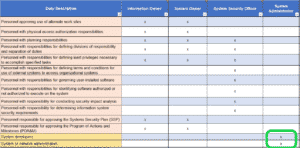
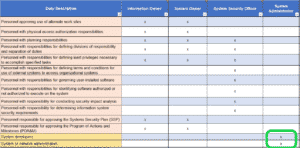
Why is separation of duties required by NIST 800-171 and CMMC?
Background on the CMMC requirement to separate the duties of individuals Members of the DoD supply chain – the Defense Industrial Base (DIB) — that
Background on the CMMC requirement to separate the duties of individuals Members of the DoD supply chain – the Defense Industrial Base (DIB) — that

If your company is a member of the Department of Defense (DoD) Industrial Base (DIB), it is very likely that you are already familiar with

What if we told you that starting the path towards CMMC compliance doesn’t require thousands of dollars in shiny new hardware? Introduction & Totem Top

The Cybersecurity Maturity Model Certification (CMMC) was designed to improve the security posture of the Defense Industrial Base. In developing the framework, Pentagon officials drew

Totem Technologies’ Small Business CMMC Preparation Methodology This post describes Totem Technologies’ (Totem.Tech) three-phased approach and methodology to achieve CMMC Certification. We follow this Methodology

What the heck are processes acting on behalf of authorized users? Excellent question, especially since NIST SP 800-171 and CMMC discussion, guidance, examples, and “clarification”

History of Cyber Crime Cybercriminals are increasingly embracing a service-based economy. In the past, a cybercriminal had to be a skilled hacker, able to carry

Introduction to Phishing Attacks Phishing attacks are some of the most common cyberattacks in existence. Almost a third of data breaches involved phishing in 2019,

Multi-Factor Authentication for Small Business: Is It Worth the Price? Hacking is a business, after all, and most hackers make their living picking off easy

(385) 492-3405

Copyright © 2024 Totem Technologies, LLC
All rights reserved. Privacy Policy.