoT), the main idea behind it is to make living easier through automation. These devices may be the next step in our cyber evolution, but the necessity for constant network connection and transport of credentials are causing some controversy. The average person who just wants to make life easier may consider IoT to be as good as or even better than sliced bread, but the information security community has a few recurring qualms.
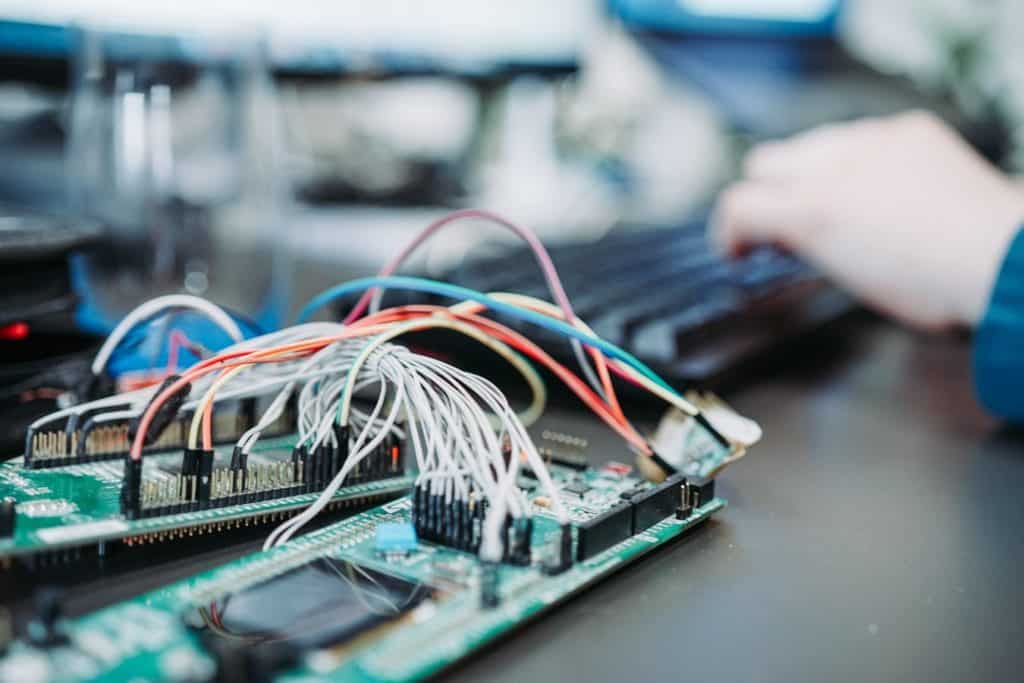
How to Secure Development of IoT
Before sending a brand-new device out to the public for use, it’s integral for software and hardware developers to implement security since they send, receive, and possibly even contain personally identifiable information (PII). A great source for a short-and-sweet article regarding cyber security implementation is Chris Romeo’s “How to put the S (for security) into your IoT development”. This includes the following:
- Robust authentication mechanisms like multi-factor authentication (MFA)
- Utilizing industry-standard encryption methods
- Automatic software patching over encrypted channels
- Securing web-apps. that are part of the IoT platform
Albeit these measures will increase security for IoT, it is possible that developers may have overlooked something or missed a step. However, that’s where the consumers come in.
Consumers assessing the security of IoT
If the developers continue to push updates to the devices, it is up to the consumer to download and install the updates on a regular basis i.e. patching. However, if the developers had missed something, one of the best ways to help is to do some white hat work by analyzing the device then submitting vulnerabilities found, a process called bug hunting. For instance, there was a talk during DEFCON 27 by Jmaxxz called “Your Car is My Car” on automotive cybersecurity, with the focus being a remote-start device he had bought for his girlfriend. He demonstrated how he could start and ultimately steal a vehicle by utilizing the intercepted data that was transferred between the remote-start device and the car itself. The unencrypted data that was intercepted had allowed him to gain administrative control of his vehicle’s ignition and current geographic location. After this discovery, Jmaxxz contacted the company as soon as he could to let them know what the issue was and left them to fix the vulnerabilities that he found.
Configuration Management an important security step for IoT
Attending this talk had aroused thoughts regarding the significance of configuration management in the workplace—check out Adam Austin’s blog for his insights on this topic. It is quite easy to add IoT devices into a small business corporate network without much thought. We at Totem.Tech highly discourage employees internally and externally from doing so because of situations like the one portrayed by Jmaxxz. When these devices are neglected and users forget to execute patching, IoT devices become an easy target to establish a persistent foothold for an adversary. Furthermore, IoT devices that are breached on corporate networks allow the adversary to pivot laterally to discover, and compromise more valuable assets like workstations and servers. We at Totem.Tech utilize Nmap to scan our corporate networks to try to find IoT devices that might have been accidentally connected by our users. If your users desire IoT devices in the office, we highly recommend creating a DMZ e.g. a network utilized only for facility/office guests dedicated for hosting devices which should never be on the corporate network. We also recommend mentioning IoT devices in your annual internal cybersecurity training to highlight the cybersecurity risks of utilizing such devices in the workplace.
Securing the Internet of Things for Future Utilization and Enjoyment
An integral part of the security community is to be the white hat to help developers and ensure a more secure system overall. Per the CIA triad, this will increase the confidentiality piece as well as the integrity piece with accessibility only being affected in terms of how fast the content travels to-and-from the device. Rather than beating the dead horse “IoT devices are bad,” there should be a stronger focus on finding a way to better secure IoT devices. We added regulations on fire construction and space navigation for safety reasons. Hence with IoT on the rise, it is imperative to improve by applying security proactively and reporting remaining issues today for a more secure tomorrow.
–Miguel Vara
Cybersecurity Technician