Update 5/25/2022: CMMC has evolved since the release of this blog. We recommend you read up on our latest blogs or grab a seat in one of our Workshops to stay up to date on the latest with CMMC.
One of the biggest changes to the DFARS 7012 for cybersecurity compliance in the Cybersecurity Maturity Model Certification (CMMC) is contractors no longer being able to self-attest that they meet these two main cybersecurity requirements:
DFARS Requirements
- Provide “adequate security” for CUI in the contractor internal information systems, by implementing the National Institutes of Standards and Technology (NIST) 800-171 cybersecurity controls (safeguards)
- The ability to recognize and report cybersecurity incidents to the DoD via a special online portal
To be clear: DFARS 7012 is a good thing, as our adversaries for too long have targeted DoD contractors—the weakest link in the DoD supply chain—to steal our precious military secrets. Not sure what the cybersecurity requirements are for contracting? You can read about the NIST 800-171 Contract Clause here.
However, the winds are changing, and contractors are starting to be held accountable by the DoD for these attestations with the Cybersecurity Maturity Model Certification (CMMC). In January 2019, Undersecretary of Defense for Acquisition, Ms. Ellen Lord, released a memo directing the Defense Contractor Management Agency (DCMA) to begin validating and verifying (V&V) contractor implementations of the DFARS 7012 requirements.
At a fantastic USC/Northrop Grumman 800-171 workshop in early July in Grand Forks, ND, the Northrop Grumman presenter indicated his organization, in consortium with several other large DoD prime contractors, had indeed begun the validation and verification process with reps from DCMA. The DCMA is doing a sort of “proof-of-concept” audit with the large primes, and then will be targeting smaller primes and subcontractors in the future. The bottom line: it’s time for all DoD contractors, prime or sub, to get ready for upcoming Cybersecurity Maturity Model Certification audits of their internal IT processes.
Katie Arrington and the Cybersecurity Maturity Model Certification (CMMC)
In May 2019 the DoD announced even broader changes to contractor cybersecurity accountability. Katie Arrington of the Undersecretary’s office presented a notional concept of a DoD-sponsored Cybersecurity Maturity Model Certification (CMMC) for DoD contractors. The CMMC is scheduled to be rolled out in phases in 2020, replete with an assessment tool independent third-party auditors will use to evaluate contractors’ implementation of DFARS 7012.
Here summary of the Cybersecurity Maturity Model Certification (CMMC) as Ms. Arrington presented them
- The DoD is working with John Hopkins University Applied Physics Laboratory (APL) and Carnegie Mellon University Software Engineering Institute (SEI) to review and combine various cybersecurity standards into one unified standard and maturity model for cybersecurity, the CMMC.
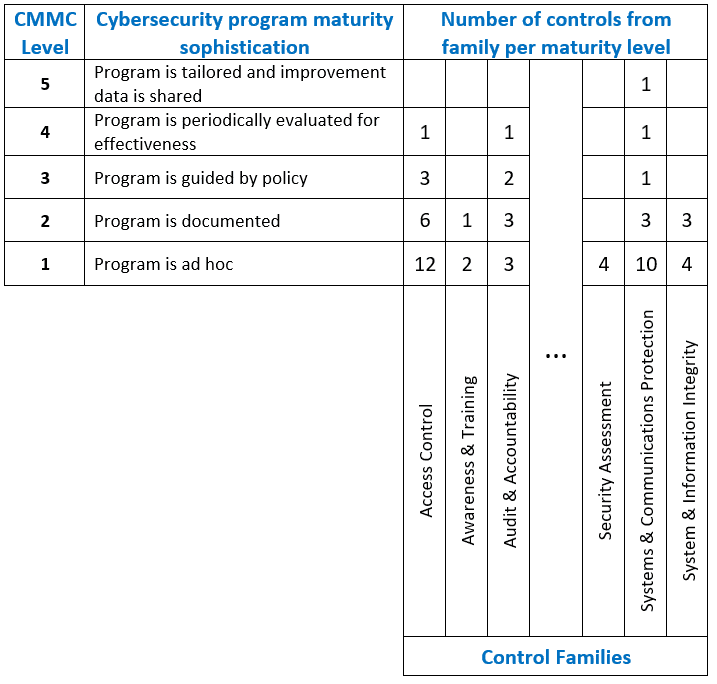
- The Cybersecurity Maturity Model Certification levels will range from basic hygiene to “State-of-the-Art”.
- The required Cybersecurity Maturity Model Certification level (notionally between 1 – 5) for a specific contract will be contained in the RFP sections L & M, and will be a “go/no-go decision”.
- The Cybersecurity Maturity Model Certification framework must be semi-automated and, more importantly, cost effective enough so that Small Businesses can achieve the minimum Cybersecurity Maturity Model Certification level of 1.
- A neutral 3rd party will maintain the Cybersecurity Maturity Model Certification for the DoD.
Ms. Arrington’s presentation went on to explain that the Cybersecurity Maturity Model Certification framework will integrate cybersecurity controls and safeguards from multiple standards, including the NIST 800-171, ISO 27001, CMMI, etc.
Currently NIST 800-171 is the control set we are required to use, and our Totem™ cybersecurity planning tool is the best lightweight security planning tool available for DoD contractors. The tool adapts for all DFARS 7012 compliance including breaking down the Cybersecurity Maturity Model Certification levels.
It appears that Cybersecurity Maturity Model Certification (CMMC) may shift to requiring cybersecurity “capabilities”, which are roll-ups of individual controls. As notionally described, the 800-171 controls or capabilities will be divvied up among the Cybersecurity Maturity Model Certification levels, so to meet Cybersecurity Maturity Model Certification Level 1, an organization would only have to be compliant with, say, 50 of the 110 800-171 controls/capabilities. Cybersecurity Maturity Model Certification Level 5 would require implementation of all 110 controls/capabilities. In fact, Northrop Grumman has been requiring a similar Cybersecurity Maturity level attestation of its subcontractors via its Supplier Security Assessment Questionnaire since at least 2016, so some of you may be familiar with this concept.
Below is a graphical depiction:
Notional Cybersecurity Maturity Model Certification Levels
and Associated Controls
It’s time your organization adjusts sail to deal with these compliance wind changes, because they are shifting rapidly. If you want to learn more about the current DFARS/NIST 800-171/CMMC landscape, or how you can create a CMMC-compliant cybersecurity program, grab a seat in one of our Workshops. Or, drop us a line; we love talking about all this stuff!
-Adam Austin
Cybersecurity Lead